committed by
 GitHub
GitHub
Не найден GPG ключ соответствующий данной подписи
Идентификатор GPG ключа: 4AEE18F83AFDEB23
100 измененных файлов: 1493 добавлений и 3495 удалений
-
+59 -0CHANGELOG.md
-
+4 -0README.md
-
+2 -2docs/alternative-architectures.md
-
Двоичные данныеdocs/assets/obtain_admin_access_token_element.png
-
+0 -39docs/configuring-awx-system.md
-
+3 -0docs/configuring-dns.md
-
+69 -0docs/configuring-playbook-backup-borg.md
-
+75 -0docs/configuring-playbook-bot-buscarron.md
-
+72 -0docs/configuring-playbook-bot-matrix-registration-bot.md
-
+6 -6docs/configuring-playbook-bridge-hookshot.md
-
+15 -0docs/configuring-playbook-bridge-mautrix-telegram.md
-
+3 -0docs/configuring-playbook-postgres-backup.md
-
+11 -0docs/configuring-playbook.md
-
+1 -1docs/faq.md
-
+1 -0docs/self-building.md
-
+126 -41group_vars/matrix_servers
-
+0 -8roles/matrix-awx/defaults/main.yml
-
+0 -29roles/matrix-awx/scripts/matrix_build_room_list.py
-
+0 -42roles/matrix-awx/surveys/access_export.json.j2
-
+0 -18roles/matrix-awx/surveys/backup_server.json.j2
-
+0 -66roles/matrix-awx/surveys/bridge_discord_appservice.json.j2
-
+0 -88roles/matrix-awx/surveys/configure_corporal.json.j2
-
+0 -30roles/matrix-awx/surveys/configure_dimension.json.j2
-
+0 -114roles/matrix-awx/surveys/configure_element.json.j2
-
+0 -18roles/matrix-awx/surveys/configure_element_subdomain.json.j2
-
+0 -19roles/matrix-awx/surveys/configure_email_relay.json.j2
-
+0 -31roles/matrix-awx/surveys/configure_jitsi.json.j2
-
+0 -41roles/matrix-awx/surveys/configure_ma1sd.json.j2
-
+0 -29roles/matrix-awx/surveys/configure_mjolnir.json.j2
-
+0 -198roles/matrix-awx/surveys/configure_synapse.json.j2
-
+0 -18roles/matrix-awx/surveys/configure_synapse_admin.json.j2
-
+0 -54roles/matrix-awx/surveys/configure_website_access_export.json.j2
-
+0 -101roles/matrix-awx/tasks/backup_server.yml
-
+0 -58roles/matrix-awx/tasks/bridge_discord_appservice.yml
-
+0 -13roles/matrix-awx/tasks/cache_matrix_variables.yml
-
+0 -11roles/matrix-awx/tasks/create_session_token.yml
-
+0 -41roles/matrix-awx/tasks/create_user.yml
-
+0 -267roles/matrix-awx/tasks/customise_website_access_export.yml
-
+0 -10roles/matrix-awx/tasks/delete_session_token.yml
-
+0 -43roles/matrix-awx/tasks/export_server.yml
-
+0 -7roles/matrix-awx/tasks/import_awx.yml
-
+0 -16roles/matrix-awx/tasks/load_hosting_and_org_variables.yml
-
+0 -16roles/matrix-awx/tasks/load_matrix_variables.yml
-
+0 -234roles/matrix-awx/tasks/main.yml
-
+0 -14roles/matrix-awx/tasks/purge_database_events.yml
-
+0 -320roles/matrix-awx/tasks/purge_database_main.yml
-
+0 -14roles/matrix-awx/tasks/purge_database_no_local.yml
-
+0 -14roles/matrix-awx/tasks/purge_database_users.yml
-
+0 -19roles/matrix-awx/tasks/purge_media_local.yml
-
+0 -111roles/matrix-awx/tasks/purge_media_main.yml
-
+0 -19roles/matrix-awx/tasks/purge_media_remote.yml
-
+0 -25roles/matrix-awx/tasks/rotate_ssh.yml
-
+0 -108roles/matrix-awx/tasks/self_check.yml
-
+0 -243roles/matrix-awx/tasks/set_variables_corporal.yml
-
+0 -105roles/matrix-awx/tasks/set_variables_dimension.yml
-
+0 -180roles/matrix-awx/tasks/set_variables_element.yml
-
+0 -43roles/matrix-awx/tasks/set_variables_element_subdomain.yml
-
+0 -45roles/matrix-awx/tasks/set_variables_jitsi.yml
-
+0 -102roles/matrix-awx/tasks/set_variables_ma1sd.yml
-
+0 -44roles/matrix-awx/tasks/set_variables_mailer.yml
-
+0 -68roles/matrix-awx/tasks/set_variables_mjolnir.yml
-
+0 -223roles/matrix-awx/tasks/set_variables_synapse.yml
-
+0 -44roles/matrix-awx/tasks/set_variables_synapse_admin.yml
-
+0 -32roles/matrix-awx/tasks/update_variables.yml
-
+98 -0roles/matrix-backup-borg/defaults/main.yml
-
+4 -0roles/matrix-backup-borg/tasks/init.yml
-
+23 -0roles/matrix-backup-borg/tasks/main.yml
-
+112 -0roles/matrix-backup-borg/tasks/setup_install.yml
-
+41 -0roles/matrix-backup-borg/tasks/setup_uninstall.yml
-
+15 -0roles/matrix-backup-borg/tasks/validate_config.yml
-
+43 -0roles/matrix-backup-borg/templates/config.yaml.j2
-
+29 -0roles/matrix-backup-borg/templates/passwd.j2
-
+1 -0roles/matrix-backup-borg/templates/sshkey.j2
-
+58 -0roles/matrix-backup-borg/templates/systemd/matrix-backup-borg.service.j2
-
+10 -0roles/matrix-backup-borg/templates/systemd/matrix-backup-borg.timer.j2
-
+7 -0roles/matrix-base/defaults/main.yml
-
+96 -0roles/matrix-bot-buscarron/defaults/main.yml
-
+5 -0roles/matrix-bot-buscarron/tasks/init.yml
-
+23 -0roles/matrix-bot-buscarron/tasks/main.yml
-
+100 -0roles/matrix-bot-buscarron/tasks/setup_install.yml
-
+36 -0roles/matrix-bot-buscarron/tasks/setup_uninstall.yml
-
+9 -0roles/matrix-bot-buscarron/tasks/validate_config.yml
-
+19 -0roles/matrix-bot-buscarron/templates/env.j2
-
+39 -0roles/matrix-bot-buscarron/templates/systemd/matrix-bot-buscarron.service.j2
-
+4 -4roles/matrix-bot-go-neb/templates/systemd/matrix-bot-go-neb.service.j2
-
+10 -1roles/matrix-bot-honoroit/defaults/main.yml
-
+4 -0roles/matrix-bot-honoroit/tasks/setup_install.yml
-
+3 -0roles/matrix-bot-honoroit/templates/env.j2
-
+4 -4roles/matrix-bot-honoroit/templates/systemd/matrix-bot-honoroit.service.j2
-
+49 -0roles/matrix-bot-matrix-registration-bot/defaults/main.yml
-
+5 -0roles/matrix-bot-matrix-registration-bot/tasks/init.yml
-
+23 -0roles/matrix-bot-matrix-registration-bot/tasks/main.yml
-
+73 -0roles/matrix-bot-matrix-registration-bot/tasks/setup_install.yml
-
+36 -0roles/matrix-bot-matrix-registration-bot/tasks/setup_uninstall.yml
-
+10 -0roles/matrix-bot-matrix-registration-bot/tasks/validate_config.yml
-
+12 -0roles/matrix-bot-matrix-registration-bot/templates/config/config.yml.j2
-
+37 -0roles/matrix-bot-matrix-registration-bot/templates/systemd/matrix-bot-matrix-registration-bot.service.j2
-
+2 -0roles/matrix-bot-matrix-reminder-bot/tasks/setup_install.yml
-
+4 -4roles/matrix-bot-matrix-reminder-bot/templates/systemd/matrix-bot-matrix-reminder-bot.service.j2
-
+2 -0roles/matrix-bot-mjolnir/tasks/setup_install.yml
+ 59
- 0
CHANGELOG.md
Просмотреть файл
| @@ -1,3 +1,62 @@ | |||
| # 2022-04-25 | |||
| ## buscarron bot support | |||
| Thanks to [Aine](https://gitlab.com/etke.cc) of [etke.cc](https://etke.cc/), the playbook can now set up [the Buscarron bot](https://gitlab.com/etke.cc/buscarron). It's a bot you can use to send any form (HTTP POST, HTML) to a (encrypted) Matrix room | |||
| See our [Setting up Buscarron](docs/configuring-playbook-bot-buscarron.md) documentation to get started. | |||
| # 2022-04-21 | |||
| ## matrix-registration-bot support | |||
| Thanks to [Julian-Samuel Gebühr (@moan0s)](https://github.com/moan0s), the playbook can now help you set up [matrix-registration-bot](https://github.com/moan0s/matrix-registration-bot) - a bot that is used to create and manage registration tokens for a Matrix server. | |||
| See our [Setting up matrix-registration-bot](docs/configuring-playbook-bot-matrix-registration-bot.md) documentation to get started. | |||
| # 2022-04-19 | |||
| ## Borg backup support | |||
| Thanks to [Aine](https://gitlab.com/etke.cc) of [etke.cc](https://etke.cc/), the playbook can now set up [Borg](https://www.borgbackup.org/) backups with [borgmatic](https://torsion.org/borgmatic/) of your Matrix server. | |||
| See our [Setting up borg backup](docs/configuring-playbook-backup-borg.md) documentation to get started. | |||
| ## (Compatibility Break) Upgrading to Synapse v1.57 on setups using workers may require manual action | |||
| If you're running a worker setup for Synapse (`matrix_synapse_workers_enabled: true`), the [Synapse v1.57 upgrade notes](https://github.com/matrix-org/synapse/blob/v1.57.0rc1/docs/upgrade.md#changes-to-database-schema-for-application-services) say that you may need to take special care when upgrading: | |||
| > Synapse v1.57.0 includes a change to the way transaction IDs are managed for application services. If your deployment uses a dedicated worker for application service traffic, **it must be stopped** when the database is upgraded (which normally happens when the main process is upgraded), to ensure the change is made safely without any risk of reusing transaction IDs. | |||
| If you're not running an `appservice` worker (`matrix_synapse_workers_preset: little-federation-helper` or `matrix_synapse_workers_appservice_workers_count: 0`), you are probably safe to upgrade as per normal, without taking any special care. | |||
| If you are running a setup with an `appservice` worker, or otherwise want to be on the safe side, we recommend the following upgrade path: | |||
| 0. Pull the latest playbook changes | |||
| 1. Stop all services (`ansible-playbook -i inventory/hosts setup.yml --tags=stop`) | |||
| 2. Re-run the playbook (`ansible-playbook -i inventory/hosts setup.yml --tags=setup-all`) | |||
| 3. Start Postgres (`systemctl start matrix-postgres` on the server) | |||
| 4. Start the main Synapse process (`systemctl start matrix-synapse` on the server) | |||
| 5. Wait a while so that Synapse can start and complete the database migrations. You can use `journalctl -fu matrix-synapse` on the server to get a clue. Waiting a few minutes should also be enough. | |||
| 6. It should now be safe to start all other services. `ansible-playbook -i inventory/hosts setup.yml --tags=start` will do it for you | |||
| # 2022-04-14 | |||
| ## (Compatibility Break) Changes to `docker-src` permissions necessitating manual action | |||
| Users who build container images from source will need to manually correct file permissions of some directories on the server. | |||
| When self-building, the playbook used to `git clone` repositories (into `/matrix/SERVICE/docker-src`) using the `root` user, but now uses `matrix` instead to work around [the following issue with git 2.35.2](https://github.com/spantaleev/matrix-docker-ansible-deploy/issues/1749). | |||
| If you're on a non-`amd64` architecture (that is, you're overriding `matrix_architecture` in your `vars.yml` file) or you have enabled self-building for some service (e.g. `matrix_*_self_build: true`), you're certainly building some container images from source and have `docker-src` directories with mixed permissions lying around in various `/matrix/SERVICE` directories. | |||
| The playbook *could* correct these permissions automatically, but that requires additional Ansible tasks in some ~45 different places - something that takes considerable effort. So we ask users observing errors related to `docker-src` directories to correct the problem manually by **running this command on the Matrix server** (which deletes all `/matrix/*/docker-src` directories): `find /matrix -maxdepth 2 -name 'docker-src' | xargs rm -rf` | |||
| # 2022-03-17 | |||
| ## (Compatibility Break) ma1sd identity server no longer installed by default | |||
+ 4
- 0
README.md
Просмотреть файл
| @@ -121,6 +121,10 @@ Using this playbook, you can get the following services configured on your serve | |||
| - (optional) the [Cinny](https://github.com/ajbura/cinny) web client - see [docs/configuring-playbook-client-cinny.md](docs/configuring-playbook-client-cinny.md) for setup documentation | |||
| - (optional) the [Borg](https://borgbackup.org) backup - see [docs/configuring-playbook-backup-borg.md](docs/configuring-playbook-backup-borg.md) for setup documentation | |||
| - (optional) the [Buscarron](https://gitlab.com/etke.cc/buscarron) bot - see [docs/configuring-playbook-bot-buscarron.md](docs/configuring-playbook-bot-buscarron.md) for setup documentation | |||
| Basically, this playbook aims to get you up-and-running with all the necessities around Matrix, without you having to do anything else. | |||
| **Note**: the list above is exhaustive. It includes optional or even some advanced components that you will most likely not need. | |||
+ 2
- 2
docs/alternative-architectures.md
Просмотреть файл
| @@ -2,7 +2,7 @@ | |||
| As stated in the [Prerequisites](prerequisites.md), currently only `x86_64` is fully supported. However, it is possible to set the target architecture, and some tools can be built on the host or other measures can be used. | |||
| To that end add the following variable to your `vars.yaml` file: | |||
| To that end add the following variable to your `vars.yml` file (see [Configuring playbook](configuring-playbook.md)): | |||
| ```yaml | |||
| matrix_architecture: <your-matrix-server-architecture> | |||
| @@ -13,7 +13,7 @@ Currently supported architectures are the following: | |||
| - `arm64` | |||
| - `arm32` | |||
| so for the Raspberry Pi, the following should be in your `vars.yaml` file: | |||
| so for the Raspberry Pi, the following should be in your `vars.yml` file: | |||
| ```yaml | |||
| matrix_architecture: "arm32" | |||
Двоичные данные
docs/assets/obtain_admin_access_token_element.png
Просмотреть файл
+ 0
- 39
docs/configuring-awx-system.md
Просмотреть файл
| @@ -1,39 +0,0 @@ | |||
| # Configuring AWX System (optional) | |||
| An AWX setup for managing multiple Matrix servers. | |||
| This section is used in an AWX system that can create and manage multiple [Matrix](http://matrix.org/) servers. You can issue members an AWX login to their own 'organisation', which they can use to manage/configure 1 to N servers. | |||
| Members can be assigned a server from Digitalocean, or they can connect their own on-premises server. These playbooks are free to use in a commercial context with the 'MemberPress Plus' plugin. They can also be run in a non-commercial context. | |||
| The AWX system is arranged into 'members' each with their own 'subscriptions'. After creating a subscription the user enters the 'provision stage' where they defined the URLs they will use, the servers location and whether or not there's already a website at the base domain. They then proceed onto the 'deploy stage' where they can configure their Matrix server. | |||
| This system can manage the updates, configuration, import and export, backups and monitoring on its own. It is an extension of the popular deploy script [spantaleev/matrix-docker-ansible-deploy](https://github.com/spantaleev/matrix-docker-ansible-deploy). | |||
| Warning: This system is about to undergo heavy revision, **we do not recommend using it at this time.** | |||
| ## Other Required Playbooks | |||
| The following repositories allow you to copy and use this setup: | |||
| [Create AWX System](https://gitlab.com/GoMatrixHosting/create-awx-system) - Creates and configures the AWX system for you. | |||
| [Ansible Create Delete Subscription Membership](https://gitlab.com/GoMatrixHosting/ansible-create-delete-subscription-membership) - Used by the AWX system to create memberships and subscriptions. Also includes other administrative playbooks for updates, backups and restoring servers. | |||
| [Ansible Provision Server](https://gitlab.com/GoMatrixHosting/ansible-provision-server) - Used by AWX members to perform initial configuration of their DigitalOcean or On-Premises server. | |||
| [GMHosting External Tools](https://gitlab.com/GoMatrixHosting/gmhosting-external-tools) - Extra tools we run outside of AWX, some of which are experimental. | |||
| ## Does I need an AWX setup to use this? How do I configure it? | |||
| Yes, you'll need to configure an AWX instance, the [Create AWX System](https://gitlab.com/GoMatrixHosting/create-awx-system) repository makes it easy to do. Just follow the steps listed in ['/docs/Installation_AWX.md' of that repository](https://gitlab.com/GoMatrixHosting/create-awx-system/-/blob/master/docs/Installation_AWX.md). | |||
| For simpler installation steps you can use to get started with this system, check out our minimal installation guide at ['/doc/Installation_Minimal_AWX.md of that repository'](https://gitlab.com/GoMatrixHosting/create-awx-system/-/blob/master/docs/Installation_Minimal_AWX.md). | |||
| ## Does I need a front-end WordPress site? And a DigitalOcean account? | |||
| You do not need a front-end WordPress site or the MemberPress plugin to use this setup. It can be run on it's own in a non-commercial context. | |||
| You also don't need a DigitalOcean account, although this will limit you to only being able to connect 'On-Premises' servers. | |||
+ 3
- 0
docs/configuring-dns.md
Просмотреть файл
| @@ -38,6 +38,7 @@ If you are using Cloudflare DNS, make sure to disable the proxy and set all reco | |||
| | CNAME | `sygnal` | - | - | - | `matrix.<your-domain>` | | |||
| | CNAME | `hydrogen` | - | - | - | `matrix.<your-domain>` | | |||
| | CNAME | `cinny` | - | - | - | `matrix.<your-domain>` | | |||
| | CNAME | `buscarron` | - | - | - | `matrix.<your-domain>` | | |||
| ## Subdomains setup | |||
| @@ -60,6 +61,8 @@ The `hydrogen.<your-domain>` subdomain may be necessary, because this playbook c | |||
| The `cinny.<your-domain>` subdomain may be necessary, because this playbook could install the [Cinny](https://github.com/ajbura/cinny) web client. The installation of cinny is disabled by default, it is not a core required component. To learn how to install it, see our [configuring cinny guide](configuring-playbook-client-cinny.md). If you do not wish to set up cinny, feel free to skip the `cinny.<your-domain>` DNS record. | |||
| The `buscarron.<your-domain>` subdomain may be necessary, because this playbook could install the [buscarron](https://github.com/etke.cc/buscarron) bot. The installation of buscarron is disabled by default, it is not a core required component. To learn how to install it, see our [configuring buscarron guide](configuring-playbook-bot-buscarron.md). If you do not wish to set up buscarron, feel free to skip the `buscarron.<your-domain>` DNS record. | |||
| ## `_matrix-identity._tcp` SRV record setup | |||
| To make the [ma1sd](https://github.com/ma1uta/ma1sd) Identity Server (which this playbook may optionally install for you) enable its federation features, set up an SRV record that looks like this: | |||
+ 69
- 0
docs/configuring-playbook-backup-borg.md
Просмотреть файл
| @@ -0,0 +1,69 @@ | |||
| # Setting up borg backup (optional) | |||
| The playbook can install and configure [borgbackup](https://www.borgbackup.org/) with [borgmatic](https://torsion.org/borgmatic/) for you. | |||
| BorgBackup is a deduplicating backup program with optional compression and encryption. | |||
| That means your daily incremental backups can be stored in a fraction of the space and is safe whether you store it at home or on a cloud service. | |||
| You will need a remote server where borg will store the backups. There are hosted, borg compatible solutions available, such as [BorgBase](https://www.borgbase.com). | |||
| The backup will run based on `matrix_backup_borg_schedule` var (systemd timer calendar), default: 4am every day. | |||
| By default, if you're using the integrated Postgres database server (as opposed to [an external Postgres server](configuring-playbook-external-postgres.md)), Borg backups will also include dumps of your Postgres database. An alternative solution for backing up the Postgres database is [postgres backup](configuring-playbook-postgres-backup.md). If you decide to go with another solution, you can disable Postgres-backup support for Borg using the `matrix_backup_borg_postgresql_enabled` variable. | |||
| ## Prerequisites | |||
| 1. Create a new SSH key: | |||
| ```bash | |||
| ssh-keygen -t ed25519 -N '' -f matrix-borg-backup -C matrix | |||
| ``` | |||
| This can be done on any machine and you don't need to place the key in the `.ssh` folder. It will be added to the Ansible config later. | |||
| 2. Add the **public** part of this SSH key (the `matrix-borg-backup.pub` file) to your borg provider/server: | |||
| If you plan to use a hosted solution, follow their instructions. If you have your own server, copy the key over: | |||
| ```bash | |||
| # example to append the new PUBKEY contents, where: | |||
| # PUBKEY is path to the public key, | |||
| # USER is a ssh user on a provider / server | |||
| # HOST is a ssh host of a provider / server | |||
| cat PUBKEY | ssh USER@HOST 'dd of=.ssh/authorized_keys oflag=append conv=notrunc' | |||
| ``` | |||
| ## Adjusting the playbook configuration | |||
| Minimal working configuration (`inventory/host_vars/matrix.DOMAIN/vars.yml`) to enable borg backup: | |||
| ```yaml | |||
| matrix_backup_borg_enabled: true | |||
| matrix_backup_borg_location_repositories: | |||
| - USER@HOST:REPO | |||
| matrix_backup_borg_storage_encryption_passphrase: "PASSPHRASE" | |||
| matrix_backup_borg_ssh_key_private: | | |||
| PRIVATE KEY | |||
| ``` | |||
| where: | |||
| * USER - SSH user of a provider/server | |||
| * HOST - SSH host of a provider/server | |||
| * REPO - borg repository name, it will be initialized on backup start, eg: `matrix` | |||
| * PASSPHRASE - passphrase used for encrypting backups, you may generate it with `pwgen -s 64 1` or use any password manager | |||
| * PRIVATE KEY - the content of the **private** part of the SSH key you created before | |||
| To backup without encryption, add `matrix_backup_borg_encryption: 'none'` to your vars. This will also enable the `matrix_backup_borg_unknown_unencrypted_repo_access_is_ok` variable. | |||
| `matrix_backup_borg_location_source_directories` defines the list of directories to back up: it's set to `{{ matrix_base_data_path }}` by default, which is the base directory for every service's data, such as Synapse, Postgres and the bridges. You might want to exclude certain directories or file patterns from the backup using the `matrix_backup_borg_location_exclude_patterns` variable. | |||
| Check the `roles/matrix-backup-borg/defaults/main.yml` file for the full list of available options. | |||
| ## Installing | |||
| After configuring the playbook, run the [installation](installing.md) command again: | |||
| ``` | |||
| ansible-playbook -i inventory/hosts setup.yml --tags=setup-all,start | |||
| ``` | |||
+ 75
- 0
docs/configuring-playbook-bot-buscarron.md
Просмотреть файл
| @@ -0,0 +1,75 @@ | |||
| # Setting up Buscarron (optional) | |||
| The playbook can install and configure [buscarron](https://gitlab.com/etke.cc/buscarron) for you. | |||
| It's a bot you can use to setup **your own helpdesk on matrix** | |||
| It's a bot you can use to send any form (HTTP POST, HTML) to a (encrypted) matrix room | |||
| ## Registering the bot user | |||
| By default, the playbook will set up the bot with a username like this: `@bot.buscarron:DOMAIN`. | |||
| (to use a different username, adjust the `matrix_bot_buscarron_login` variable). | |||
| You **need to register the bot user manually** before setting up the bot. You can use the playbook to [register a new user](registering-users.md): | |||
| ``` | |||
| ansible-playbook -i inventory/hosts setup.yml --extra-vars='username=bot.buscarron password=PASSWORD_FOR_THE_BOT admin=no' --tags=register-user | |||
| ``` | |||
| Choose a strong password for the bot. You can generate a good password with a command like this: `pwgen -s 64 1`. | |||
| ## Adjusting the playbook configuration | |||
| Add the following configuration to your `inventory/host_vars/matrix.DOMAIN/vars.yml` file: | |||
| ```yaml | |||
| matrix_bot_buscarron_enabled: true | |||
| # Adjust this to whatever password you chose when registering the bot user | |||
| matrix_bot_buscarron_password: PASSWORD_FOR_THE_BOT | |||
| # Adjust accepted forms | |||
| matrix_bot_buscarron_forms: | |||
| - name: contact # (mandatory) Your form name, will be used as endpoint, eg: buscarron.DOMAIN/contact | |||
| room: "!yourRoomID:DOMAIN" # (mandatory) Room ID where form submission will be posted | |||
| redirect: https://DOMAIN # (mandatory) To what page user will be redirected after the form submission | |||
| ratelimit: 1r/m # (optional) rate limit of the form, format: <max requests>r/<interval:s,m>, eg: 1r/s or 54r/m | |||
| extensions: [] # (optional) list of form extensions (not used yet) | |||
| matrix_bot_buscarron_spam_hosts: [] # (optional) list of email domains/hosts that should be rejected automatically | |||
| matrix_bot_buscarron_spam_emails: [] # (optional) list of email addresses that should be rejected automatically | |||
| ``` | |||
| You will also need to add a DNS record so that buscarron can be accessed. | |||
| By default buscarron will use https://buscarron.DOMAIN so you will need to create an CNAME record for `buscarron`. | |||
| See [Configuring DNS](configuring-dns.md). | |||
| If you would like to use a different domain, add the following to your configuration file (changing it to use your preferred domain): | |||
| ```yaml | |||
| matrix_server_fqn_buscarron: "form.{{ matrix_domain }}" | |||
| ``` | |||
| ## Installing | |||
| After configuring the playbook, run the [installation](installing.md) command again: | |||
| ``` | |||
| ansible-playbook -i inventory/hosts setup.yml --tags=setup-all,start | |||
| ``` | |||
| ## Usage | |||
| To use the bot, invite the `@bot.buscarron:DOMAIN` to the room you specified in a config, after that any point your form to the form url, example for the `contact` form: | |||
| ```html | |||
| <form method="POST" action="https://buscarron.DOMAIN/contact"> | |||
| <!--your fields--> | |||
| </form> | |||
| ``` | |||
| You can also refer to the upstream [documentation](https://gitlab.com/etke.cc/buscarron). | |||
+ 72
- 0
docs/configuring-playbook-bot-matrix-registration-bot.md
Просмотреть файл
| @@ -0,0 +1,72 @@ | |||
| # Setting up matrix-registration-bot (optional) | |||
| The playbook can install and configure [matrix-registration-bot](https://github.com/moan0s/matrix-registration-bot) for you. | |||
| The bot allows you to easily **create and manage registration tokens**. It can be used for an invitation-based server, | |||
| where you invite someone by sending them a registration token. They can register as normal but have to provide a valid | |||
| registration token in a final step of the registration. | |||
| See the project's [documentation](https://github.com/moan0s/matrix-registration-bot#supported-commands) to learn what it | |||
| does and why it might be useful to you. | |||
| ## Registering the bot user | |||
| By default, the playbook will set use the bot with a username like this: `@bot.matrix-registration-bot:DOMAIN`. | |||
| (to use a different username, adjust the `matrix_bot_matrix_registration_bot_matrix_user_id_localpart` variable). | |||
| You **need to register the bot user manually** before setting up the bot. You can use the playbook to [register a new user](registering-users.md): | |||
| ``` | |||
| ansible-playbook -i inventory/hosts setup.yml --extra-vars='username=bot.matrix-registration-bot password=PASSWORD_FOR_THE_BOT admin=yes' --tags=register-user | |||
| ``` | |||
| Choose a strong password for the bot. You can generate a good password with a command like this: `pwgen -s 64 1`. | |||
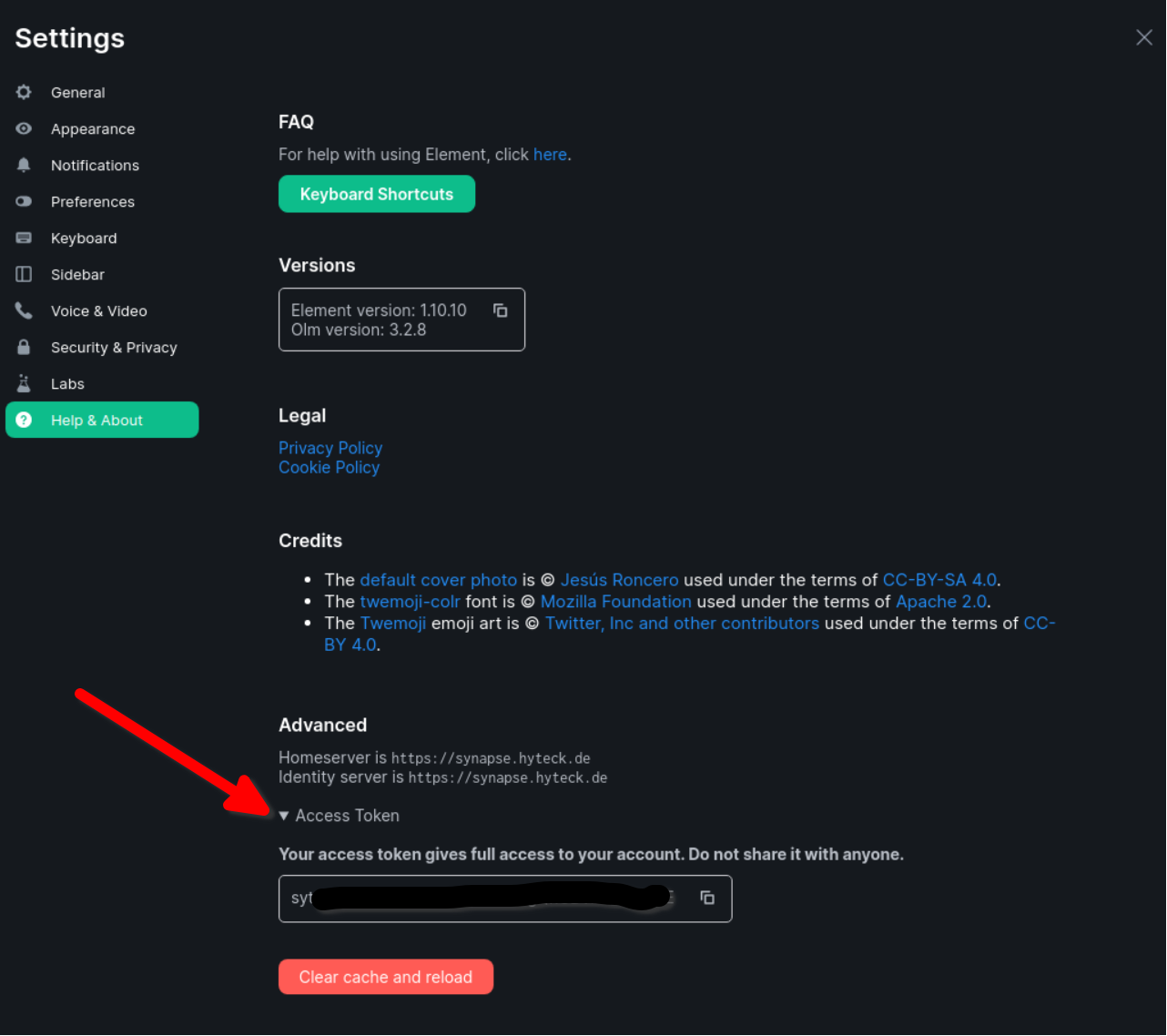
| ## Obtaining an admin access token | |||
| In order to use the bot you need to add an admin user's access token token to the configuration. As you created an admin user for the | |||
| bot, it is recommended to obtain an access token by logging into Element/Schildichat with the bot account | |||
| (using the password you set) and navigate to `Settings->Help&About` and scroll to the bottom. | |||
| You can expand "Access token" to copy it. | |||
|  | |||
| **IMPORTANT**: once you copy the token, just close the Matrix client window/tab. Do not "log out", as that would invalidate the token. | |||
| ## Adjusting the playbook configuration | |||
| Add the following configuration to your `inventory/host_vars/matrix.DOMAIN/vars.yml` file: | |||
| ```yaml | |||
| matrix_bot_matrix_registration_bot_enabled: true | |||
| # Token obtained via logging into the bot account (see above) | |||
| matrix_bot_matrix_registration_bot_bot_access_token: "syt_bW9hbm9z_XXXXXXXXXXXXXr_2kuzbE" | |||
| # Enables registration | |||
| matrix_synapse_enable_registration: true | |||
| # Restrict registration to users with a token | |||
| matrix_synapse_registration_requires_token: true | |||
| ``` | |||
| ## Installing | |||
| After configuring the playbook, run the [installation](installing.md) command again: | |||
| ``` | |||
| ansible-playbook -i inventory/hosts setup.yml --tags=setup-all,start | |||
| ``` | |||
| ## Usage | |||
| To use the bot, create a **non-encrypted** room and invite `@bot.matrix-registration-bot:DOMAIN` (where `YOUR_DOMAIN` is your base domain, not the `matrix.` domain). | |||
| In this room send `help` and the bot will reply with all options. | |||
| You can also refer to the upstream [Usage documentation](https://github.com/moan0s/matrix-registration-bot#supported-commands). | |||
| If you have any questions, or if you need help setting it up, read the [troublshooting guide](https://github.com/moan0s/matrix-registration-bot/blob/main/docs/troubleshooting.md) | |||
| or join [#matrix-registration-bot:hyteck.de](https://matrix.to/#/#matrix-registration-bot:hyteck.de). | |||
+ 6
- 6
docs/configuring-playbook-bridge-hookshot.md
Просмотреть файл
| @@ -16,24 +16,24 @@ Refer to the [official instructions](https://matrix-org.github.io/matrix-hooksho | |||
| 2. Take special note of the `matrix_hookshot_*_enabled` variables. Services that need no further configuration are enabled by default (GitLab, Generic), while you must first add the required configuration and enable the others (GitHub, Jira, Figma). | |||
| 3. If you're setting up the GitHub bridge, you'll need to generate and download a private key file after you created your GitHub app. Copy the contents of that file to the variable `matrix_hookshot_github_private_key` so the playbook can install it for you, or use one of the [other methods](#manage-github-private-key-with-matrix-aux-role) explained below. | |||
| 4. If you've already installed Matrix services using the playbook before, you'll need to re-run it (`--tags=setup-all,start`). If not, proceed with [configuring other playbook services](configuring-playbook.md) and then with [Installing](installing.md). Get back to this guide once ready. Hookshot can be set up individually using the tag `setup-hookshot`. | |||
| 5. Refer to [Hookshot's official instructions](https://matrix-org.github.io/matrix-hookshot/usage.html) to start using the bridge. **Important:** Note that the different listeners are bound to certain paths which might differe from those assumed by the hookshot documentation, see [URLs for bridges setup](urls-for-bridges-setup) below. | |||
| 5. Refer to [Hookshot's official instructions](https://matrix-org.github.io/matrix-hookshot/usage.html) to start using the bridge. **Important:** Note that the different listeners are bound to certain paths which might differ from those assumed by the hookshot documentation, see [URLs for bridges setup](urls-for-bridges-setup) below. | |||
| Other configuration options are available via the `matrix_hookshot_configuration_extension_yaml` and `matrix_hookshot_registration_extension_yaml` variables, see the comments in [main.yml](/roles/matrix-bridge-hookshot/defaults/main.yml) for how to use them. | |||
| ### URLs for bridges setup | |||
| All of the following endpoints are reachable on your `matrix.` subdomain (if the feature is enabled). | |||
| Unless indicated otherwise, the following endpoints are reachable on your `matrix.` subdomain (if the feature is enabled). | |||
| | Listener | default path | variable | used as | | |||
| | listener | default path | variable | used as | | |||
| |---|---|---|---| | |||
| | webhooks | `/hookshot/webhooks/` | `matrix_hookshot_webhook_endpoint` | GitHub "Webhook URL" | | |||
| | webhooks | `/hookshot/webhooks/` | `matrix_hookshot_webhook_endpoint` | generics, GitHub "Webhook URL", etc. | | |||
| | github oauth | `/hookshot/webhooks/oauth` | `matrix_hookshot_github_oauth_endpoint` | GitHub "Callback URL" | | |||
| | jira oauth | `/hookshot/webhooks/jira/oauth` | `matrix_hookshot_jira_oauth_endpoint` | JIRA OAuth | | |||
| | figma endpoint | `/hookshot/webhooks/figma/webhook` | `matrix_hookshot_figma_endpoint` | Figma | | |||
| | provisioning | `/hookshot/v1/` | `matrix_hookshot_provisioning_endpoint` | Dimension [provisioning](#provisioning-api) | | |||
| | appservice | `/hookshot/_matrix/app/` | `matrix_hookshot_appservice_endpoint` | Matrix server | | |||
| | metrics | `/hookshot/metrics/` | `matrix_hookshot_metrics_endpoint` | Prometheus | | |||
| | widgets | | | not supported | | |||
| | widgets | `/hookshot/widgetapi/` | `/matrix_hookshot_widgets_endpoint` | Widgets | | |||
| | metrics | `/hookshot/metrics/` (on `stats.` subdomain) | `matrix_hookshot_metrics_endpoint` | Prometheus | | |||
| See also `matrix_hookshot_matrix_nginx_proxy_configuration` in [init.yml](/roles/matrix-bridge-hookshot/tasks/init.yml). | |||
+ 15
- 0
docs/configuring-playbook-bridge-mautrix-telegram.md
Просмотреть файл
| @@ -49,4 +49,19 @@ If you want to use the relay-bot feature ([relay bot documentation](https://docs | |||
| ```yaml | |||
| matrix_mautrix_telegram_bot_token: YOUR_TELEGRAM_BOT_TOKEN | |||
| matrix_mautrix_telegram_configuration_extension_yaml: | | |||
| bridge: | |||
| permissions: | |||
| '*': relaybot | |||
| ``` | |||
| You might also want to give permissions to administrate the bot: | |||
| ```yaml | |||
| matrix_mautrix_telegram_configuration_extension_yaml: | | |||
| bridge: | |||
| permissions: | |||
| '@user:DOMAIN': admin | |||
| ``` | |||
| More details about permissions in this example: | |||
| https://github.com/mautrix/telegram/blob/master/mautrix_telegram/example-config.yaml#L410 | |||
+ 3
- 0
docs/configuring-playbook-postgres-backup.md
Просмотреть файл
| @@ -2,6 +2,9 @@ | |||
| The playbook can install and configure [docker-postgres-backup-local](https://github.com/prodrigestivill/docker-postgres-backup-local) for you. | |||
| For a more complete backup solution (one that includes not only Postgres, but also other configuration/data files), you may wish to look into [borg backup](configuring-playbook-backup-borg.md) instead. | |||
| ## Adjusting the playbook configuration | |||
| Minimal working configuration (`inventory/host_vars/matrix.DOMAIN/vars.yml`) to enable Postgres backup: | |||
+ 11
- 0
docs/configuring-playbook.md
Просмотреть файл
| @@ -145,12 +145,23 @@ When you're done with all the configuration you'd like to do, continue with [Ins | |||
| - [Setting up matrix-reminder-bot](configuring-playbook-bot-matrix-reminder-bot.md) - a bot to remind you about stuff (optional) | |||
| - [Setting up matrix-registration-bot](configuring-playbook-bot-matrix-registration-bot.md) - a bot to create and manage registration tokens to invite users (optional) | |||
| - [Setting up honoroit](configuring-playbook-bot-honoroit.md) - a helpdesk bot (optional) | |||
| - [Setting up Go-NEB](configuring-playbook-bot-go-neb.md) - an extensible multifunctional bot (optional) | |||
| - [Setting up Mjolnir](configuring-playbook-bot-mjolnir.md) - a moderation tool/bot (optional) | |||
| - [Setting up Buscarron](configuring-playbook-bot-buscarron.md) - a bot you can use to send any form (HTTP POST, HTML) to a (encrypted) Matrix room (optional) | |||
| ### Backups | |||
| - [Setting up borg backup](configuring-playbook-backup-borg.md) - a full Matrix server backup solution, including the Postgres database (optional) | |||
| - [Setting up postgres backup](configuring-playbook-postgres-backup.md) - a Postgres-database backup solution (note: does not include other files) (optional) | |||
| ### Other specialized services | |||
+ 1
- 1
docs/faq.md
Просмотреть файл
| @@ -55,7 +55,7 @@ There are 3 ways to get into Martix, depending on your technical ability and nee | |||
| - **using the existing default server** - the easiest way is to use an existing server. The largest public Matrix server is `matrix.org` and it's configured as a default server in clients such as [Element](https://element.io) and many others. Just use Element on the browser via that link (or download the Element app on a smartphone), create an account and start chatting. | |||
| - **using some other server** - instead of using the largest public server (`matrix.org`), you can use another public one. Here's a [list of public Matrix servers](https://publiclist.anchel.nl/) to choose from. Again, you download [Element](https://element.io) or [some other client](https://matrix.org/clients/) of your choosing and adjust the homeserver URL during login. | |||
| - **using some other server** - instead of using the largest public server (`matrix.org`), you can use another public one. Here's a [list of public Matrix servers](https://joinmatrix.org/servers/) to choose from. Again, you download [Element](https://element.io) or [some other client](https://matrix.org/clients/) of your choosing and adjust the homeserver URL during login. | |||
| - **using your own server** - running your own server puts you in ultimate control of your data. It also lets you have your own user identifiers (e.g. `@bob:your-domain.com`). See [How do I set up my own Matrix server](#how-do-i-set-up-my-own-matrix-server). | |||
+ 1
- 0
docs/self-building.md
Просмотреть файл
| @@ -22,6 +22,7 @@ List of roles where self-building the Docker image is currently possible: | |||
| - `matrix-dimension` | |||
| - `matrix-ma1sd` | |||
| - `matrix-mailer` | |||
| - `matrix-bridge-hookshot` | |||
| - `matrix-bridge-appservice-irc` | |||
| - `matrix-bridge-appservice-slack` | |||
| - `matrix-bridge-appservice-webhooks` | |||
+ 126
- 41
group_vars/matrix_servers
Просмотреть файл
| @@ -47,27 +47,6 @@ matrix_integration_manager_ui_url: "{{ matrix_dimension_integrations_ui_url if m | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-awx | |||
| # | |||
| ###################################################################### | |||
| # We don't enable AWX support by default. | |||
| matrix_awx_enabled: false | |||
| matrix_nginx_proxy_data_path: "{{ '/chroot/website' if (matrix_awx_enabled and not matrix_nginx_proxy_base_domain_homepage_enabled) else (matrix_nginx_proxy_base_path + '/data') }}" | |||
| matrix_nginx_proxy_data_path_in_container: "{{ '/nginx-data/matrix-domain' if (matrix_awx_enabled and not matrix_nginx_proxy_base_domain_homepage_enabled) else '/nginx-data' }}" | |||
| matrix_nginx_proxy_data_path_extension: "{{ '' if (matrix_awx_enabled and not matrix_nginx_proxy_base_domain_homepage_enabled) else '/matrix-domain' }}" | |||
| matrix_nginx_proxy_base_domain_create_directory: "{{ not matrix_awx_enabled }}" | |||
| ###################################################################### | |||
| # | |||
| # /matrix-awx | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-bridge-appservice-discord | |||
| @@ -481,7 +460,7 @@ matrix_mautrix_signal_database_engine: 'postgres' | |||
| matrix_mautrix_signal_database_password: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'mau.signal.db') | to_uuid }}" | |||
| matrix_mautrix_signal_container_image_self_build: "{{ matrix_architecture not in ['amd64', 'arm64'] }}" | |||
| matrix_mautrix_signal_daemon_container_image_self_build: "{{ matrix_architecture != 'amd64' }}" | |||
| matrix_mautrix_signal_daemon_container_image_self_build: "{{ matrix_architecture not in ['amd64', 'arm64'] }}" | |||
| ###################################################################### | |||
| # | |||
| @@ -556,14 +535,14 @@ matrix_mautrix_twitter_systemd_required_services_list: | | |||
| (['matrix-nginx-proxy.service'] if matrix_nginx_proxy_enabled else []) | |||
| }} | |||
| matrix_mautrix_twitter_appservice_token: "{{ matrix_homeserver_generic_secret_key | password_hash('sha512', 'twt.as.token') | to_uuid }}" | |||
| matrix_mautrix_twitter_appservice_token: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'twt.as.token') | to_uuid }}" | |||
| matrix_mautrix_twitter_homeserver_token: "{{ matrix_homeserver_generic_secret_key | password_hash('sha512', 'twt.hs.token') | to_uuid }}" | |||
| matrix_mautrix_twitter_homeserver_token: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'twt.hs.token') | to_uuid }}" | |||
| matrix_mautrix_twitter_login_shared_secret: "{{ matrix_synapse_ext_password_provider_shared_secret_auth_shared_secret if matrix_synapse_ext_password_provider_shared_secret_auth_enabled else '' }}" | |||
| matrix_mautrix_twitter_database_hostname: "{{ 'matrix-postgres' if matrix_postgres_enabled else '' }}" | |||
| matrix_mautrix_twitter_database_password: "{{ matrix_homeserver_generic_secret_key | password_hash('sha512', 'mau.twt.db') | to_uuid if matrix_postgres_enabled else '' }}" | |||
| matrix_mautrix_twitter_database_password: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'mau.twt.db') | to_uuid if matrix_postgres_enabled else '' }}" | |||
| ###################################################################### | |||
| # | |||
| @@ -673,6 +652,8 @@ matrix_heisenbridge_systemd_wanted_services_list: | | |||
| # We don't enable bridges by default. | |||
| matrix_hookshot_enabled: false | |||
| matrix_hookshot_container_image_self_build: "{{ matrix_architecture not in ['amd64'] }}" | |||
| matrix_hookshot_appservice_token: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'hookshot.as.tok') | to_uuid }}" | |||
| matrix_hookshot_homeserver_token: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'hookshot.hs.tok') | to_uuid }}" | |||
| @@ -697,9 +678,9 @@ matrix_hookshot_provisioning_enabled: "{{ matrix_hookshot_provisioning_secret an | |||
| matrix_hookshot_proxy_metrics: "{{ matrix_nginx_proxy_proxy_synapse_metrics }}" | |||
| matrix_hookshot_proxy_metrics_basic_auth_enabled: "{{ matrix_nginx_proxy_proxy_synapse_metrics_basic_auth_enabled }}" | |||
| matrix_hookshot_generic_urlprefix_port_enabled: "{{ matrix_nginx_proxy_container_https_host_bind_port == 443 if matrix_nginx_proxy_https_enabled else matrix_nginx_proxy_container_https_host_bind_port == 80 }}" | |||
| matrix_hookshot_generic_urlprefix_port: ":{{ matrix_nginx_proxy_container_https_host_bind_port if matrix_nginx_proxy_https_enabled else matrix_nginx_proxy_container_http_host_bind_port }}" | |||
| matrix_hookshot_generic_urlprefix: "http{{ 's' if matrix_nginx_proxy_https_enabled else '' }}://{{ matrix_server_fqn_matrix }}{{ matrix_hookshot_generic_urlprefix_port if matrix_hookshot_generic_urlprefix_port_enabled else '' }}{{ matrix_hookshot_generic_endpoint }}" | |||
| matrix_hookshot_urlprefix_port_enabled: "{{ matrix_nginx_proxy_container_https_host_bind_port == 443 if matrix_nginx_proxy_https_enabled else matrix_nginx_proxy_container_https_host_bind_port == 80 }}" | |||
| matrix_hookshot_urlprefix_port: ":{{ matrix_nginx_proxy_container_https_host_bind_port if matrix_nginx_proxy_https_enabled else matrix_nginx_proxy_container_http_host_bind_port }}" | |||
| matrix_hookshot_urlprefix: "http{{ 's' if matrix_nginx_proxy_https_enabled else '' }}://{{ matrix_server_fqn_matrix }}{{ matrix_hookshot_urlprefix_port if matrix_hookshot_urlprefix_port_enabled else '' }}" | |||
| ###################################################################### | |||
| # | |||
| @@ -1008,6 +989,35 @@ matrix_bot_matrix_reminder_bot_container_image_self_build: "{{ matrix_architectu | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-bot-matrix-registration-bot | |||
| # | |||
| ###################################################################### | |||
| # We don't enable bots by default. | |||
| matrix_bot_matrix_registration_bot_enabled: false | |||
| matrix_bot_matrix_registration_bot_container_image_self_build: "{{ matrix_architecture not in ['amd64'] }}" | |||
| matrix_bot_matrix_registration_bot_systemd_required_services_list: | | |||
| {{ | |||
| ['docker.service'] | |||
| + | |||
| ['matrix-' + matrix_homeserver_implementation + '.service'] | |||
| + | |||
| (['matrix-nginx-proxy.service'] if matrix_nginx_proxy_enabled else []) | |||
| }} | |||
| ###################################################################### | |||
| # | |||
| # /matrix-bot-matrix-registration-bot | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-bot-honoroit | |||
| @@ -1039,6 +1049,37 @@ matrix_bot_honoroit_container_image_self_build: "{{ matrix_architecture not in [ | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-bot-buscarron | |||
| # | |||
| ###################################################################### | |||
| # We don't enable bots by default. | |||
| matrix_bot_buscarron_enabled: false | |||
| matrix_bot_buscarron_systemd_required_services_list: | | |||
| {{ | |||
| ['docker.service'] | |||
| + | |||
| (['matrix-postgres.service'] if matrix_postgres_enabled else []) | |||
| + | |||
| (['matrix-synapse.service'] if matrix_synapse_enabled else []) | |||
| + | |||
| (['matrix-nginx-proxy.service'] if matrix_nginx_proxy_enabled else []) | |||
| }} | |||
| # Postgres is the default, except if not using `matrix_postgres` (internal postgres) | |||
| matrix_bot_buscarron_database_engine: "{{ 'postgres' if matrix_postgres_enabled else 'sqlite' }}" | |||
| matrix_bot_buscarron_database_password: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'buscarron.bot.db') | to_uuid }}" | |||
| matrix_bot_buscarron_container_image_self_build: "{{ matrix_architecture not in ['amd64', 'arm32', 'arm64'] }}" | |||
| ###################################################################### | |||
| # | |||
| # /matrix-bot-buscarron | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| @@ -1095,6 +1136,47 @@ matrix_bot_mjolnir_systemd_required_services_list: | | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| # matrix-backup-borg | |||
| # | |||
| ###################################################################### | |||
| matrix_backup_borg_enabled: false | |||
| matrix_backup_borg_container_image_self_build: "{{ matrix_architecture not in ['amd64', 'arm32', 'arm64'] }}" | |||
| matrix_backup_borg_postgresql_enabled: "{{ matrix_postgres_enabled }}" | |||
| matrix_backup_borg_postgresql_databases_hostname: "{{ matrix_postgres_connection_hostname }}" | |||
| matrix_backup_borg_postgresql_databases_username: "{{ matrix_postgres_connection_username }}" | |||
| matrix_backup_borg_postgresql_databases_password: "{{ matrix_postgres_connection_password }}" | |||
| matrix_backup_borg_postgresql_databases_port: "{{ matrix_postgres_connection_port }}" | |||
| matrix_backup_borg_postgresql_databases: | | |||
| {{ | |||
| (([{ | |||
| 'name': matrix_synapse_database_database | |||
| }] if (matrix_synapse_enabled and matrix_synapse_database_database == matrix_postgres_db_name and matrix_synapse_database_host == 'matrix-postgres') else []) | |||
| + | |||
| matrix_postgres_additional_databases)|map(attribute='name')|list | |||
| }} | |||
| matrix_backup_borg_location_source_directories: | |||
| - "{{ matrix_base_data_path }}" | |||
| matrix_backup_borg_location_exclude_patterns: | | |||
| {{ | |||
| ([matrix_synapse_media_store_path + '/local_thumbnails', matrix_synapse_media_store_path + '/remote_thumbnail', matrix_synapse_media_store_path + '/url_cache', matrix_synapse_media_store_path + '/url_cache_thumbnails'] if matrix_homeserver_implementation == 'synapse' else []) | |||
| + | |||
| ([matrix_postgres_data_path] if matrix_postgres_enabled else []) | |||
| }} | |||
| matrix_backup_borg_systemd_required_services_list: | | |||
| {{ | |||
| ['docker.service'] | |||
| + | |||
| (['matrix-postgres.service'] if matrix_postgres_enabled else []) | |||
| }} | |||
| ###################################################################### | |||
| # | |||
| # /matrix-backup-borg | |||
| # | |||
| ###################################################################### | |||
| ###################################################################### | |||
| # | |||
| @@ -1424,6 +1506,7 @@ matrix_nginx_proxy_proxy_matrix_enabled: true | |||
| matrix_nginx_proxy_proxy_element_enabled: "{{ matrix_client_element_enabled }}" | |||
| matrix_nginx_proxy_proxy_hydrogen_enabled: "{{ matrix_client_hydrogen_enabled }}" | |||
| matrix_nginx_proxy_proxy_cinny_enabled: "{{ matrix_client_cinny_enabled }}" | |||
| matrix_nginx_proxy_proxy_buscarron_enabled: "{{ matrix_bot_buscarron_enabled }}" | |||
| matrix_nginx_proxy_proxy_dimension_enabled: "{{ matrix_dimension_enabled }}" | |||
| matrix_nginx_proxy_proxy_bot_go_neb_enabled: "{{ matrix_bot_go_neb_enabled }}" | |||
| matrix_nginx_proxy_proxy_jitsi_enabled: "{{ matrix_jitsi_enabled }}" | |||
| @@ -1514,6 +1597,8 @@ matrix_nginx_proxy_systemd_wanted_services_list: | | |||
| + | |||
| (['matrix-client-cinny.service'] if matrix_client_cinny_enabled else []) | |||
| + | |||
| (['matrix-bot-buscarron.service'] if matrix_bot_buscarron_enabled else []) | |||
| + | |||
| (['matrix-client-element.service'] if matrix_client_element_enabled else []) | |||
| + | |||
| (['matrix-client-hydrogen.service'] if matrix_client_hydrogen_enabled else []) | |||
| @@ -1545,6 +1630,8 @@ matrix_ssl_domains_to_obtain_certificates_for: | | |||
| + | |||
| ([matrix_server_fqn_cinny] if matrix_client_cinny_enabled else []) | |||
| + | |||
| ([matrix_server_fqn_buscarron] if matrix_bot_buscarron_enabled else []) | |||
| + | |||
| ([matrix_server_fqn_dimension] if matrix_dimension_enabled else []) | |||
| + | |||
| ([matrix_server_fqn_bot_go_neb] if matrix_bot_go_neb_enabled else []) | |||
| @@ -1601,15 +1688,11 @@ matrix_postgres_additional_databases: | | |||
| }] if (matrix_synapse_enabled and matrix_synapse_database_database != matrix_postgres_db_name and matrix_synapse_database_host == 'matrix-postgres') else []) | |||
| + | |||
| ([{ | |||
| 'name': matrix_dendrite_naffka_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_appservice_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_federationsender_database, | |||
| 'name': matrix_dendrite_federationapi_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| @@ -1624,20 +1707,16 @@ matrix_postgres_additional_databases: | | |||
| 'name': matrix_dendrite_room_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_singingkeyserver_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_syncapi_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_account_database, | |||
| 'name': matrix_dendrite_userapi_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| 'name': matrix_dendrite_device_database, | |||
| 'name': matrix_dendrite_pushserver_database, | |||
| 'username': matrix_dendrite_database_user, | |||
| 'password': matrix_dendrite_database_password, | |||
| },{ | |||
| @@ -1664,6 +1743,12 @@ matrix_postgres_additional_databases: | | |||
| 'password': matrix_bot_honoroit_database_password, | |||
| }] if (matrix_bot_honoroit_enabled and matrix_bot_honoroit_database_engine == 'postgres' and matrix_bot_honoroit_database_hostname == 'matrix-postgres') else []) | |||
| + | |||
| ([{ | |||
| 'name': matrix_bot_buscarron_database_name, | |||
| 'username': matrix_bot_buscarron_database_username, | |||
| 'password': matrix_bot_buscarron_database_password, | |||
| }] if (matrix_bot_buscarron_enabled and matrix_bot_buscarron_database_engine == 'postgres' and matrix_bot_buscarron_database_hostname == 'matrix-postgres') else []) | |||
| + | |||
| ([{ | |||
| 'name': matrix_registration_database_name, | |||
| 'username': matrix_registration_database_username, | |||
| @@ -2281,9 +2366,9 @@ matrix_dendrite_container_https_host_bind_address: "{{ '' if matrix_nginx_proxy_ | |||
| matrix_dendrite_sync_api_real_ip_header: "{{ 'X-Forwarded-For' if matrix_nginx_proxy_enabled else '' }}" | |||
| matrix_dendrite_registration_shared_secret: "{{ matrix_homeserver_generic_secret_key | password_hash('sha512', 'dendrite.rss') | to_uuid }}" | |||
| matrix_dendrite_registration_shared_secret: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'dendrite.rss') | to_uuid }}" | |||
| matrix_dendrite_database_password: "{{ matrix_homeserver_generic_secret_key | password_hash('sha512', 'dendrite.db') | to_uuid }}" | |||
| matrix_dendrite_database_password: "{{ '%s' | format(matrix_homeserver_generic_secret_key) | password_hash('sha512', 'dendrite.db') | to_uuid }}" | |||
| # Even if TURN doesn't support TLS (it does by default), | |||
| # it doesn't hurt to try a secure connection anyway. | |||
+ 0
- 8
roles/matrix-awx/defaults/main.yml
Просмотреть файл
| @@ -1,8 +0,0 @@ | |||
| --- | |||
| matrix_awx_enabled: true | |||
| # Defaults for 'Customise Website + Access Export' template | |||
| awx_sftp_auth_method: 'Disabled' | |||
| awx_sftp_password: '' | |||
| awx_sftp_public_key: '' | |||
+ 0
- 29
roles/matrix-awx/scripts/matrix_build_room_list.py
Просмотреть файл
| @@ -1,29 +0,0 @@ | |||
| import sys | |||
| import requests | |||
| import json | |||
| janitor_token = sys.argv[1] | |||
| synapse_container_ip = sys.argv[2] | |||
| synapse_container_port = sys.argv[3] | |||
| # collect total amount of rooms | |||
| rooms_raw_url = 'http://' + synapse_container_ip + ':' + synapse_container_port + '/_synapse/admin/v1/rooms' | |||
| rooms_raw_header = {'Authorization': 'Bearer ' + janitor_token} | |||
| rooms_raw = requests.get(rooms_raw_url, headers=rooms_raw_header) | |||
| rooms_raw_python = json.loads(rooms_raw.text) | |||
| total_rooms = rooms_raw_python["total_rooms"] | |||
| # build complete room list file | |||
| room_list_file = open("/tmp/room_list_complete.json", "w") | |||
| for i in range(0, total_rooms, 100): | |||
| rooms_inc_url = 'http://' + synapse_container_ip + ':' + synapse_container_port + '/_synapse/admin/v1/rooms?from=' + str(i) | |||
| rooms_inc = requests.get(rooms_inc_url, headers=rooms_raw_header) | |||
| room_list_file.write(rooms_inc.text) | |||
| room_list_file.close() | |||
| print(total_rooms) | |||
+ 0
- 42
roles/matrix-awx/surveys/access_export.json.j2
Просмотреть файл
| @@ -1,42 +0,0 @@ | |||
| { | |||
| "name": "Access Export", | |||
| "description": "Access the services export.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "SFTP Authorisation Method", | |||
| "question_description": "Set whether you want to disable SFTP, use a password to connect to SFTP or connect with a more secure SSH key.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_sftp_auth_method | string }}", | |||
| "choices": "Disabled\nPassword\nSSH Key", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_auth_method", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "SFTP Password", | |||
| "question_description": "Sets the password of the 'sftp' account, which allows you to upload a multi-file static website by SFTP, as well as export the latest copy of your Matrix service. Must be defined if 'Password' method is selected. WARNING: You must set a strong and unique password here.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 64, | |||
| "default": "{{ awx_sftp_password }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_password", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "SFTP Public SSH Key (More Secure)", | |||
| "question_description": "Sets the public SSH key used to access the 'sftp' account, which allows you to upload a multi-file static website by SFTP, as well as export the latest copy of your Matrix service. Must be defined if 'SSH Key' method is selected.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 16384, | |||
| "default": "{{ awx_sftp_public_key }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_public_key", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 18
roles/matrix-awx/surveys/backup_server.json.j2
Просмотреть файл
| @@ -1,18 +0,0 @@ | |||
| { | |||
| "name": "Backup Server", | |||
| "description": "Performs a backup of the entire service to a remote location.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Backup", | |||
| "question_description": "Set if remote backup is enabled or not. If enabled a daily backup of your server will be sent to the backup server located in {{ backup_server_location }}.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_backup_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "awx_backup_enabled", | |||
| "type": "multiplechoice" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 66
roles/matrix-awx/surveys/bridge_discord_appservice.json.j2
Просмотреть файл
| @@ -1,66 +0,0 @@ | |||
| { | |||
| "name": "Bridge Discord Appservice", | |||
| "description": "Enables a private bridge you can use to connect Matrix rooms to Discord.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Discord AppService Bridge", | |||
| "question_description": "Enables a private bridge you can use to connect Matrix rooms to Discord.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_appservice_discord_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_appservice_discord_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Discord OAuth2 Client ID", | |||
| "question_description": "The OAuth2 'CLIENT ID' which can be found in the 'OAuth2' tab of your new discord application: https://discord.com/developers/applications", | |||
| "required": true, | |||
| "min": 0, | |||
| "max": 128, | |||
| "default": "{{ matrix_appservice_discord_client_id | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_appservice_discord_client_id", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Discord Bot Token", | |||
| "question_description": "The Bot 'TOKEN' which can be found in the 'Bot' tab of your new discord application: https://discord.com/developers/applications", | |||
| "required": true, | |||
| "min": 0, | |||
| "max": 256, | |||
| "default": "{{ matrix_appservice_discord_bot_token | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_appservice_discord_bot_token", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "Auto-Admin Matrix User", | |||
| "question_description": "The username you would like to be automatically joined and promoted to administrator (PL100) in bridged rooms. Exclude the '@' and server name postfix. So to create @stevo:example.org just enter 'stevo'.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 1024, | |||
| "default": "", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_appservice_discord_admin_user", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Auto-Admin Rooms", | |||
| "question_description": "A list of rooms you want the user to be automatically joined and promoted to administrator (PL100) in. These should be the internal IDs (for example '!axfBUsKhfAjSMBdjKX:example.org') separated by newlines.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 4096, | |||
| "default": "", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_appservice_discord_admin_rooms", | |||
| "type": "textarea" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 88
roles/matrix-awx/surveys/configure_corporal.json.j2
Просмотреть файл
| @@ -1,88 +0,0 @@ | |||
| { | |||
| "name": "Configure Matrix Corporal", | |||
| "description": "Configure Matrix Corporal, a tool that manages your Matrix server according to a configuration policy.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Corporal", | |||
| "question_description": "Controls if Matrix Corporal is enabled at all. If you're unsure if you need Matrix Corporal or not, you most likely don't.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_corporal_enabled|string|lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_corporal_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Corporal Policy Provider", | |||
| "question_description": "Controls what provider policy is used with Matrix Corporal.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_corporal_policy_provider_mode }}", | |||
| "choices": "Simple Static File\nHTTP Pull Mode (API Enabled)\nHTTP Push Mode (API Enabled)", | |||
| "new_question": true, | |||
| "variable": "awx_corporal_policy_provider_mode", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Simple Static File Configuration", | |||
| "question_description": "The configuration file for Matrix Corporal, only needed if 'Simple Static File' provider is selected, any configuration entered here will be saved and applied.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": "", | |||
| "new_question": true, | |||
| "variable": "awx_corporal_simple_static_config", | |||
| "type": "textarea" | |||
| }, | |||
| { | |||
| "question_name": "HTTP Pull Mode URI", | |||
| "question_description": "The network address to remotely fetch the configuration from. Only needed if 'HTTP Pull Mode (API Enabled)' provider is selected.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 4096, | |||
| "default": "{{ awx_corporal_pull_mode_uri }}", | |||
| "new_question": true, | |||
| "variable": "awx_corporal_pull_mode_uri", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "HTTP Pull Mode Authentication Token", | |||
| "question_description": "An authentication token for pulling the Corporal configuration from a network location. Only needed if 'HTTP Pull Mode (API Enabled)' provider is selected. WARNING: You must set a strong and unique password here.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 256, | |||
| "default": "{{ awx_corporal_pull_mode_token }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_corporal_pull_mode_token", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "Corporal API Authentication Token", | |||
| "question_description": "An authentication token for interfacing with Corporals API. Only needed to be set if 'HTTP Pull Mode (API Enabled)' or 'HTTP Push Mode (API Enabled)' provider is selected. WARNING: You must set a strong and unique password here.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 256, | |||
| "default": "{{ matrix_corporal_http_api_auth_token }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_corporal_http_api_auth_token", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "Raise Synapse Ratelimits", | |||
| "question_description": "For Matrix Corporal to work you will need to temporarily raise the rate limits for logins, please return this value to 'Normal' after you're done using Corporal.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_corporal_raise_ratelimits }}", | |||
| "choices": "Normal\nRaised", | |||
| "new_question": true, | |||
| "variable": "awx_corporal_raise_ratelimits", | |||
| "type": "multiplechoice" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 30
roles/matrix-awx/surveys/configure_dimension.json.j2
Просмотреть файл
| @@ -1,30 +0,0 @@ | |||
| { | |||
| "name": "Configure Dimension", | |||
| "description": "Configure Dimension, the self-hosted integrations server.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Dimension", | |||
| "question_description": "Enables the Dimension integration server, before doing this you need to create a CNAME record for 'dimension.{{ matrix_domain }}' that points to 'matrix.{{ matrix_domain }}'.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_dimension_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_dimension_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Dimension Users", | |||
| "question_description": "Here you can list the user accounts that will be able to configure Dimension. Entries must be seperated with newlines and must be a complete Matrix ID. For example: '@dimension:{{ matrix_domain }}'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": {{ awx_dimension_users_final | to_json }}, | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_dimension_users", | |||
| "type": "textarea" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 114
roles/matrix-awx/surveys/configure_element.json.j2
Просмотреть файл
| @@ -1,114 +0,0 @@ | |||
| { | |||
| "name": "Configure Element", | |||
| "description": "Configure Element web client, Element is the most developed Matrix client software.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Element-Web", | |||
| "question_description": "Set if Element web client is enabled or not.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_client_element_enabled }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Set Theme for Web Client", | |||
| "question_description": "Sets the default theme for the web client, can be changed later by individual users.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_client_element_default_theme }}", | |||
| "choices": "light\ndark", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_default_theme", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Set Branding for Web Client", | |||
| "question_description": "Sets the 'branding' seen in the tab and on the welcome page to a custom value.Leaving this field blank will cause the default branding will be used: 'Element'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 256, | |||
| "default": "{{ matrix_client_element_brand | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_brand", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Set Welcome Page Background", | |||
| "question_description": "Sets the background image on the welcome page, you should enter a URL to the image you want to use. Must be a 'https' link, otherwise it won't be set. Leaving this field blank will cause the default background to be used.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 1024, | |||
| "default": "{{ matrix_client_element_branding_welcomeBackgroundUrl | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_branding_welcomeBackgroundUrl", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Set Welcome Page Logo", | |||
| "question_description": "Sets the logo found on the welcome and login page, must be a valid https link to your logo, the logo itself should be a square vector image (SVG). Leaving this field blank will cause the default Element logo to be used.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 1024, | |||
| "default": "{{ matrix_client_element_welcome_logo | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_welcome_logo", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Set Welcome Page Logo URL", | |||
| "question_description": "Sets the URL link the welcome page logo leads to, must be a valid https link. Leaving this field blank will cause this default link to be used: 'https://element.io'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 1024, | |||
| "default": "{{ matrix_client_element_welcome_logo_link | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_welcome_logo_link", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Set Welcome Page Headline", | |||
| "question_description": "Sets the headline seen on the welcome page. Leaving this field blank will cause this default headline to be used: 'Welcome to Element!'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 512, | |||
| "default": "{{ awx_matrix_client_element_welcome_headline | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_matrix_client_element_welcome_headline", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Set Welcome Page Text", | |||
| "question_description": "Sets the text seen on the welcome page. Leaving this field blank will cause this default headline to be used: 'Decentralised, encrypted chat & collaboration powered by [Matrix]'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 2048, | |||
| "default": "{{ awx_matrix_client_element_welcome_text | trim }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_matrix_client_element_welcome_text", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Show Registration Button", | |||
| "question_description": "If you show the registration button on the welcome page.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_client_element_registration_enabled }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_client_element_registration_enabled", | |||
| "type": "multiplechoice" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 18
roles/matrix-awx/surveys/configure_element_subdomain.json.j2
Просмотреть файл
| @@ -1,18 +0,0 @@ | |||
| { | |||
| "name": "Configure Element Subdomain", | |||
| "description": "Configure Element clients subdomain location. (Eg: 'element' for element.example.org)", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Set Element Subdomain", | |||
| "question_description": "Sets the subdomain of the Element web-client, you should only specify the subdomain, not the base domain you've already set. (Eg: 'element' for element.example.org) Note that if you change this value you'll need to reconfigure your DNS.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 2048, | |||
| "default": "{{ awx_element_subdomain }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_element_subdomain", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 19
roles/matrix-awx/surveys/configure_email_relay.json.j2
Просмотреть файл
| @@ -1,19 +0,0 @@ | |||
| { | |||
| "name": "Configure Email Relay", | |||
| "description": "Enable MailGun relay to increase verification email reliability.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Email Relay", | |||
| "question_description": "Enables the MailGun email relay server, enabling this will increase the reliability of your email verification.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_mailer_relay_use | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_mailer_relay_use", | |||
| "type": "multiplechoice" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 31
roles/matrix-awx/surveys/configure_jitsi.json.j2
Просмотреть файл
| @@ -1,31 +0,0 @@ | |||
| { | |||
| "name": "Configure Jitsi", | |||
| "description": "Configure Jitsi conferencing settings.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Jitsi", | |||
| "question_description": "Set if Jitsi is enabled or not. If disabled your server will use the https://jitsi.riot.im server. If you're on a smaller server disabling this might increase the performance of your Matrix service.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_jitsi_enabled }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_jitsi_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Set Default Language", | |||
| "question_description": "2 digit 639-1 language code to adjust the language of the web client. For a list of possible codes see: https://en.wikipedia.org/wiki/List_of_ISO_639-1_codes", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 2, | |||
| "default": "{{ matrix_jitsi_web_config_defaultLanguage }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "matrix_jitsi_web_config_defaultLanguage", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 41
roles/matrix-awx/surveys/configure_ma1sd.json.j2
Просмотреть файл
| @@ -1,41 +0,0 @@ | |||
| { | |||
| "name": "Configure ma1sd", | |||
| "description": "Configure ma1sd settings, ma1sd is a self-hosted identity server for Matrix.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable ma1sd", | |||
| "question_description": "Set if ma1sd is enabled or not. If disabled your server will loose identity functionality (not recommended).", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_ma1sd_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_ma1sd_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "ma1sd Authentication Mode", | |||
| "question_description": "Set the source of user account authentication credentials with the ma1sd.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_matrix_ma1sd_auth_store }}", | |||
| "choices": "Synapse Internal\nLDAP/AD", | |||
| "new_question": true, | |||
| "variable": "awx_matrix_ma1sd_auth_store", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "LDAP/AD Configuration", | |||
| "question_description": "Settings for connecting LDAP/AD to the ma1sd service. (ignored if using Synapse Internal, see https://github.com/ma1uta/ma1sd/blob/master/docs/stores/README.md )", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": {{ awx_matrix_ma1sd_configuration_extension_yaml | to_json }}, | |||
| "new_question": true, | |||
| "variable": "awx_matrix_ma1sd_configuration_extension_yaml", | |||
| "type": "textarea" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 29
roles/matrix-awx/surveys/configure_mjolnir.json.j2
Просмотреть файл
| @@ -1,29 +0,0 @@ | |||
| { | |||
| "name": "Configure Mjolnir", | |||
| "description": "Configure Mjolnir settings, Mjolnir is a moderation bot for Matrix.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Mjolnir", | |||
| "question_description": "Set if Mjolnir is enabled or not. Mjolnir is a moderation bot for Matrix.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_bot_mjolnir_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_bot_mjolnir_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Mjolnir Management Room", | |||
| "question_description": "Sets the internal ID of the management room for Mjolnir. Example: '!wAeZaPCKvaCHcSqxAW:matrix.org'", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_bot_mjolnir_management_room }}", | |||
| "new_question": true, | |||
| "variable": "matrix_bot_mjolnir_management_room", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 198
roles/matrix-awx/surveys/configure_synapse.json.j2
Просмотреть файл
| @@ -1,198 +0,0 @@ | |||
| { | |||
| "name": "Configure Synapse", | |||
| "description": "Configure Synapse settings. Synapse is the homeserver software that powers your Matrix instance.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Public Registration", | |||
| "question_description": "Controls whether people with access to the homeserver can register by themselves.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_enable_registration | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_enable_registration", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Enable Federation", | |||
| "question_description": "Controls whether Synapse will federate at all. Disable this to completely isolate your server from the rest of the Matrix network.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_federation_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_federation_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Allow Public Rooms Over Federation", | |||
| "question_description": "Controls whether remote servers can fetch this server's public rooms directory via federation. For private servers, you'll most likely want to forbid this.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_allow_public_rooms_over_federation | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_allow_public_rooms_over_federation", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Enable Community Creation", | |||
| "question_description": "Allows regular users (who aren't server admins) to create 'communities', which are basically groups of rooms.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_enable_group_creation | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_enable_group_creation", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Enable Synapse Presence", | |||
| "question_description": "Controls whether presence is enabled. This shows who's online and reading your posts. Disabling it will increase both performance and user privacy.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_presence_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_presence_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Enable URL Previews", | |||
| "question_description": "Controls whether URL previews should be generated. This will cause a request from Synapse to URLs shared by users.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_url_preview_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_url_preview_enabled", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Enable Guest Access", | |||
| "question_description": "Controls whether 'guest accounts' can access rooms without registering. Guest users do not count towards your servers user limit.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_allow_guest_access | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_allow_guest_access", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Registration Requires Email", | |||
| "question_description": "Controls whether an email address is required to register on the server.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_registrations_require_3pid | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "awx_registrations_require_3pid", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Registration Shared Secret", | |||
| "question_description": "A secret that allows registration of standard or admin accounts by anyone who has the shared secret, even if registration is otherwise disabled. WARNING: You must set a strong and unique password here.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 256, | |||
| "default": "", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_matrix_synapse_registration_shared_secret", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "Synapse Max Upload Size", | |||
| "question_description": "Sets the maximum size for uploaded files in MB.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 3, | |||
| "default": "{{ matrix_synapse_max_upload_size_mb }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_synapse_max_upload_size_mb", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "URL Preview Languages", | |||
| "question_description": "Sets the languages that URL previews will be generated in. Entries are a 2-3 letter IETF language tag, they must be seperated with newlines. For example: 'fr' https://en.wikipedia.org/wiki/IETF_language_tag", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": {{ awx_url_preview_accept_language_default | to_json }}, | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_url_preview_accept_language", | |||
| "type": "textarea" | |||
| }, | |||
| { | |||
| "question_name": "Federation Whitelist", | |||
| "question_description": "Here you can list the URLs of other Matrix homeservers and Synapse will only federate with those homeservers. Entries must be seperated with newlines and must not have a 'https://' prefix. For example: 'matrix.example.org'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": {{ awx_federation_whitelist | to_json }}, | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_federation_whitelist", | |||
| "type": "textarea" | |||
| }, | |||
| { | |||
| "question_name": "Synapse Auto-Join Rooms", | |||
| "question_description": "Sets the 'auto-join' rooms, where new users will be automatically invited to, these rooms must already exist. Entries must be room addresses that are separated with newlines. For example: '#announcements:example.org'", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 65536, | |||
| "default": {{ awx_synapse_auto_join_rooms | to_json }}, | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_synapse_auto_join_rooms", | |||
| "type": "textarea" | |||
| }, | |||
| { | |||
| "question_name": "Enable ReCaptcha on Registration", | |||
| "question_description": "Enables Googles ReCaptcha verification for registering an account, recommended for public servers.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_enable_registration_captcha | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "awx_enable_registration_captcha", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "Recaptcha Public Key", | |||
| "question_description": "Sets the Google ReCaptcha public key for this website.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 40, | |||
| "default": "{{ awx_recaptcha_public_key }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_recaptcha_public_key", | |||
| "type": "text" | |||
| }, | |||
| { | |||
| "question_name": "Recaptcha Private Key", | |||
| "question_description": "Sets the Google ReCaptcha private key for this website.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 40, | |||
| "default": "{{ awx_recaptcha_private_key }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_recaptcha_private_key", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 18
roles/matrix-awx/surveys/configure_synapse_admin.json.j2
Просмотреть файл
| @@ -1,18 +0,0 @@ | |||
| { | |||
| "name": "Configure Synapse Admin", | |||
| "description": "Configure 'Synapse Admin', a moderation tool to help you manage your server.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Enable Synapse Admin", | |||
| "question_description": "Set if Synapse Admin is enabled or not. If enabled you can access it at https://{{ matrix_server_fqn_matrix }}/synapse-admin.", | |||
| "required": false, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ matrix_synapse_admin_enabled | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "matrix_synapse_admin_enabled", | |||
| "type": "multiplechoice" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 54
roles/matrix-awx/surveys/configure_website_access_export.json.j2
Просмотреть файл
| @@ -1,54 +0,0 @@ | |||
| { | |||
| "name": "Configure Website Access Backup", | |||
| "description": "Configure base domain website settings and access the services backup.", | |||
| "spec": [ | |||
| { | |||
| "question_name": "Customise Base Domain Website", | |||
| "question_description": "Set if you want to adjust the base domain website using SFTP.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_customise_base_domain_website | string | lower }}", | |||
| "choices": "true\nfalse", | |||
| "new_question": true, | |||
| "variable": "awx_customise_base_domain_website", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "SFTP Authorisation Method", | |||
| "question_description": "Set whether you want to disable SFTP, use a password to connect to SFTP or connect with a more secure SSH key.", | |||
| "required": true, | |||
| "min": null, | |||
| "max": null, | |||
| "default": "{{ awx_sftp_auth_method | string }}", | |||
| "choices": "Disabled\nPassword\nSSH Key", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_auth_method", | |||
| "type": "multiplechoice" | |||
| }, | |||
| { | |||
| "question_name": "SFTP Password", | |||
| "question_description": "Sets the password of the 'sftp' account, which allows you to upload a multi-file static website by SFTP, as well as export the latest copy of your Matrix service. Must be defined if 'Password' method is selected. WARNING: You must set a strong and unique password here.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 64, | |||
| "default": "{{ awx_sftp_password }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_password", | |||
| "type": "password" | |||
| }, | |||
| { | |||
| "question_name": "SFTP Public SSH Key (More Secure)", | |||
| "question_description": "Sets the public SSH key used to access the 'sftp' account, which allows you to upload a multi-file static website by SFTP, as well as export the latest copy of your Matrix service. Must be defined if 'SSH Key' method is selected.", | |||
| "required": false, | |||
| "min": 0, | |||
| "max": 16384, | |||
| "default": "{{ awx_sftp_public_key }}", | |||
| "choices": "", | |||
| "new_question": true, | |||
| "variable": "awx_sftp_public_key", | |||
| "type": "text" | |||
| } | |||
| ] | |||
| } | |||
+ 0
- 101
roles/matrix-awx/tasks/backup_server.yml
Просмотреть файл
| @@ -1,101 +0,0 @@ | |||
| --- | |||
| - name: Record Backup Server variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# AWX Settings Start' | |||
| with_dict: | |||
| 'awx_backup_enabled': '{{ awx_backup_enabled }}' | |||
| tags: use-survey | |||
| - name: Save new 'Backup Server' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/backup_server.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/backup_server.json' | |||
| tags: use-survey | |||
| - name: Copy new 'Backup Server' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/backup_server.json' | |||
| dest: '/matrix/awx/backup_server.json' | |||
| mode: '0660' | |||
| tags: use-survey | |||
| - name: Recreate 'Backup Server' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 0 - Backup Server" | |||
| description: "Performs a backup of the entire service to a remote location." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "backup-server,use-survey" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/backup_server.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| tags: use-survey | |||
| - name: Include vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| no_log: true | |||
| - name: Copy new 'matrix_vars.yml' to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| dest: '/matrix/awx/matrix_vars.yml' | |||
| mode: '0660' | |||
| tags: use-survey | |||
| - name: Run initial backup of /matrix/ and snapshot the database simultaneously | |||
| command: "{{ item }}" | |||
| with_items: | |||
| - borgmatic -c /root/.config/borgmatic/config_1.yaml | |||
| - /bin/sh /usr/local/bin/awx-export-service.sh 1 0 | |||
| register: _create_instances | |||
| async: 3600 # Maximum runtime in seconds. | |||
| poll: 0 # Fire and continue (never poll) | |||
| when: awx_backup_enabled|bool | |||
| - name: Wait for both of these jobs to finish | |||
| async_status: | |||
| jid: "{{ item.ansible_job_id }}" | |||
| register: _jobs | |||
| until: _jobs.finished | |||
| delay: 5 # Check every 5 seconds. | |||
| retries: 720 # Retry for a full hour. | |||
| with_items: "{{ _create_instances.results }}" | |||
| when: awx_backup_enabled|bool | |||
| - name: Perform borg backup of postgres dump | |||
| command: borgmatic -c /root/.config/borgmatic/config_2.yaml | |||
| when: awx_backup_enabled|bool | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| awx_end_playbook: true | |||
| - name: End playbook if this task list is called. | |||
| meta: end_play | |||
| when: awx_end_playbook is defined and awx_end_playbook|bool | |||
+ 0
- 58
roles/matrix-awx/tasks/bridge_discord_appservice.yml
Просмотреть файл
| @@ -1,58 +0,0 @@ | |||
| --- | |||
| - name: Record Bridge Discord AppService variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Bridge Discord AppService Start' | |||
| with_dict: | |||
| 'matrix_appservice_discord_enabled': '{{ matrix_appservice_discord_enabled }}' | |||
| 'matrix_appservice_discord_client_id': '{{ matrix_appservice_discord_client_id }}' | |||
| 'matrix_appservice_discord_bot_token': '{{ matrix_appservice_discord_bot_token }}' | |||
| - name: If the raw inputs is not empty start constructing parsed awx_appservice_discord_admin_rooms list | |||
| set_fact: | |||
| awx_appservice_discord_admin_rooms_array: |- | |||
| {{ awx_appservice_discord_admin_rooms.splitlines() | to_json }} | |||
| when: awx_appservice_discord_admin_rooms | trim | length > 0 | |||
| - name: Promote user to administer (PL100) of each room | |||
| command: | | |||
| docker exec -i matrix-appservice-discord /bin/sh -c 'cp /cfg/registration.yaml /tmp/discord-registration.yaml && cd /tmp && node /build/tools/adminme.js -c /cfg/config.yaml -m "{{ item.1 }}" -u "@{{ awx_appservice_discord_admin_user }}:{{ matrix_domain }}" -p 100' | |||
| with_indexed_items: | |||
| - "{{ awx_appservice_discord_admin_rooms_array }}" | |||
| when: ( awx_appservice_discord_admin_rooms | trim | length > 0 ) and ( awx_appservice_discord_admin_user is defined ) | |||
| - name: Save new 'Bridge Discord Appservice' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/bridge_discord_appservice.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}//bridge_discord_appservice.json' | |||
| - name: Copy new 'Bridge Discord Appservice' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/bridge_discord_appservice.json' | |||
| dest: '/matrix/awx/bridge_discord_appservice.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Bridge Discord Appservice' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 3 - Bridge Discord AppService" | |||
| description: "Enables a private bridge you can use to connect Matrix rooms to Discord." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-all,bridge-discord-appservice" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/bridge_discord_appservice.json') }}" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 13
roles/matrix-awx/tasks/cache_matrix_variables.yml
Просмотреть файл
| @@ -1,13 +0,0 @@ | |||
| --- | |||
| - name: Collect current datetime | |||
| set_fact: | |||
| awx_datetime: "{{ lookup('pipe', 'date +%Y-%m-%d_%H:%M') }}" | |||
| - name: Create cached matrix_vars.yml file location | |||
| set_fact: | |||
| awx_cached_matrix_vars: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars_{{ awx_datetime }}.yml' | |||
| - name: Create cached matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| shell: "cp /var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml {{ awx_cached_matrix_vars }}" | |||
+ 0
- 11
roles/matrix-awx/tasks/create_session_token.yml
Просмотреть файл
| @@ -1,11 +0,0 @@ | |||
| --- | |||
| - name: Create a AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: present | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_master_token }}" | |||
| register: awx_session_token | |||
| no_log: true | |||
+ 0
- 41
roles/matrix-awx/tasks/create_user.yml
Просмотреть файл
| @@ -1,41 +0,0 @@ | |||
| --- | |||
| # | |||
| # Create user and define if they are admin | |||
| # | |||
| # /usr/local/bin/matrix-synapse-register-user <your_username> <your_password> <admin access: 0 or 1> | |||
| # | |||
| - name: Set admin bool to zero | |||
| set_fact: | |||
| awx_admin_bool: 0 | |||
| when: awx_admin_access == 'false' | |||
| - name: Examine if server admin set | |||
| set_fact: | |||
| awx_admin_bool: 1 | |||
| when: awx_admin_access == 'true' | |||
| - name: Create user account | |||
| command: | | |||
| /usr/local/bin/matrix-synapse-register-user {{ awx_new_username | quote }} {{ awx_new_password | quote }} {{ awx_admin_bool }} | |||
| register: awx_cmd_output | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| awx_end_playbook: true | |||
| - name: Result | |||
| debug: msg="{{ awx_cmd_output.stdout }}" | |||
| - name: End playbook if this task list is called. | |||
| meta: end_play | |||
| when: awx_end_playbook is defined and awx_end_playbook|bool | |||
+ 0
- 267
roles/matrix-awx/tasks/customise_website_access_export.yml
Просмотреть файл
| @@ -1,267 +0,0 @@ | |||
| --- | |||
| - name: Enable index.html creation if user doesn't wish to customise base domain | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Base Domain Settings Start' | |||
| with_dict: | |||
| 'matrix_nginx_proxy_base_domain_homepage_enabled': 'true' | |||
| when: (awx_customise_base_domain_website is defined) and not awx_customise_base_domain_website|bool | |||
| - name: Disable index.html creation to allow multi-file site if user does wish to customise base domain | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Base Domain Settings Start' | |||
| with_dict: | |||
| 'matrix_nginx_proxy_base_domain_homepage_enabled': 'false' | |||
| when: (awx_customise_base_domain_website is defined) and awx_customise_base_domain_website|bool | |||
| - name: Record custom 'Customise Website + Access Export' variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Custom Settings Start' | |||
| with_dict: | |||
| 'awx_sftp_auth_method': '"{{ awx_sftp_auth_method }}"' | |||
| 'awx_sftp_password': '"{{ awx_sftp_password }}"' | |||
| 'awx_sftp_public_key': '"{{ awx_sftp_public_key }}"' | |||
| - name: Record custom 'Customise Website + Access Export' variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Custom Settings Start' | |||
| with_dict: | |||
| 'awx_customise_base_domain_website': '{{ awx_customise_base_domain_website }}' | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Reload vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '{{ awx_cached_matrix_vars }}' | |||
| no_log: true | |||
| - name: Save new 'Customise Website + Access Export' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: './roles/matrix-awx/surveys/configure_website_access_export.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_website_access_export.json' | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Copy new 'Customise Website + Access Export' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_website_access_export.json' | |||
| dest: '/matrix/awx/configure_website_access_export.json' | |||
| mode: '0660' | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Save new 'Customise Website + Access Export' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: './roles/matrix-awx/surveys/access_export.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/access_export.json' | |||
| when: awx_customise_base_domain_website is undefined | |||
| - name: Copy new 'Customise Website + Access Export' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/access_export.json' | |||
| dest: '/matrix/awx/access_export.json' | |||
| mode: '0660' | |||
| when: awx_customise_base_domain_website is undefined | |||
| - name: Recreate 'Configure Website + Access Export' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Website + Access Export" | |||
| description: "Configure base domain website settings and access the servers export." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-nginx-proxy" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_website_access_export.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Recreate 'Access Export' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Access Export" | |||
| description: "Access the services export." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-nginx-proxy" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/access_export.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: awx_customise_base_domain_website is undefined | |||
| - name: If user doesn't define a awx_sftp_password, create a disabled 'sftp' account | |||
| user: | |||
| name: sftp | |||
| comment: SFTP user to set custom web files and access servers export | |||
| shell: /bin/false | |||
| home: /home/sftp | |||
| group: matrix | |||
| password: '*' | |||
| update_password: always | |||
| when: awx_sftp_password|length == 0 | |||
| - name: If user defines awx_sftp_password, enable account and set password on 'stfp' account | |||
| user: | |||
| name: sftp | |||
| comment: SFTP user to set custom web files and access servers export | |||
| shell: /bin/false | |||
| home: /home/sftp | |||
| group: matrix | |||
| password: "{{ awx_sftp_password | password_hash('sha512') }}" | |||
| update_password: always | |||
| when: awx_sftp_password|length > 0 | |||
| - name: Ensure group "sftp" exists | |||
| group: | |||
| name: sftp | |||
| state: present | |||
| - name: adding existing user 'sftp' to group matrix | |||
| user: | |||
| name: sftp | |||
| groups: sftp | |||
| append: true | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Create the ro /chroot directory with sticky bit if it doesn't exist. (/chroot/website has matrix:matrix permissions and is mounted to nginx container) | |||
| file: | |||
| path: /chroot | |||
| state: directory | |||
| owner: root | |||
| group: root | |||
| mode: '1755' | |||
| - name: Ensure /chroot/website location exists. | |||
| file: | |||
| path: /chroot/website | |||
| state: directory | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '0770' | |||
| when: awx_customise_base_domain_website is defined | |||
| - name: Ensure /chroot/export location exists | |||
| file: | |||
| path: /chroot/export | |||
| state: directory | |||
| owner: sftp | |||
| group: sftp | |||
| mode: '0700' | |||
| - name: Ensure /home/sftp/.ssh location exists | |||
| file: | |||
| path: /home/sftp/.ssh | |||
| state: directory | |||
| owner: sftp | |||
| group: sftp | |||
| mode: '0700' | |||
| - name: Ensure /home/sftp/authorized_keys exists | |||
| file: | |||
| path: /home/sftp/.ssh/authorized_keys | |||
| state: touch | |||
| owner: sftp | |||
| group: sftp | |||
| mode: '0644' | |||
| - name: Clear authorized_keys file | |||
| shell: echo "" > /home/sftp/.ssh/authorized_keys | |||
| - name: Insert public SSH key into authorized_keys file | |||
| lineinfile: | |||
| path: /home/sftp/.ssh/authorized_keys | |||
| line: "{{ awx_sftp_public_key }}" | |||
| owner: sftp | |||
| group: sftp | |||
| mode: '0644' | |||
| when: (awx_sftp_public_key | length > 0) and (awx_sftp_auth_method == "SSH Key") | |||
| - name: Remove any existing Subsystem lines | |||
| lineinfile: | |||
| path: /etc/ssh/sshd_config | |||
| state: absent | |||
| regexp: '^Subsystem' | |||
| - name: Set SSH Subsystem State | |||
| lineinfile: | |||
| path: /etc/ssh/sshd_config | |||
| insertafter: "^# override default of no subsystems" | |||
| line: "Subsystem sftp internal-sftp" | |||
| - name: Add SSH Match User section for disabled auth | |||
| blockinfile: | |||
| path: /etc/ssh/sshd_config | |||
| state: absent | |||
| block: | | |||
| Match User sftp | |||
| ChrootDirectory /chroot | |||
| PermitTunnel no | |||
| X11Forwarding no | |||
| AllowTcpForwarding no | |||
| PasswordAuthentication yes | |||
| AuthorizedKeysFile /home/sftp/.ssh/authorized_keys | |||
| when: awx_sftp_auth_method == "Disabled" | |||
| - name: Add SSH Match User section for password auth | |||
| blockinfile: | |||
| path: /etc/ssh/sshd_config | |||
| state: present | |||
| block: | | |||
| Match User sftp | |||
| ChrootDirectory /chroot | |||
| PermitTunnel no | |||
| X11Forwarding no | |||
| AllowTcpForwarding no | |||
| PasswordAuthentication yes | |||
| when: awx_sftp_auth_method == "Password" | |||
| - name: Add SSH Match User section for publickey auth | |||
| blockinfile: | |||
| path: /etc/ssh/sshd_config | |||
| state: present | |||
| block: | | |||
| Match User sftp | |||
| ChrootDirectory /chroot | |||
| PermitTunnel no | |||
| X11Forwarding no | |||
| AllowTcpForwarding no | |||
| AuthorizedKeysFile /home/sftp/.ssh/authorized_keys | |||
| when: awx_sftp_auth_method == "SSH Key" | |||
| - name: Restart service ssh.service | |||
| service: | |||
| name: ssh.service | |||
| state: restarted | |||
+ 0
- 10
roles/matrix-awx/tasks/delete_session_token.yml
Просмотреть файл
| @@ -1,10 +0,0 @@ | |||
| --- | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
+ 0
- 43
roles/matrix-awx/tasks/export_server.yml
Просмотреть файл
| @@ -1,43 +0,0 @@ | |||
| --- | |||
| - name: Run export of /matrix/ and snapshot the database simultaneously | |||
| command: "{{ item }}" | |||
| with_items: | |||
| - /bin/sh /usr/local/bin/awx-export-service.sh 1 0 | |||
| - /bin/sh /usr/local/bin/awx-export-service.sh 0 1 | |||
| register: awx_create_instances | |||
| async: 3600 # Maximum runtime in seconds. | |||
| poll: 0 # Fire and continue (never poll) | |||
| - name: Wait for both of these jobs to finish | |||
| async_status: | |||
| jid: "{{ item.ansible_job_id }}" | |||
| register: awx_jobs | |||
| until: awx_jobs.finished | |||
| delay: 5 # Check every 5 seconds. | |||
| retries: 720 # Retry for a full hour. | |||
| with_items: "{{ awx_create_instances.results }}" | |||
| - name: Schedule deletion of the export in 24 hours | |||
| at: | |||
| command: rm /chroot/export/matrix* | |||
| count: 1 | |||
| units: days | |||
| unique: true | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| awx_end_playbook: true | |||
| - name: End playbook if this task list is called. | |||
| meta: end_play | |||
| when: awx_end_playbook is defined and awx_end_playbook|bool | |||
+ 0
- 7
roles/matrix-awx/tasks/import_awx.yml
Просмотреть файл
| @@ -1,7 +0,0 @@ | |||
| --- | |||
| - name: Ensure correct ownership of /matrix/awx | |||
| shell: chown -R matrix:matrix /matrix/awx | |||
| - name: Ensure correct ownership of /matrix/synapse | |||
| shell: chown -R matrix:matrix /matrix/synapse | |||
+ 0
- 16
roles/matrix-awx/tasks/load_hosting_and_org_variables.yml
Просмотреть файл
| @@ -1,16 +0,0 @@ | |||
| --- | |||
| - name: Include vars in organisation.yml | |||
| include_vars: | |||
| file: '/var/lib/awx/projects/clients/{{ member_id }}/organisation.yml' | |||
| no_log: true | |||
| - name: Include vars in hosting_vars.yml | |||
| include_vars: | |||
| file: '/var/lib/awx/projects/hosting/hosting_vars.yml' | |||
| no_log: true | |||
| - name: Include AWX master token from awx_tokens.yml | |||
| include_vars: | |||
| file: /var/lib/awx/projects/hosting/awx_tokens.yml | |||
| no_log: true | |||
+ 0
- 16
roles/matrix-awx/tasks/load_matrix_variables.yml
Просмотреть файл
| @@ -1,16 +0,0 @@ | |||
| --- | |||
| - name: Include new vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '{{ awx_cached_matrix_vars }}' | |||
| no_log: true | |||
| - name: If include_vars succeeds overwrite the old matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| shell: "cp {{ awx_cached_matrix_vars }} /var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml && rm {{ awx_cached_matrix_vars }}" | |||
| - name: Copy new 'matrix_vars.yml' to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| dest: '/matrix/awx/matrix_vars.yml' | |||
| mode: '0660' | |||
+ 0
- 234
roles/matrix-awx/tasks/main.yml
Просмотреть файл
| @@ -1,234 +0,0 @@ | |||
| --- | |||
| # Load initial hosting and organisation variables from AWX volume | |||
| - include_tasks: | |||
| file: "load_hosting_and_org_variables.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
| # Renames or updates the vars.yml if needed | |||
| - include_tasks: | |||
| file: "update_variables.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
| # Create AWX session token | |||
| - include_tasks: | |||
| file: "create_session_token.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
| # Perform a backup of the server | |||
| - include_tasks: | |||
| file: "backup_server.yml" | |||
| apply: | |||
| tags: backup-server | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - backup-server | |||
| # Perform a export of the server | |||
| - include_tasks: | |||
| file: "export_server.yml" | |||
| apply: | |||
| tags: export-server | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - export-server | |||
| # Create a user account if called | |||
| - include_tasks: | |||
| file: "create_user.yml" | |||
| apply: | |||
| tags: create-user | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - create-user | |||
| # Purge local/remote media if called | |||
| - include_tasks: | |||
| file: "purge_media_main.yml" | |||
| apply: | |||
| tags: purge-media | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - purge-media | |||
| # Purge Synapse database if called | |||
| - include_tasks: | |||
| file: "purge_database_main.yml" | |||
| apply: | |||
| tags: purge-database | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - purge-database | |||
| # Rotate SSH key if called | |||
| - include_tasks: | |||
| file: "rotate_ssh.yml" | |||
| apply: | |||
| tags: rotate-ssh | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - rotate-ssh | |||
| # Import configs, media repo from /chroot/backup import | |||
| - include_tasks: | |||
| file: "import_awx.yml" | |||
| apply: | |||
| tags: import-awx | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - import-awx | |||
| # Perform extra self-check functions | |||
| - include_tasks: | |||
| file: "self_check.yml" | |||
| apply: | |||
| tags: self-check | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - self-check | |||
| # Create cached matrix_vars.yml file | |||
| - include_tasks: | |||
| file: "cache_matrix_variables.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
| # Configure SFTP so user can upload a static website or access the servers export | |||
| - include_tasks: | |||
| file: "customise_website_access_export.yml" | |||
| apply: | |||
| tags: setup-nginx-proxy | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-nginx-proxy | |||
| # Additional playbook to set the variable file during Element configuration | |||
| - include_tasks: | |||
| file: "set_variables_element.yml" | |||
| apply: | |||
| tags: setup-client-element | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-client-element | |||
| # Additional playbook to set the variable file during Mailer configuration | |||
| - include_tasks: | |||
| file: "set_variables_mailer.yml" | |||
| apply: | |||
| tags: setup-mailer | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-mailer | |||
| # Additional playbook to set the variable file during Element configuration | |||
| - include_tasks: | |||
| file: "set_variables_element_subdomain.yml" | |||
| apply: | |||
| tags: setup-client-element-subdomain | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-client-element-subdomain | |||
| # Additional playbook to set the variable file during Synapse configuration | |||
| - include_tasks: | |||
| file: "set_variables_synapse.yml" | |||
| apply: | |||
| tags: setup-synapse | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-synapse | |||
| # Additional playbook to set the variable file during Jitsi configuration | |||
| - include_tasks: | |||
| file: "set_variables_jitsi.yml" | |||
| apply: | |||
| tags: setup-jitsi | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-jitsi | |||
| # Additional playbook to set the variable file during Ma1sd configuration | |||
| - include_tasks: | |||
| file: "set_variables_ma1sd.yml" | |||
| apply: | |||
| tags: setup-ma1sd | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-ma1sd | |||
| # Additional playbook to set the variable file during Mjolnir Bot configuration | |||
| - include_tasks: | |||
| file: "set_variables_mjolnir.yml" | |||
| apply: | |||
| tags: setup-bot-mjolnir | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-bot-mjolnir | |||
| # Additional playbook to set the variable file during Corporal configuration | |||
| - include_tasks: | |||
| file: "set_variables_corporal.yml" | |||
| apply: | |||
| tags: setup-corporal | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-corporal | |||
| # Additional playbook to set the variable file during Dimension configuration | |||
| - include_tasks: | |||
| file: "set_variables_dimension.yml" | |||
| apply: | |||
| tags: setup-dimension | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-dimension | |||
| # Additional playbook to set the variable file during Synapse Admin configuration | |||
| - include_tasks: | |||
| file: "set_variables_synapse_admin.yml" | |||
| apply: | |||
| tags: setup-synapse-admin | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - setup-synapse-admin | |||
| # Additional playbook to set the variable file during Discord Appservice Bridge configuration | |||
| - include_tasks: | |||
| file: "bridge_discord_appservice.yml" | |||
| apply: | |||
| tags: bridge-discord-appservice | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - bridge-discord-appservice | |||
| # Delete AWX session token | |||
| - include_tasks: | |||
| file: "delete_session_token.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
| # Load newly formed matrix variables from AWX volume | |||
| - include_tasks: | |||
| file: "load_matrix_variables.yml" | |||
| apply: | |||
| tags: always | |||
| when: run_setup|bool and matrix_awx_enabled|bool | |||
| tags: | |||
| - always | |||
+ 0
- 14
roles/matrix-awx/tasks/purge_database_events.yml
Просмотреть файл
| @@ -1,14 +0,0 @@ | |||
| --- | |||
| - name: Purge all rooms with more then N events | |||
| shell: | | |||
| curl --header "Authorization: Bearer {{ awx_janitors_token.stdout[1:-1] }}" -X POST -H "Content-Type: application/json" -d '{ "delete_local_events": false, "purge_up_to_ts": {{ awx_purge_epoche_time.stdout }}000 }' "{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_synapse/admin/v1/purge_history/{{ item[1:-1] }}" | |||
| register: awx_purge_command | |||
| - name: Print output of purge command | |||
| debug: | |||
| msg: "{{ awx_purge_command.stdout }}" | |||
| - name: Pause for 5 seconds to let Synapse breathe | |||
| pause: | |||
| seconds: 5 | |||
+ 0
- 320
roles/matrix-awx/tasks/purge_database_main.yml
Просмотреть файл
| @@ -1,320 +0,0 @@ | |||
| --- | |||
| - name: Ensure dateutils and curl is installed in AWX | |||
| delegate_to: 127.0.0.1 | |||
| yum: | |||
| name: dateutils | |||
| state: latest | |||
| - name: Include vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| no_log: true | |||
| - name: Ensure curl and jq intalled on target machine | |||
| apt: | |||
| pkg: | |||
| - curl | |||
| - jq | |||
| state: present | |||
| - name: Collect before shrink size of Synapse database | |||
| shell: du -sh /matrix/postgres/data | |||
| register: awx_db_size_before_stat | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| no_log: true | |||
| - name: Collect the internal IP of the matrix-synapse container | |||
| shell: "/usr/bin/docker inspect --format '{''{range.NetworkSettings.Networks}''}{''{.IPAddress}''}{''{end}''}' matrix-synapse" | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| register: awx_synapse_container_ip | |||
| - name: Collect access token for @admin-janitor user | |||
| shell: | | |||
| curl -X POST -d '{"type":"m.login.password", "user":"admin-janitor", "password":"{{ awx_janitor_user_password }}"}' "{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_matrix/client/r0/login" | jq '.access_token' | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| register: awx_janitors_token | |||
| no_log: true | |||
| - name: Copy build_room_list.py script to target machine | |||
| copy: | |||
| src: ./roles/matrix-awx/scripts/matrix_build_room_list.py | |||
| dest: /usr/local/bin/matrix_build_room_list.py | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '0755' | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Run build_room_list.py script | |||
| shell: | | |||
| runuser -u matrix -- python3 /usr/local/bin/matrix_build_room_list.py {{ awx_janitors_token.stdout[1:-1] }} {{ awx_synapse_container_ip.stdout }} {{ matrix_synapse_container_client_api_port.stdout }} | |||
| register: awx_rooms_total | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Fetch complete room list from target machine | |||
| fetch: | |||
| src: /tmp/room_list_complete.json | |||
| dest: "/tmp/{{ subscription_id }}_room_list_complete.json" | |||
| flat: true | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Remove complete room list from target machine | |||
| file: | |||
| path: /tmp/room_list_complete.json | |||
| state: absent | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Generate list of rooms with no local users | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| jq 'try .rooms[] | select(.joined_local_members == 0) | .room_id' < /tmp/{{ subscription_id }}_room_list_complete.json > /tmp/{{ subscription_id }}_room_list_no_local_users.txt | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Count number of rooms with no local users | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| wc -l /tmp/{{ subscription_id }}_room_list_no_local_users.txt | awk '{ print $1 }' | |||
| register: awx_rooms_no_local_total | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Setting host fact awx_room_list_no_local_users | |||
| set_fact: | |||
| awx_room_list_no_local_users: "{{ lookup('file', '/tmp/{{ subscription_id }}_room_list_no_local_users.txt') }}" | |||
| no_log: true | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Purge all rooms with no local users | |||
| include_tasks: purge_database_no_local.yml | |||
| loop: "{{ awx_room_list_no_local_users.splitlines() | flatten(levels=1) }}" | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Collect epoche time from date | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| date -d '{{ awx_purge_date }}' +"%s" | |||
| when: (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| register: awx_purge_epoche_time | |||
| - name: Generate list of rooms with more then N users | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| jq 'try .rooms[] | select(.joined_members > {{ awx_purge_metric_value }}) | .room_id' < /tmp/{{ subscription_id }}_room_list_complete.json > /tmp/{{ subscription_id }}_room_list_joined_members.txt | |||
| when: awx_purge_mode.find("Number of users [slower]") != -1 | |||
| - name: Count number of rooms with more then N users | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| wc -l /tmp/{{ subscription_id }}_room_list_joined_members.txt | awk '{ print $1 }' | |||
| register: awx_rooms_join_members_total | |||
| when: awx_purge_mode.find("Number of users [slower]") != -1 | |||
| - name: Setting host fact awx_room_list_joined_members | |||
| delegate_to: 127.0.0.1 | |||
| set_fact: | |||
| awx_room_list_joined_members: "{{ lookup('file', '/tmp/{{ subscription_id }}_room_list_joined_members.txt') }}" | |||
| when: awx_purge_mode.find("Number of users [slower]") != -1 | |||
| no_log: true | |||
| - name: Purge all rooms with more then N users | |||
| include_tasks: purge_database_users.yml | |||
| loop: "{{ awx_room_list_joined_members.splitlines() | flatten(levels=1) }}" | |||
| when: awx_purge_mode.find("Number of users [slower]") != -1 | |||
| - name: Generate list of rooms with more then N events | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| jq 'try .rooms[] | select(.state_events > {{ awx_purge_metric_value }}) | .room_id' < /tmp/{{ subscription_id }}_room_list_complete.json > /tmp/{{ subscription_id }}_room_list_state_events.txt | |||
| when: awx_purge_mode.find("Number of events [slower]") != -1 | |||
| - name: Count number of rooms with more then N events | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| wc -l /tmp/{{ subscription_id }}_room_list_state_events.txt | awk '{ print $1 }' | |||
| register: awx_rooms_state_events_total | |||
| when: awx_purge_mode.find("Number of events [slower]") != -1 | |||
| - name: Setting host fact awx_room_list_state_events | |||
| delegate_to: 127.0.0.1 | |||
| set_fact: | |||
| awx_room_list_state_events: "{{ lookup('file', '/tmp/{{ subscription_id }}_room_list_state_events.txt') }}" | |||
| when: awx_purge_mode.find("Number of events [slower]") != -1 | |||
| no_log: true | |||
| - name: Purge all rooms with more then N events | |||
| include_tasks: purge_database_events.yml | |||
| loop: "{{ awx_room_list_state_events.splitlines() | flatten(levels=1) }}" | |||
| when: awx_purge_mode.find("Number of events [slower]") != -1 | |||
| - name: Adjust 'Deploy/Update a Server' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| description: "Creates a new matrix service with Spantaleev's playbooks" | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "rust-synapse-compress-state" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) or (awx_purge_mode.find("Skip purging rooms [faster]") != -1) | |||
| - name: Execute rust-synapse-compress-state job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_launch: | |||
| job_template: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| wait: true | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) or (awx_purge_mode.find("Skip purging rooms [faster]") != -1) | |||
| - name: Revert 'Deploy/Update a Server' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| description: "Creates a new matrix service with Spantaleev's playbooks" | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "setup-all,start" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) or (awx_purge_mode.find("Skip purging rooms [faster]") != -1) | |||
| - name: Ensure matrix-synapse is stopped | |||
| service: | |||
| name: matrix-synapse | |||
| state: stopped | |||
| daemon_reload: true | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Re-index Synapse database | |||
| shell: docker exec -i matrix-postgres psql "host=127.0.0.1 port=5432 dbname=synapse user=synapse password={{ matrix_synapse_connection_password }}" -c 'REINDEX (VERBOSE) DATABASE synapse' | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Ensure matrix-synapse is started | |||
| service: | |||
| name: matrix-synapse | |||
| state: started | |||
| daemon_reload: true | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Adjust 'Deploy/Update a Server' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| description: "Creates a new matrix service with Spantaleev's playbooks" | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "run-postgres-vacuum,start" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Execute run-postgres-vacuum job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_launch: | |||
| job_template: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| wait: true | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Revert 'Deploy/Update a Server' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 0 - Deploy/Update a Server" | |||
| description: "Creates a new matrix service with Spantaleev's playbooks" | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "setup-all,start" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Cleanup room_list files | |||
| delegate_to: 127.0.0.1 | |||
| shell: | | |||
| rm /tmp/{{ subscription_id }}_room_list* | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| ignore_errors: true | |||
| - name: Collect after shrink size of Synapse database | |||
| shell: du -sh /matrix/postgres/data | |||
| register: awx_db_size_after_stat | |||
| when: (awx_purge_mode.find("Perform final shrink") != -1) | |||
| no_log: true | |||
| - name: Print total number of rooms processed | |||
| debug: | |||
| msg: '{{ awx_rooms_total.stdout }}' | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Print the number of rooms purged with no local users | |||
| debug: | |||
| msg: '{{ awx_rooms_no_local_total.stdout }}' | |||
| when: (awx_purge_mode.find("No local users [recommended]") != -1) or (awx_purge_mode.find("Number of users [slower]") != -1) or (awx_purge_mode.find("Number of events [slower]") != -1) | |||
| - name: Print the number of rooms purged with more then N users | |||
| debug: | |||
| msg: '{{ awx_rooms_join_members_total.stdout }}' | |||
| when: awx_purge_mode.find("Number of users") != -1 | |||
| - name: Print the number of rooms purged with more then N events | |||
| debug: | |||
| msg: '{{ awx_rooms_state_events_total.stdout }}' | |||
| when: awx_purge_mode.find("Number of events") != -1 | |||
| - name: Print before purge size of Synapse database | |||
| debug: | |||
| msg: "{{ awx_db_size_before_stat.stdout.split('\n') }}" | |||
| when: ( awx_db_size_before_stat is defined ) and ( awx_purge_mode.find("Perform final shrink" ) != -1 ) | |||
| - name: Print after purge size of Synapse database | |||
| debug: | |||
| msg: "{{ awx_db_size_after_stat.stdout.split('\n') }}" | |||
| when: (awx_db_size_after_stat is defined) and (awx_purge_mode.find("Perform final shrink") != -1) | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| awx_end_playbook: true | |||
| - name: End playbook early if this task is called. | |||
| meta: end_play | |||
| when: awx_end_playbook is defined and awx_end_playbook|bool | |||
+ 0
- 14
roles/matrix-awx/tasks/purge_database_no_local.yml
Просмотреть файл
| @@ -1,14 +0,0 @@ | |||
| --- | |||
| - name: Purge all rooms with no local users | |||
| shell: | | |||
| curl --header "Authorization: Bearer {{ awx_janitors_token.stdout[1:-1] }}" -X POST -H "Content-Type: application/json" -d '{ "room_id": {{ item }} }' '{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_synapse/admin/v1/purge_room' | |||
| register: awx_purge_command | |||
| - name: Print output of purge command | |||
| debug: | |||
| msg: "{{ awx_purge_command.stdout }}" | |||
| - name: Pause for 5 seconds to let Synapse breathe | |||
| pause: | |||
| seconds: 5 | |||
+ 0
- 14
roles/matrix-awx/tasks/purge_database_users.yml
Просмотреть файл
| @@ -1,14 +0,0 @@ | |||
| --- | |||
| - name: Purge all rooms with more then N users | |||
| shell: | | |||
| curl --header "Authorization: Bearer {{ awx_janitors_token.stdout[1:-1] }}" -X POST -H "Content-Type: application/json" -d '{ "delete_local_events": false, "purge_up_to_ts": {{ awx_purge_epoche_time.stdout }}000 }' "{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_synapse/admin/v1/purge_history/{{ item[1:-1] }}" | |||
| register: awx_purge_command | |||
| - name: Print output of purge command | |||
| debug: | |||
| msg: "{{ awx_purge_command.stdout }}" | |||
| - name: Pause for 5 seconds to let Synapse breathe | |||
| pause: | |||
| seconds: 5 | |||
+ 0
- 19
roles/matrix-awx/tasks/purge_media_local.yml
Просмотреть файл
| @@ -1,19 +0,0 @@ | |||
| --- | |||
| - name: Collect epoche time from date | |||
| shell: | | |||
| date -d '{{ item }}' +"%s" | |||
| register: awx_epoche_time | |||
| - name: Purge local media to specific date | |||
| shell: | | |||
| curl -X POST --header "Authorization: Bearer {{ awx_janitors_token.stdout[1:-1] }}" '{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_synapse/admin/v1/media/matrix.{{ matrix_domain }}/delete?before_ts={{ awx_epoche_time.stdout }}000' | |||
| register: awx_purge_command | |||
| - name: Print output of purge command | |||
| debug: | |||
| msg: "{{ awx_purge_command.stdout }}" | |||
| - name: Pause for 5 seconds to let Synapse breathe | |||
| pause: | |||
| seconds: 5 | |||
+ 0
- 111
roles/matrix-awx/tasks/purge_media_main.yml
Просмотреть файл
| @@ -1,111 +0,0 @@ | |||
| --- | |||
| - name: Ensure dateutils is installed in AWX | |||
| delegate_to: 127.0.0.1 | |||
| yum: | |||
| name: dateutils | |||
| state: latest | |||
| - name: Include vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| no_log: true | |||
| - name: Ensure curl and jq intalled on target machine | |||
| apt: | |||
| pkg: | |||
| - curl | |||
| - jq | |||
| state: present | |||
| - name: Collect the internal IP of the matrix-synapse container | |||
| shell: "/usr/bin/docker inspect --format '{''{range.NetworkSettings.Networks}''}{''{.IPAddress}''}{''{end}''}' matrix-synapse" | |||
| register: awx_synapse_container_ip | |||
| - name: Collect access token for @admin-janitor user | |||
| shell: | | |||
| curl -XPOST -d '{"type":"m.login.password", "user":"admin-janitor", "password":"{{ awx_janitor_user_password }}"}' "{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_matrix/client/r0/login" | jq '.access_token' | |||
| register: awx_janitors_token | |||
| no_log: true | |||
| - name: Generate list of dates to purge to | |||
| delegate_to: 127.0.0.1 | |||
| shell: "dateseq {{ awx_purge_from_date }} {{ awx_purge_to_date }}" | |||
| register: awx_purge_dates | |||
| - name: Calculate initial size of local media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/local* | |||
| register: awx_local_media_size_before | |||
| when: awx_purge_media_type == "Local Media" | |||
| async: 600 | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Calculate initial size of remote media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/remote* | |||
| register: awx_remote_media_size_before | |||
| when: awx_purge_media_type == "Remote Media" | |||
| async: 600 | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Purge local media with loop | |||
| include_tasks: purge_media_local.yml | |||
| loop: "{{ awx_purge_dates.stdout_lines | flatten(levels=1) }}" | |||
| when: awx_purge_media_type == "Local Media" | |||
| - name: Purge remote media with loop | |||
| include_tasks: purge_media_remote.yml | |||
| loop: "{{ awx_purge_dates.stdout_lines | flatten(levels=1) }}" | |||
| when: awx_purge_media_type == "Remote Media" | |||
| - name: Calculate final size of local media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/local* | |||
| register: awx_local_media_size_after | |||
| when: awx_purge_media_type == "Local Media" | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Calculate final size of remote media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/remote* | |||
| register: awx_remote_media_size_after | |||
| when: awx_purge_media_type == "Remote Media" | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Print size of local media repository before purge | |||
| debug: | |||
| msg: "{{ awx_local_media_size_before.stdout.split('\n') }}" | |||
| when: awx_purge_media_type == "Local Media" | |||
| - name: Print size of local media repository after purge | |||
| debug: | |||
| msg: "{{ awx_local_media_size_after.stdout.split('\n') }}" | |||
| when: awx_purge_media_type == "Local Media" | |||
| - name: Print size of remote media repository before purge | |||
| debug: | |||
| msg: "{{ awx_remote_media_size_before.stdout.split('\n') }}" | |||
| when: awx_purge_media_type == "Remote Media" | |||
| - name: Print size of remote media repository after purge | |||
| debug: | |||
| msg: "{{ awx_remote_media_size_after.stdout.split('\n') }}" | |||
| when: awx_purge_media_type == "Remote Media" | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| awx_end_playbook: true | |||
| - name: End playbook early if this task is called. | |||
| meta: end_play | |||
| when: awx_end_playbook is defined and awx_end_playbook|bool | |||
+ 0
- 19
roles/matrix-awx/tasks/purge_media_remote.yml
Просмотреть файл
| @@ -1,19 +0,0 @@ | |||
| --- | |||
| - name: Collect epoche time from date | |||
| shell: | | |||
| date -d '{{ item }}' +"%s" | |||
| register: awx_epoche_time | |||
| - name: Purge remote media to specific date | |||
| shell: | | |||
| curl -X POST --header "Authorization: Bearer {{ awx_janitors_token.stdout[1:-1] }}" '{{ awx_synapse_container_ip.stdout }}:{{ matrix_synapse_container_client_api_port }}/_synapse/admin/v1/purge_media_cache?before_ts={{ awx_epoche_time.stdout }}000' | |||
| register: awx_purge_command | |||
| - name: Print output of purge command | |||
| debug: | |||
| msg: "{{ awx_purge_command.stdout }}" | |||
| - name: Pause for 5 seconds to let Synapse breathe | |||
| pause: | |||
| seconds: 5 | |||
+ 0
- 25
roles/matrix-awx/tasks/rotate_ssh.yml
Просмотреть файл
| @@ -1,25 +0,0 @@ | |||
| --- | |||
| - name: Set the new authorized key taken from file | |||
| authorized_key: | |||
| user: root | |||
| state: present | |||
| exclusive: true | |||
| key: "{{ lookup('file', '/var/lib/awx/projects/hosting/client_public.key') }}" | |||
| - name: Delete the AWX session token for executing modules | |||
| awx.awx.tower_token: | |||
| description: 'AWX Session Token' | |||
| scope: "write" | |||
| state: absent | |||
| existing_token_id: "{{ awx_session_token.ansible_facts.tower_token.id }}" | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| - name: Set boolean value to exit playbook | |||
| set_fact: | |||
| end_playbook: true | |||
| - name: End playbook if this task list is called. | |||
| meta: end_play | |||
| when: end_playbook is defined and end_playbook|bool | |||
+ 0
- 108
roles/matrix-awx/tasks/self_check.yml
Просмотреть файл
| @@ -1,108 +0,0 @@ | |||
| --- | |||
| - name: Install prerequisite apt packages on target | |||
| apt: | |||
| name: | |||
| - sysstat | |||
| - curl | |||
| state: present | |||
| - name: Install prerequisite yum packages on AWX | |||
| delegate_to: 127.0.0.1 | |||
| yum: | |||
| name: | |||
| - bind-utils | |||
| state: present | |||
| - name: Install prerequisite pip packages on AWX | |||
| delegate_to: 127.0.0.1 | |||
| pip: | |||
| name: | |||
| - dnspython | |||
| state: present | |||
| - name: Calculate MAU value | |||
| shell: | | |||
| curl -s localhost:9000 | grep "^synapse_admin_mau_current " | |||
| register: awx_mau_stat | |||
| no_log: true | |||
| - name: Calculate CPU usage statistics | |||
| shell: iostat -c | |||
| register: awx_cpu_usage_stat | |||
| no_log: true | |||
| - name: Calculate RAM usage statistics | |||
| shell: free -mh | |||
| register: awx_ram_usage_stat | |||
| no_log: true | |||
| - name: Calculate free disk space | |||
| shell: df -h | |||
| register: awx_disk_space_stat | |||
| no_log: true | |||
| - name: Calculate size of Synapse database | |||
| shell: du -sh /matrix/postgres/data | |||
| register: awx_db_size_stat | |||
| no_log: true | |||
| - name: Calculate size of local media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/local* | |||
| register: awx_local_media_size_stat | |||
| async: 600 | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Calculate size of remote media repository | |||
| shell: du -sh /matrix/synapse/storage/media-store/remote* | |||
| register: awx_remote_media_size_stat | |||
| async: 600 | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Calculate docker container statistics | |||
| shell: docker stats --all --no-stream | |||
| register: awx_docker_stats | |||
| ignore_errors: true | |||
| no_log: true | |||
| - name: Print size of remote media repository | |||
| debug: | |||
| msg: "{{ awx_remote_media_size_stat.stdout.split('\n') }}" | |||
| when: awx_remote_media_size_stat is defined | |||
| - name: Print size of local media repository | |||
| debug: | |||
| msg: "{{ awx_local_media_size_stat.stdout.split('\n') }}" | |||
| when: awx_local_media_size_stat is defined | |||
| - name: Print size of Synapse database | |||
| debug: | |||
| msg: "{{ awx_db_size_stat.stdout.split('\n') }}" | |||
| when: awx_db_size_stat is defined | |||
| - name: Print free disk space | |||
| debug: | |||
| msg: "{{ awx_disk_space_stat.stdout.split('\n') }}" | |||
| when: awx_disk_space_stat is defined | |||
| - name: Print RAM usage statistics | |||
| debug: | |||
| msg: "{{ awx_ram_usage_stat.stdout.split('\n') }}" | |||
| when: awx_ram_usage_stat is defined | |||
| - name: Print CPU usage statistics | |||
| debug: | |||
| msg: "{{ awx_cpu_usage_stat.stdout.split('\n') }}" | |||
| when: awx_cpu_usage_stat is defined | |||
| - name: Print MAU value | |||
| debug: | |||
| msg: "{{ awx_mau_stat.stdout.split('\n') }}" | |||
| when: awx_mau_stat is defined | |||
| - name: Print docker container statistics | |||
| debug: | |||
| msg: "{{ awx_docker_stats.stdout.split('\n') }}" | |||
| when: awx_docker_stats is defined | |||
+ 0
- 243
roles/matrix-awx/tasks/set_variables_corporal.yml
Просмотреть файл
| @@ -1,243 +0,0 @@ | |||
| --- | |||
| - name: Record Corporal Enabled/Disabled variable | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Corporal Settings Start' | |||
| with_dict: | |||
| 'matrix_corporal_enabled': '{{ matrix_corporal_enabled }}' | |||
| - name: Enable Shared Secret Auth if Corporal enabled | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Shared Secret Auth Settings Start' | |||
| with_dict: | |||
| 'matrix_synapse_ext_password_provider_shared_secret_auth_enabled': 'true' | |||
| when: matrix_corporal_enabled|bool | |||
| - name: Disable Shared Secret Auth if Corporal disabled | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Shared Secret Auth Settings Start' | |||
| with_dict: | |||
| 'matrix_synapse_ext_password_provider_shared_secret_auth_enabled': 'false' | |||
| when: not matrix_corporal_enabled|bool | |||
| - name: Enable Rest Auth Endpoint if Corporal enabled | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Extension Start' | |||
| with_dict: | |||
| 'matrix_synapse_ext_password_provider_rest_auth_enabled': 'true' | |||
| when: matrix_corporal_enabled|bool | |||
| - name: Disable Rest Auth Endpoint if Corporal disabled | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Extension Start' | |||
| with_dict: | |||
| 'matrix_synapse_ext_password_provider_rest_auth_enabled': 'false' | |||
| when: not matrix_corporal_enabled|bool | |||
| - name: Disable Corporal API if Simple Static File mode selected | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Corporal Settings Start' | |||
| with_dict: | |||
| 'matrix_corporal_http_api_enabled': 'false' | |||
| when: (awx_corporal_policy_provider_mode == "Simple Static File") or (not matrix_corporal_enabled|bool) | |||
| - name: Enable Corporal API if Push/Pull mode delected | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Corporal Settings Start' | |||
| with_dict: | |||
| 'matrix_corporal_http_api_enabled': 'true' | |||
| when: (awx_corporal_policy_provider_mode != "Simple Static File") and (matrix_corporal_enabled|bool) | |||
| - name: Record Corporal API Access Token if it's defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Corporal Settings Start' | |||
| with_dict: | |||
| 'matrix_corporal_http_api_auth_token': '{{ matrix_corporal_http_api_auth_token }}' | |||
| when: ( matrix_corporal_http_api_auth_token|length > 0 ) and ( awx_corporal_policy_provider_mode != "Simple Static File" ) | |||
| - name: Record 'Simple Static File' configuration variables in matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| blockinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertbefore: "# Corporal Policy Provider Settings End" | |||
| marker_begin: "Corporal" | |||
| marker_end: "Corporal" | |||
| block: | | |||
| matrix_corporal_policy_provider_config: | | |||
| { | |||
| "Type": "static_file", | |||
| "Path": "/etc/matrix-corporal/corporal-policy.json" | |||
| } | |||
| when: awx_corporal_policy_provider_mode == "Simple Static File" | |||
| - name: Touch the /matrix/corporal/ directory | |||
| file: | |||
| path: "/matrix/corporal/" | |||
| state: directory | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '750' | |||
| - name: Touch the /matrix/corporal/config/ directory | |||
| file: | |||
| path: "/matrix/corporal/config/" | |||
| state: directory | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '750' | |||
| - name: Touch the /matrix/corporal/cache/ directory | |||
| file: | |||
| path: "/matrix/corporal/cache/" | |||
| state: directory | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '750' | |||
| - name: Touch the corporal-policy.json file to ensure it exists | |||
| file: | |||
| path: "/matrix/corporal/config/corporal-policy.json" | |||
| state: touch | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '660' | |||
| - name: Touch the last-policy.json file to ensure it exists | |||
| file: | |||
| path: "/matrix/corporal/config/last-policy.json" | |||
| state: touch | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '660' | |||
| - name: Record 'Simple Static File' configuration content in corporal-policy.json | |||
| copy: | |||
| content: "{{ awx_corporal_simple_static_config | string }}" | |||
| dest: "/matrix/corporal/config/corporal-policy.json" | |||
| owner: matrix | |||
| group: matrix | |||
| mode: '660' | |||
| when: (awx_corporal_policy_provider_mode == "Simple Static File") and (awx_corporal_simple_static_config|length > 0) | |||
| - name: Record 'HTTP Pull Mode' configuration variables in matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| blockinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: "# Corporal Policy Provider Settings Start" | |||
| block: | | |||
| matrix_corporal_policy_provider_config: | | |||
| { | |||
| "Type": "http", | |||
| "Uri": "{{ awx_corporal_pull_mode_uri }}", | |||
| "AuthorizationBearerToken": "{{ awx_corporal_pull_mode_token }}", | |||
| "CachePath": "/var/cache/matrix-corporal/last-policy.json", | |||
| "ReloadIntervalSeconds": 1800, | |||
| "TimeoutMilliseconds": 30000 | |||
| } | |||
| when: (awx_corporal_policy_provider_mode == "HTTP Pull Mode (API Enabled)") and (matrix_corporal_pull_mode_uri|length > 0) and (awx_corporal_pull_mode_token|length > 0) | |||
| - name: Record 'HTTP Push Mode' configuration variables in matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| blockinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: "# Corporal Policy Provider Settings Start" | |||
| block: | | |||
| matrix_corporal_policy_provider_config: | | |||
| { | |||
| "Type": "last_seen_store_policy", | |||
| "CachePath": "/var/cache/matrix-corporal/last-policy.json" | |||
| } | |||
| when: (awx_corporal_policy_provider_mode == "HTTP Push Mode (API Enabled)") | |||
| - name: Lower RateLimit if set to 'Normal' | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: ' address:\n per_second: 50\n burst_count: 300\n account:\n per_second: 0.17\n burst_count: 300' | |||
| replace: ' address:\n per_second: 0.17\n burst_count: 3\n account:\n per_second: 0.17\n burst_count: 3' | |||
| when: awx_corporal_raise_ratelimits == "Normal" | |||
| - name: Raise RateLimit if set to 'Raised' | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: ' address:\n per_second: 0.17\n burst_count: 3\n account:\n per_second: 0.17\n burst_count: 3' | |||
| replace: ' address:\n per_second: 50\n burst_count: 300\n account:\n per_second: 0.17\n burst_count: 300' | |||
| when: awx_corporal_raise_ratelimits == "Raised" | |||
| - name: Save new 'Configure Corporal' survey.json to the AWX tower | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_corporal.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_corporal.json' | |||
| - name: Copy new 'Configure Corporal' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_corporal.json' | |||
| dest: '/matrix/awx/configure_corporal.json' | |||
| mode: '0660' | |||
| - debug: | |||
| msg: "matrix_corporal_matrix_homeserver_api_endpoint: {{ matrix_corporal_matrix_homeserver_api_endpoint }}" | |||
| - debug: | |||
| msg: "matrix_corporal_matrix_auth_shared_secret: {{ matrix_corporal_matrix_auth_shared_secret }}" | |||
| - debug: | |||
| msg: "matrix_corporal_http_gateway_internal_rest_auth_enabled: {{ matrix_corporal_http_gateway_internal_rest_auth_enabled }}" | |||
| - debug: | |||
| msg: "matrix_corporal_matrix_registration_shared_secret: {{ matrix_corporal_matrix_registration_shared_secret }}" | |||
| - name: Recreate 'Configure Corporal (Advanced)' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Corporal (Advanced)" | |||
| description: "Configure Matrix Corporal, a tool that manages your Matrix server according to a configuration policy." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-corporal" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_corporal.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 105
roles/matrix-awx/tasks/set_variables_dimension.yml
Просмотреть файл
| @@ -1,105 +0,0 @@ | |||
| --- | |||
| - name: Include vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '{{ awx_cached_matrix_vars }}' | |||
| no_log: true | |||
| - name: Install jq and curl on remote machine | |||
| apt: | |||
| name: | |||
| - jq | |||
| - curl | |||
| state: present | |||
| - name: Collect access token of @admin-dimension user | |||
| shell: | | |||
| curl -X POST --header 'Content-Type: application/json' -d '{"identifier": {"type": "m.id.user","user": "admin-dimension"}, "password": "{{ awx_dimension_user_password }}", "type": "m.login.password"}' 'https://matrix.{{ matrix_domain }}/_matrix/client/r0/login' | jq '.access_token' | |||
| register: awx_dimension_user_access_token | |||
| - name: Record Synapse variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Dimension Settings Start' | |||
| with_dict: | |||
| 'matrix_dimension_enabled': '{{ matrix_dimension_enabled }}' | |||
| 'matrix_dimension_access_token': '"{{ awx_dimension_user_access_token.stdout[1:-1] }}"' | |||
| - name: Set final users list if users are defined | |||
| set_fact: | |||
| awx_dimension_users_final: "{{ awx_dimension_users }}" | |||
| when: awx_dimension_users | length > 0 | |||
| - name: Set final users list if no users are defined | |||
| set_fact: | |||
| awx_dimension_users_final: '@dimension:{{ matrix_domain }}' | |||
| when: awx_dimension_users | length == 0 | |||
| - name: Remove Dimension Users | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: '^ - .*\n' | |||
| after: 'matrix_dimension_admins:' | |||
| before: '# Dimension Settings End' | |||
| - name: Set Dimension Users Header | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertbefore: '# Dimension Settings End' | |||
| line: "matrix_dimension_admins:" | |||
| - name: Set Dimension Users | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: '^matrix_dimension_admins:' | |||
| line: ' - "{{ item }}"' | |||
| with_items: "{{ awx_dimension_users_final.splitlines() }}" | |||
| - name: Record Dimension Custom variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertbefore: '# Dimension Settings End' | |||
| with_dict: | |||
| 'awx_dimension_users': '{{ awx_dimension_users.splitlines() | to_json }}' | |||
| - name: Save new 'Configure Dimension' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_dimension.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}//configure_dimension.json' | |||
| - name: Copy new 'Configure Dimension' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_dimension.json' | |||
| dest: '/matrix/awx/configure_dimension.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Dimension' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Dimension" | |||
| description: "Configure Dimension, the self-hosted integrations server." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-all,setup-dimension" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_dimension.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 180
roles/matrix-awx/tasks/set_variables_element.yml
Просмотреть файл
| @@ -1,180 +0,0 @@ | |||
| --- | |||
| - name: Record Element-Web variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_enabled': '{{ matrix_client_element_enabled }}' | |||
| 'matrix_client_element_jitsi_preferredDomain': 'jitsi.{{ matrix_domain }}' | |||
| 'matrix_client_element_default_theme': '{{ matrix_client_element_default_theme }}' | |||
| 'matrix_client_element_registration_enabled': '{{ matrix_client_element_registration_enabled }}' | |||
| 'matrix_client_element_brand': '{{ matrix_client_element_brand | trim }}' | |||
| 'matrix_client_element_branding_welcomeBackgroundUrl': '{{ matrix_client_element_branding_welcomeBackgroundUrl | trim }}' | |||
| 'matrix_client_element_welcome_logo': '{{ matrix_client_element_welcome_logo | trim }}' | |||
| 'matrix_client_element_welcome_logo_link': '{{ matrix_client_element_welcome_logo_link | trim }}' | |||
| - name: Record Element-Web custom variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertbefore: '# Element Settings End' | |||
| with_dict: | |||
| 'awx_matrix_client_element_welcome_headline': '{{ awx_matrix_client_element_welcome_headline | trim }}' | |||
| 'awx_matrix_client_element_welcome_text': '{{ awx_matrix_client_element_welcome_text | trim }}' | |||
| - name: Set Element-Web custom branding locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_brand': "{{ matrix_client_element_brand }}" | |||
| when: matrix_client_element_brand | trim | length > 0 | |||
| - name: Remove Element-Web custom branding locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_brand: " | |||
| state: absent | |||
| when: matrix_client_element_brand | trim | length == 0 | |||
| - name: Set fact for 'https' string | |||
| set_fact: | |||
| awx_https_string: "https" | |||
| - name: Set Element-Web custom logo locally on AWX if defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_welcome_logo': '{{ matrix_client_element_welcome_logo }}' | |||
| when: ( awx_https_string in matrix_client_element_welcome_logo ) and ( matrix_client_element_welcome_logo | trim | length > 0 ) | |||
| - name: Remove Element-Web custom logo locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_welcome_logo: " | |||
| state: absent | |||
| when: matrix_client_element_welcome_logo | trim | length == 0 | |||
| - name: Set Element-Web custom logo link locally on AWX if defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_welcome_logo_link': '{{ matrix_client_element_welcome_logo_link }}' | |||
| when: ( awx_https_string in matrix_client_element_welcome_logo_link ) and ( matrix_client_element_welcome_logo_link | trim | length > 0 ) | |||
| - name: Remove Element-Web custom logo link locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_welcome_logo_link: " | |||
| state: absent | |||
| when: matrix_client_element_welcome_logo_link | trim | length == 0 | |||
| - name: Set Element-Web custom headline locally on AWX if defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_welcome_headline': '{{ awx_matrix_client_element_welcome_headline }}' | |||
| when: awx_matrix_client_element_welcome_headline | trim | length > 0 | |||
| - name: Remove Element-Web custom headline locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_welcome_headline: " | |||
| state: absent | |||
| when: awx_matrix_client_element_welcome_headline | trim | length == 0 | |||
| - name: Set Element-Web custom text locally on AWX if defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_welcome_text': '{{ awx_matrix_client_element_welcome_text }}' | |||
| when: awx_matrix_client_element_welcome_text | trim | length > 0 | |||
| - name: Remove Element-Web custom text locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_welcome_text: " | |||
| state: absent | |||
| when: awx_matrix_client_element_welcome_text | trim | length == 0 | |||
| - name: Set Element-Web background locally on AWX if defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: '{{ item.value }}'" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_client_element_branding_welcomeBackgroundUrl': '{{ matrix_client_element_branding_welcomeBackgroundUrl }}' | |||
| when: matrix_client_element_branding_welcomeBackgroundUrl | trim | length > 0 | |||
| - name: Remove Element-Web background locally on AWX if not defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_client_element_branding_welcomeBackgroundUrl: " | |||
| state: absent | |||
| when: matrix_client_element_branding_welcomeBackgroundUrl | trim | length == 0 | |||
| - name: Save new 'Configure Element' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_element.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element.json' | |||
| - name: Copy new 'Configure Element' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element.json' | |||
| dest: '/matrix/awx/configure_element.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Element' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Element" | |||
| description: "Configure Element client via survey." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-client-element" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 43
roles/matrix-awx/tasks/set_variables_element_subdomain.yml
Просмотреть файл
| @@ -1,43 +0,0 @@ | |||
| --- | |||
| - name: Record Element-Web variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Element Settings Start' | |||
| with_dict: | |||
| 'matrix_server_fqn_element': "{{ awx_element_subdomain | trim }}.{{ matrix_domain }}" | |||
| - name: Save new 'Configure Element Subdomain' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_element_subdomain.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element_subdomain.json' | |||
| - name: Copy new 'Configure Element Subdomain' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element_subdomain.json' | |||
| dest: '/matrix/awx/configure_element_subdomain.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Element Subdomain' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Element Subdomain" | |||
| description: "Configure Element clients subdomain location. (Eg: 'element' for element.example.org)" | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-all,setup-client-element-subdomain" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_element_subdomain.json') }}" | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 45
roles/matrix-awx/tasks/set_variables_jitsi.yml
Просмотреть файл
| @@ -1,45 +0,0 @@ | |||
| --- | |||
| - name: Record Jitsi variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Jitsi Settings Start' | |||
| with_dict: | |||
| 'matrix_jitsi_enabled': '{{ matrix_jitsi_enabled }}' | |||
| 'matrix_jitsi_web_config_defaultLanguage': '{{ matrix_jitsi_web_config_defaultLanguage | trim }}' | |||
| - name: Save new 'Configure Jitsi' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_jitsi.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_jitsi.json' | |||
| - name: Copy new 'Configure Jitsi' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_jitsi.json' | |||
| dest: '/matrix/awx/configure_jitsi.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Jitsi' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Jitsi" | |||
| description: "Configure Jitsi conferencing settings." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-jitsi" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_jitsi.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 102
roles/matrix-awx/tasks/set_variables_ma1sd.yml
Просмотреть файл
| @@ -1,102 +0,0 @@ | |||
| --- | |||
| - name: Record ma1sd variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# ma1sd Settings Start' | |||
| with_dict: | |||
| 'matrix_ma1sd_enabled': '{{ matrix_ma1sd_enabled }}' | |||
| - name: Disable REST auth (matrix-corporal/ma1sd) if using internal auth | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Extension Start' | |||
| with_dict: | |||
| 'matrix_synapse_awx_password_provider_rest_auth_enabled': 'false' | |||
| when: awx_matrix_ma1sd_auth_store == 'Synapse Internal' | |||
| - name: Enable REST auth if using external LDAP/AD with ma1sd | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Extension Start' | |||
| with_dict: | |||
| 'matrix_synapse_awx_password_provider_rest_auth_enabled': 'true' | |||
| 'matrix_synapse_awx_password_provider_rest_auth_endpoint': '"http://matrix-ma1sd:{{ matrix_ma1sd_container_port }}"' | |||
| when: awx_matrix_ma1sd_auth_store == 'LDAP/AD' | |||
| - name: Remove entire ma1sd configuration extension | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: '^.*\n' | |||
| after: '# ma1sd Extension Start' | |||
| before: '# ma1sd Extension End' | |||
| - name: Replace conjoined ma1sd configuration extension limiters | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: '^# ma1sd Extension Start# ma1sd Extension End' | |||
| replace: '# ma1sd Extension Start\n# ma1sd Extension End' | |||
| - name: Insert/Update ma1sd configuration extension variables | |||
| delegate_to: 127.0.0.1 | |||
| blockinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| marker: "# {mark} ma1sd ANSIBLE MANAGED BLOCK" | |||
| insertafter: '# ma1sd Extension Start' | |||
| block: '{{ awx_matrix_ma1sd_configuration_extension_yaml }}' | |||
| - name: Record ma1sd Custom variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertbefore: '# ma1sd Settings End' | |||
| with_dict: | |||
| 'awx_matrix_ma1sd_auth_store': '{{ awx_matrix_ma1sd_auth_store }}' | |||
| 'awx_matrix_ma1sd_configuration_extension_yaml': '{{ awx_matrix_ma1sd_configuration_extension_yaml.splitlines() | to_json }}' | |||
| no_log: true | |||
| - name: Save new 'Configure ma1sd' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_ma1sd.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_ma1sd.json' | |||
| - name: Copy new 'Configure ma1sd' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_ma1sd.json' | |||
| dest: '/matrix/awx/configure_ma1sd.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure ma1sd (Advanced)' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure ma1sd (Advanced)" | |||
| description: "Configure Jitsi conferencing settings." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-ma1sd" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_ma1sd.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 44
roles/matrix-awx/tasks/set_variables_mailer.yml
Просмотреть файл
| @@ -1,44 +0,0 @@ | |||
| --- | |||
| - name: Record Mailer variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Email Settings Start' | |||
| with_dict: | |||
| 'matrix_mailer_relay_use': '{{ matrix_mailer_relay_use }}' | |||
| - name: Save new 'Configure Email Relay' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_email_relay.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_email_relay.json' | |||
| - name: Copy new 'Configure Email Relay' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_email_relay.json' | |||
| dest: '/matrix/awx/configure_email_relay.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Email Relay' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Email Relay" | |||
| description: "Enable MailGun relay to increase verification email reliability." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-mailer" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_email_relay.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 68
roles/matrix-awx/tasks/set_variables_mjolnir.yml
Просмотреть файл
| @@ -1,68 +0,0 @@ | |||
| --- | |||
| - name: Include vars in matrix_vars.yml | |||
| include_vars: | |||
| file: '{{ awx_cached_matrix_vars }}' | |||
| no_log: true | |||
| - name: Collect the internal IP of the matrix-synapse container | |||
| shell: | | |||
| /usr/bin/docker inspect --format '{''{range.NetworkSettings.Networks}''}{''{.IPAddress}''}{''{end}''}' matrix-synapse | |||
| register: matrix_synapse_ip | |||
| - name: Collect access token of @admin-mjolnir user | |||
| shell: | | |||
| curl -X POST --header 'Content-Type: application/json' -d '{"identifier": {"type": "m.id.user","user": "admin-mjolnir"}, "password": "{{ awx_mjolnir_user_password }}", "type": "m.login.password"}' 'http://{{ matrix_synapse_ip.stdout }}:8008/_matrix/client/r0/login' | jq '.access_token' | |||
| register: awx_mjolnir_user_access_token | |||
| no_log: true | |||
| - name: Record Mjolnir Bot variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Mjolnir Settings Start' | |||
| with_dict: | |||
| 'matrix_bot_mjolnir_enabled': '{{ matrix_bot_mjolnir_enabled }}' | |||
| 'matrix_bot_mjolnir_access_token': '{{ awx_mjolnir_user_access_token.stdout[1:-1] }}' | |||
| 'matrix_bot_mjolnir_management_room': '"{{ matrix_bot_mjolnir_management_room }}"' | |||
| no_log: true | |||
| - name: Remove Synapse rate-limiting for admin-mjolnir user | |||
| shell: | | |||
| /usr/local/bin/matrix-postgres-cli-non-interactive --dbname=synapse --command="INSERT INTO ratelimit_override VALUES ('@admin-mjolnir:{{ matrix_domain }}', 0, 0);" | |||
| ignore_errors: true | |||
| - name: Save new 'Configure Mjolnir' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_mjolnir.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_mjolnir.json' | |||
| - name: Copy new 'Configure Mjolnir' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_mjolnir.json' | |||
| dest: '/matrix/awx/configure_mjolnir.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Mjolnir Bot' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Mjolnir Bot" | |||
| description: "Configure Mjolnir settings, Mjolnir is a moderation bot for Matrix." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-bot-mjolnir" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_mjolnir.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 223
roles/matrix-awx/tasks/set_variables_synapse.yml
Просмотреть файл
| @@ -1,223 +0,0 @@ | |||
| --- | |||
| - name: Limit max upload size to 200MB part 1 | |||
| set_fact: | |||
| matrix_synapse_max_upload_size_mb: "200" | |||
| when: awx_synapse_max_upload_size_mb | int >= 200 | |||
| - name: Limit max upload size to 200MB part 2 | |||
| set_fact: | |||
| matrix_synapse_max_upload_size_mb: "{{ awx_synapse_max_upload_size_mb }}" | |||
| when: awx_synapse_max_upload_size_mb | int < 200 | |||
| - name: Record Synapse variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Settings Start' | |||
| with_dict: | |||
| 'matrix_synapse_allow_public_rooms_over_federation': '{{ matrix_synapse_allow_public_rooms_over_federation }}' | |||
| 'matrix_synapse_enable_registration': '{{ matrix_synapse_enable_registration }}' | |||
| 'matrix_synapse_federation_enabled': '{{ matrix_synapse_federation_enabled }}' | |||
| 'matrix_synapse_enable_group_creation': '{{ matrix_synapse_enable_group_creation }}' | |||
| 'matrix_synapse_presence_enabled': '{{ matrix_synapse_presence_enabled }}' | |||
| 'matrix_synapse_max_upload_size_mb': '{{ matrix_synapse_max_upload_size_mb }}' | |||
| 'matrix_synapse_url_preview_enabled': '{{ matrix_synapse_url_preview_enabled }}' | |||
| 'matrix_synapse_allow_guest_access': '{{ matrix_synapse_allow_guest_access }}' | |||
| - name: Empty Synapse variable 'matrix_synapse_auto_join_rooms' locally on AWX, if raw inputs empty | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^matrix_synapse_auto_join_rooms: .*$" | |||
| replace: "matrix_synapse_auto_join_rooms: []" | |||
| when: awx_synapse_auto_join_rooms | length == 0 | |||
| - name: If the raw inputs is not empty start constructing parsed auto_join_rooms list | |||
| set_fact: | |||
| awx_synapse_auto_join_rooms_array: |- | |||
| {{ awx_synapse_auto_join_rooms.splitlines() | to_json }} | |||
| when: awx_synapse_auto_join_rooms | length > 0 | |||
| - name: Record Synapse variable 'matrix_synapse_auto_join_rooms' locally on AWX, if it's not blank | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Settings Start' | |||
| with_dict: | |||
| "matrix_synapse_auto_join_rooms": "{{ awx_synapse_auto_join_rooms_array }}" | |||
| when: awx_synapse_auto_join_rooms | length > 0 | |||
| - name: Record Synapse Shared Secret if it's defined | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Settings Start' | |||
| with_dict: | |||
| 'matrix_synapse_registration_shared_secret': '{{ awx_matrix_synapse_registration_shared_secret }}' | |||
| when: awx_matrix_synapse_registration_shared_secret | length > 0 | |||
| - name: Record registations_require_3pid extra variable if true | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "{{ item }}" | |||
| line: "{{ item }}" | |||
| insertbefore: '# Synapse Extension End' | |||
| with_items: | |||
| - " registrations_require_3pid:" | |||
| - " - email" | |||
| when: awx_registrations_require_3pid | bool | |||
| - name: Remove registrations_require_3pid extra variable if false | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "{{ item }}" | |||
| line: "{{ item }}" | |||
| insertbefore: '# Synapse Extension End' | |||
| state: absent | |||
| with_items: | |||
| - " registrations_require_3pid:" | |||
| - " - email" | |||
| when: not awx_registrations_require_3pid | bool | |||
| - name: Remove URL Languages | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: '^(?!.*\bemail\b) - [a-zA-Z\-]{2,5}\n' | |||
| after: ' url_preview_accept_language:' | |||
| before: '# Synapse Extension End' | |||
| - name: Set URL languages default if raw inputs empty | |||
| set_fact: | |||
| awx_url_preview_accept_language_default: 'en' | |||
| when: awx_url_preview_accept_language | length == 0 | |||
| - name: Set URL languages default if raw inputs not empty | |||
| set_fact: | |||
| awx_url_preview_accept_language_default: "{{ awx_url_preview_accept_language }}" | |||
| when: awx_url_preview_accept_language|length > 0 | |||
| - name: Set URL languages if raw inputs empty | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: '^ url_preview_accept_language:' | |||
| line: " - {{ awx_url_preview_accept_language_default }}" | |||
| when: awx_url_preview_accept_language|length == 0 | |||
| - name: Set URL languages if raw inputs not empty | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: '^ url_preview_accept_language:' | |||
| line: " - {{ item }}" | |||
| with_items: "{{ awx_url_preview_accept_language.splitlines() }}" | |||
| when: awx_url_preview_accept_language | length > 0 | |||
| - name: Remove Federation Whitelisting 1 | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: '^ - [a-z0-9]+\.[a-z0-9.]+\n' | |||
| after: ' federation_domain_whitelist:' | |||
| before: '# Synapse Extension End' | |||
| - name: Remove Federation Whitelisting 2 | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| line: " federation_domain_whitelist:" | |||
| state: absent | |||
| - name: Set Federation Whitelisting 1 | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: '^matrix_synapse_configuration_extension_yaml: \|' | |||
| line: " federation_domain_whitelist:" | |||
| when: awx_federation_whitelist | length > 0 | |||
| - name: Set Federation Whitelisting 2 | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| insertafter: '^ federation_domain_whitelist:' | |||
| line: " - {{ item }}" | |||
| with_items: "{{ awx_federation_whitelist.splitlines() }}" | |||
| when: awx_federation_whitelist | length > 0 | |||
| - name: Set awx_recaptcha_public_key to a 'public-key' if undefined | |||
| set_fact: awx_recaptcha_public_key="public-key" | |||
| when: (awx_recaptcha_public_key is not defined) or (awx_recaptcha_public_key|length == 0) | |||
| - name: Set awx_recaptcha_private_key to a 'private-key' if undefined | |||
| set_fact: awx_recaptcha_private_key="private-key" | |||
| when: (awx_recaptcha_private_key is not defined) or (awx_recaptcha_private_key|length == 0) | |||
| - name: Record Synapse Extension variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertbefore: '# Synapse Extension End' | |||
| with_dict: | |||
| ' enable_registration_captcha': '{{ awx_enable_registration_captcha }}' | |||
| ' recaptcha_public_key': '{{ awx_recaptcha_public_key }}' | |||
| ' recaptcha_private_key': '{{ awx_recaptcha_private_key }}' | |||
| - name: Record Synapse Custom variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertbefore: '# Synapse Settings End' | |||
| with_dict: | |||
| 'awx_federation_whitelist': '{{ awx_federation_whitelist.splitlines() | to_json }}' | |||
| 'awx_url_preview_accept_language_default': '{{ awx_url_preview_accept_language_default.splitlines() | to_json }}' | |||
| 'awx_enable_registration_captcha': '{{ awx_enable_registration_captcha }}' | |||
| 'awx_recaptcha_public_key': '"{{ awx_recaptcha_public_key }}"' | |||
| 'awx_recaptcha_private_key': '"{{ awx_recaptcha_private_key }}"' | |||
| - name: Save new 'Configure Synapse' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_synapse.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}//configure_synapse.json' | |||
| - name: Copy new 'Configure Synapse' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_synapse.json' | |||
| dest: '/matrix/awx/configure_synapse.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Synapse' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Synapse" | |||
| description: "Configure Synapse (homeserver) settings." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-synapse" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_synapse.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 44
roles/matrix-awx/tasks/set_variables_synapse_admin.yml
Просмотреть файл
| @@ -1,44 +0,0 @@ | |||
| --- | |||
| - name: Record Synapse Admin variables locally on AWX | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '{{ awx_cached_matrix_vars }}' | |||
| regexp: "^#? *{{ item.key | regex_escape() }}:" | |||
| line: "{{ item.key }}: {{ item.value }}" | |||
| insertafter: '# Synapse Admin Settings Start' | |||
| with_dict: | |||
| 'matrix_synapse_admin_enabled': '{{ matrix_synapse_admin_enabled }}' | |||
| - name: Save new 'Configure Synapse Admin' survey.json to the AWX tower, template | |||
| delegate_to: 127.0.0.1 | |||
| template: | |||
| src: 'roles/matrix-awx/surveys/configure_synapse_admin.json.j2' | |||
| dest: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_synapse_admin.json' | |||
| - name: Copy new 'Configure Synapse Admin' survey.json to target machine | |||
| copy: | |||
| src: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_synapse_admin.json' | |||
| dest: '/matrix/awx/configure_synapse_admin.json' | |||
| mode: '0660' | |||
| - name: Recreate 'Configure Synapse Admin' job template | |||
| delegate_to: 127.0.0.1 | |||
| awx.awx.tower_job_template: | |||
| name: "{{ matrix_domain }} - 1 - Configure Synapse Admin" | |||
| description: "Configure 'Synapse Admin', a moderation tool to help you manage your server." | |||
| extra_vars: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/extra_vars.json') }}" | |||
| job_type: run | |||
| job_tags: "start,setup-all" | |||
| inventory: "{{ member_id }}" | |||
| project: "{{ member_id }} - Matrix Docker Ansible Deploy" | |||
| playbook: setup.yml | |||
| credential: "{{ member_id }} - AWX SSH Key" | |||
| survey_enabled: true | |||
| survey_spec: "{{ lookup('file', '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/configure_synapse_admin.json') }}" | |||
| become_enabled: true | |||
| state: present | |||
| verbosity: 1 | |||
| tower_host: "https://{{ awx_host }}" | |||
| tower_oauthtoken: "{{ awx_session_token.ansible_facts.tower_token.token }}" | |||
| validate_certs: true | |||
+ 0
- 32
roles/matrix-awx/tasks/update_variables.yml
Просмотреть файл
| @@ -1,32 +0,0 @@ | |||
| --- | |||
| - name: Rename synapse presence variable | |||
| delegate_to: 127.0.0.1 | |||
| replace: | |||
| path: "/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml" | |||
| regexp: 'matrix_synapse_use_presence' | |||
| replace: 'matrix_synapse_presence_enabled' | |||
| - name: Search for matrix_homeserver_generic_secret_key variable in matrix_vars.yml | |||
| delegate_to: 127.0.0.1 | |||
| register: presence | |||
| shell: "grep -i 'matrix_homeserver_generic_secret_key' /var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml" | |||
| no_log: true | |||
| - name: Generate matrix_homeserver_generic_secret_key variable if not present | |||
| delegate_to: 127.0.0.1 | |||
| command: | | |||
| openssl rand -hex 16 | |||
| register: generic_secret | |||
| no_log: true | |||
| when: presence is not changed | |||
| - name: Add new matrix_homeserver_generic_secret_key variable if not present | |||
| delegate_to: 127.0.0.1 | |||
| lineinfile: | |||
| path: '/var/lib/awx/projects/clients/{{ member_id }}/{{ subscription_id }}/matrix_vars.yml' | |||
| line: "matrix_homeserver_generic_secret_key: {{ generic_secret.stdout }}" | |||
| insertbefore: '# Basic Settings End' | |||
| mode: '0600' | |||
| state: present | |||
| when: presence is not changed | |||
+ 98
- 0
roles/matrix-backup-borg/defaults/main.yml
Просмотреть файл
| @@ -0,0 +1,98 @@ | |||
| --- | |||
| matrix_backup_borg_enabled: true | |||
| matrix_backup_borg_base_path: "{{ matrix_base_data_path }}/backup-borg" | |||
| matrix_backup_borg_config_path: "{{ matrix_backup_borg_base_path }}/config" | |||
| matrix_backup_borg_container_image_self_build: false | |||
| matrix_backup_borg_docker_repo: "https://gitlab.com/etke.cc/borgmatic" | |||
| matrix_backup_borg_docker_src_files_path: "{{ matrix_backup_borg_base_path }}/docker-src" | |||
| # version determined automatically, based on postgres server version (if enabled), otherwise latest is used | |||
| matrix_backup_borg_version: "" | |||
| matrix_backup_borg_docker_image: "{{ matrix_backup_borg_docker_image_name_prefix }}etke.cc/borgmatic:{{ matrix_backup_borg_version }}" | |||
| matrix_backup_borg_docker_image_name_prefix: "{{ 'localhost/' if matrix_backup_borg_container_image_self_build else 'registry.gitlab.com/' }}" | |||
| matrix_backup_borg_docker_image_force_pull: "{{ matrix_backup_borg_docker_image.endswith(':latest') or matrix_backup_borg_version|default('') == '' }}" | |||
| # A list of extra arguments to pass to the container | |||
| matrix_backup_borg_container_extra_arguments: [] | |||
| # List of systemd services that matrix-backup-borg.service depends on | |||
| matrix_backup_borg_systemd_required_services_list: ['docker.service'] | |||
| # List of systemd services that matrix-backup-borg.service wants | |||
| matrix_backup_borg_systemd_wanted_services_list: [] | |||
| # systemd calendar configuration for backup job | |||
| matrix_backup_borg_schedule: "*-*-* 04:00:00" | |||
| # what directories should be added to backup | |||
| matrix_backup_borg_location_source_directories: [] | |||
| # postgres db backup | |||
| matrix_backup_borg_postgresql_enabled: true | |||
| matrix_backup_borg_supported_postgres_versions: ['12', '13', '14'] | |||
| matrix_backup_borg_postgresql_databases: [] | |||
| matrix_backup_borg_postgresql_databases_hostname: "matrix-postgres" | |||
| matrix_backup_borg_postgresql_databases_username: "matrix" | |||
| matrix_backup_borg_postgresql_databases_password: "" | |||
| matrix_backup_borg_postgresql_databases_port: 5432 | |||
| # target repositories | |||
| matrix_backup_borg_location_repositories: [] | |||
| # exclude following paths: | |||
| matrix_backup_borg_location_exclude_patterns: [] | |||
| # borg encryption mode, only "repokey-*" and "none" are supported | |||
| matrix_backup_borg_encryption: repokey-blake2 | |||
| # private ssh key used to connect to the borg repo | |||
| matrix_backup_borg_ssh_key_private: "" | |||
| # allow unencrypted repo access | |||
| matrix_backup_borg_unknown_unencrypted_repo_access_is_ok: "{{ matrix_backup_borg_encryption == 'none' }}" | |||
| # borg ssh command with ssh key | |||
| matrix_backup_borg_storage_ssh_command: ssh -o "StrictHostKeyChecking accept-new" -i /etc/borgmatic.d/sshkey | |||
| # compression algorithm | |||
| matrix_backup_borg_storage_compression: lz4 | |||
| # archive name format | |||
| matrix_backup_borg_storage_archive_name_format: matrix-{now:%Y-%m-%d-%H%M%S} | |||
| # repository passphrase | |||
| matrix_backup_borg_storage_encryption_passphrase: "" | |||
| # retention configuration | |||
| matrix_backup_borg_retention_keep_hourly: 0 | |||
| matrix_backup_borg_retention_keep_daily: 7 | |||
| matrix_backup_borg_retention_keep_weekly: 4 | |||
| matrix_backup_borg_retention_keep_monthly: 12 | |||
| matrix_backup_borg_retention_keep_yearly: 2 | |||
| # retention prefix | |||
| matrix_backup_borg_retention_prefix: matrix- | |||
| # Default borgmatic configuration template which covers the generic use case. | |||
| # You can customize it by controlling the various variables inside it. | |||
| # | |||
| # For a more advanced customization, you can extend the default (see `matrix_backup_borg_configuration_extension_yaml`) | |||
| # or completely replace this variable with your own template. | |||
| matrix_backup_borg_configuration_yaml: "{{ lookup('template', 'templates/config.yaml.j2') }}" | |||
| matrix_backup_borg_configuration_extension_yaml: | | |||
| # Your custom YAML configuration for borgmatic goes here. | |||
| # This configuration extends the default starting configuration (`matrix_borg_configuration_yaml`). | |||
| # | |||
| # You can override individual variables from the default configuration, or introduce new ones. | |||
| # | |||
| # If you need something more special, you can take full control by | |||
| # completely redefining `matrix_backup_borg_configuration_yaml`. | |||
| matrix_backup_borg_configuration_extension: "{{ matrix_backup_borg_configuration_extension_yaml|from_yaml if matrix_backup_borg_configuration_extension_yaml|from_yaml is mapping else {} }}" | |||
| # Holds the final borgmatic configuration (a combination of the default and its extension). | |||
| # You most likely don't need to touch this variable. Instead, see `matrix_backup_borg_configuration_yaml`. | |||
| matrix_backup_borg_configuration: "{{ matrix_backup_borg_configuration_yaml|from_yaml|combine(matrix_backup_borg_configuration_extension, recursive=True) }}" | |||
+ 4
- 0
roles/matrix-backup-borg/tasks/init.yml
Просмотреть файл
| @@ -0,0 +1,4 @@ | |||
| --- | |||
| - set_fact: | |||
| matrix_systemd_services_list: "{{ matrix_systemd_services_list + ['matrix-backup-borg.timer'] }}" | |||
| when: matrix_backup_borg_enabled|bool | |||
+ 23
- 0
roles/matrix-backup-borg/tasks/main.yml
Просмотреть файл
| @@ -0,0 +1,23 @@ | |||
| --- | |||
| - import_tasks: "{{ role_path }}/tasks/init.yml" | |||
| tags: | |||
| - always | |||
| - import_tasks: "{{ role_path }}/tasks/validate_config.yml" | |||
| when: "run_setup|bool and matrix_backup_borg_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-backup-borg | |||
| - import_tasks: "{{ role_path }}/tasks/setup_install.yml" | |||
| when: "run_setup|bool and matrix_backup_borg_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-backup-borg | |||
| - import_tasks: "{{ role_path }}/tasks/setup_uninstall.yml" | |||
| when: "run_setup|bool and not matrix_backup_borg_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-backup-borg | |||
+ 112
- 0
roles/matrix-backup-borg/tasks/setup_install.yml
Просмотреть файл
| @@ -0,0 +1,112 @@ | |||
| --- | |||
| - block: | |||
| - import_tasks: "{{ role_path }}/../matrix-postgres/tasks/util/detect_existing_postgres_version.yml" | |||
| - name: Fail if detected Postgres version is unsupported | |||
| fail: | |||
| msg: "You cannot use borg backup with such an old version ({{ matrix_postgres_detected_version }}) of Postgres. Consider upgrading - link to docs for upgrading Postgres: docs/maintenance-postgres.md#upgrading-postgresql" | |||
| when: "matrix_postgres_detected_version not in matrix_backup_borg_supported_postgres_versions" | |||
| - name: Set the correct borg backup version to use | |||
| set_fact: | |||
| matrix_backup_borg_version: "{{ matrix_postgres_detected_version }}" | |||
| when: matrix_backup_borg_postgresql_enabled|bool and matrix_backup_borg_version == '' | |||
| - name: Ensure borg paths exist | |||
| file: | |||
| path: "{{ item.path }}" | |||
| state: directory | |||
| mode: 0750 | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| with_items: | |||
| - {path: "{{ matrix_backup_borg_config_path }}", when: true} | |||
| - {path: "{{ matrix_backup_borg_docker_src_files_path }}", when: true} | |||
| when: "item.when|bool" | |||
| - name: Ensure borgmatic config is created | |||
| copy: | |||
| content: "{{ matrix_backup_borg_configuration|to_nice_yaml(indent=2, width=999999) }}" | |||
| dest: "{{ matrix_backup_borg_config_path }}/config.yaml" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0640 | |||
| - name: Ensure borg passwd is created | |||
| template: | |||
| src: "{{ role_path }}/templates/passwd.j2" | |||
| dest: "{{ matrix_backup_borg_config_path }}/passwd" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0640 | |||
| - name: Ensure borg ssh key is created | |||
| template: | |||
| src: "{{ role_path }}/templates/sshkey.j2" | |||
| dest: "{{ matrix_backup_borg_config_path }}/sshkey" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0600 | |||
| - name: Ensure borg image is pulled | |||
| docker_image: | |||
| name: "{{ matrix_backup_borg_docker_image }}" | |||
| source: "{{ 'pull' if ansible_version.major > 2 or ansible_version.minor > 7 else omit }}" | |||
| force_source: "{{ matrix_backup_borg_docker_image_force_pull if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_backup_borg_docker_image_force_pull }}" | |||
| when: "not matrix_backup_borg_container_image_self_build|bool" | |||
| register: result | |||
| retries: "{{ matrix_container_retries_count }}" | |||
| delay: "{{ matrix_container_retries_delay }}" | |||
| until: result is not failed | |||
| - name: Ensure borg repository is present on self-build | |||
| git: | |||
| repo: "{{ matrix_backup_borg_docker_repo }}" | |||
| dest: "{{ matrix_backup_borg_docker_src_files_path }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_backup_borg_git_pull_results | |||
| when: "matrix_backup_borg_container_image_self_build|bool" | |||
| - name: Ensure borg image is built | |||
| docker_image: | |||
| name: "{{ matrix_backup_borg_docker_image }}" | |||
| source: build | |||
| force_source: "{{ matrix_backup_borg_git_pull_results.changed if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_mailer_git_pull_results.changed }}" | |||
| build: | |||
| dockerfile: Dockerfile | |||
| path: "{{ matrix_backup_borg_docker_src_files_path }}" | |||
| pull: true | |||
| when: "matrix_backup_borg_container_image_self_build|bool" | |||
| - name: Ensure matrix-backup-borg.service installed | |||
| template: | |||
| src: "{{ role_path }}/templates/systemd/matrix-backup-borg.service.j2" | |||
| dest: "{{ matrix_systemd_path }}/matrix-backup-borg.service" | |||
| mode: 0644 | |||
| register: matrix_backup_borg_systemd_service_result | |||
| - name: Ensure matrix-backup-borg.timer installed | |||
| template: | |||
| src: "{{ role_path }}/templates/systemd/matrix-backup-borg.timer.j2" | |||
| dest: "{{ matrix_systemd_path }}/matrix-backup-borg.timer" | |||
| mode: 0644 | |||
| register: matrix_backup_borg_systemd_timer_result | |||
| - name: Ensure systemd reloaded after matrix-backup-borg.service installation | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_backup_borg_systemd_service_result.changed|bool" | |||
| - name: Ensure matrix-backup-borg.service enabled | |||
| service: | |||
| enabled: true | |||
| name: matrix-backup-borg.service | |||
| - name: Ensure matrix-backup-borg.timer enabled | |||
| service: | |||
| enabled: true | |||
| name: matrix-backup-borg.timer | |||
+ 41
- 0
roles/matrix-backup-borg/tasks/setup_uninstall.yml
Просмотреть файл
| @@ -0,0 +1,41 @@ | |||
| --- | |||
| - name: Check existence of matrix-backup-borg service | |||
| stat: | |||
| path: "{{ matrix_systemd_path }}/matrix-backup-borg.service" | |||
| register: matrix_backup_borg_service_stat | |||
| - name: Ensure matrix-backup-borg is stopped | |||
| service: | |||
| name: matrix-backup-borg | |||
| state: stopped | |||
| enabled: false | |||
| daemon_reload: true | |||
| register: stopping_result | |||
| when: "matrix_backup_borg_service_stat.stat.exists|bool" | |||
| - name: Ensure matrix-backup-borg.service doesn't exist | |||
| file: | |||
| path: "{{ matrix_systemd_path }}/matrix-backup-borg.service" | |||
| state: absent | |||
| when: "matrix_backup_borg_service_stat.stat.exists|bool" | |||
| - name: Ensure matrix-backup-borg.timer doesn't exist | |||
| file: | |||
| path: "{{ matrix_systemd_path }}/matrix-backup-borg.timer" | |||
| state: absent | |||
| when: "matrix_backup_borg_service_stat.stat.exists|bool" | |||
| - name: Ensure systemd reloaded after matrix-backup-borg.service removal | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_backup_borg_service_stat.stat.exists|bool" | |||
| - name: Ensure Matrix borg paths don't exist | |||
| file: | |||
| path: "{{ matrix_backup_borg_base_path }}" | |||
| state: absent | |||
| - name: Ensure borg Docker image doesn't exist | |||
| docker_image: | |||
| name: "{{ matrix_backup_borg_docker_image }}" | |||
| state: absent | |||
+ 15
- 0
roles/matrix-backup-borg/tasks/validate_config.yml
Просмотреть файл
| @@ -0,0 +1,15 @@ | |||
| --- | |||
| - name: Fail if required settings not defined | |||
| fail: | |||
| msg: >- | |||
| You need to define a required configuration setting (`{{ item }}`). | |||
| when: "vars[item] == ''" | |||
| with_items: | |||
| - "matrix_backup_borg_ssh_key_private" | |||
| - "matrix_backup_borg_location_repositories" | |||
| - name: Fail if encryption passphrase is undefined unless repository is unencrypted | |||
| fail: | |||
| msg: >- | |||
| You need to define a required passphrase using the `matrix_backup_borg_storage_encryption_passphrase` variable. | |||
| when: "matrix_backup_borg_storage_encryption_passphrase == '' and matrix_backup_borg_encryption != 'none'" | |||
+ 43
- 0
roles/matrix-backup-borg/templates/config.yaml.j2
Просмотреть файл
| @@ -0,0 +1,43 @@ | |||
| #jinja2: lstrip_blocks: "True", trim_blocks: "True" | |||
| location: | |||
| source_directories: {{ matrix_backup_borg_location_source_directories|to_json }} | |||
| repositories: {{ matrix_backup_borg_location_repositories|to_json }} | |||
| one_file_system: true | |||
| exclude_patterns: {{ matrix_backup_borg_location_exclude_patterns|to_json }} | |||
| storage: | |||
| compression: {{ matrix_backup_borg_storage_compression|to_json }} | |||
| ssh_command: {{ matrix_backup_borg_storage_ssh_command|to_json }} | |||
| archive_name_format: {{ matrix_backup_borg_storage_archive_name_format|to_json }} | |||
| encryption_passphrase: {{ matrix_backup_borg_storage_encryption_passphrase|to_json }} | |||
| unknown_unencrypted_repo_access_is_ok: {{ matrix_backup_borg_unknown_unencrypted_repo_access_is_ok|to_json }} | |||
| retention: | |||
| keep_hourly: {{ matrix_backup_borg_retention_keep_hourly|to_json }} | |||
| keep_daily: {{ matrix_backup_borg_retention_keep_daily|to_json }} | |||
| keep_weekly: {{ matrix_backup_borg_retention_keep_weekly|to_json }} | |||
| keep_monthly: {{ matrix_backup_borg_retention_keep_monthly|to_json }} | |||
| keep_yearly: {{ matrix_backup_borg_retention_keep_yearly|to_json }} | |||
| prefix: {{ matrix_backup_borg_retention_prefix|to_json }} | |||
| consistency: | |||
| checks: | |||
| - repository | |||
| - archives | |||
| hooks: | |||
| {% if matrix_backup_borg_postgresql_enabled and matrix_backup_borg_postgresql_databases|length > 0 %} | |||
| postgresql_databases: | |||
| {% for database in matrix_backup_borg_postgresql_databases %} | |||
| - name: {{ database|to_json }} | |||
| hostname: {{ matrix_backup_borg_postgresql_databases_hostname|to_json }} | |||
| username: {{ matrix_backup_borg_postgresql_databases_username|to_json }} | |||
| password: {{ matrix_backup_borg_postgresql_databases_password|to_json }} | |||
| port: {{ matrix_backup_borg_postgresql_databases_port|to_json }} | |||
| {% endfor %} | |||
| {% endif %} | |||
| after_backup: | |||
| - echo "Backup created." | |||
| on_error: | |||
| - echo "Error while creating a backup." | |||
+ 29
- 0
roles/matrix-backup-borg/templates/passwd.j2
Просмотреть файл
| @@ -0,0 +1,29 @@ | |||
| {# the passwd file with correct username, UID and GID is mandatory to work with borg over ssh, otherwise ssh connections will fail #} | |||
| root:x:0:0:root:/root:/bin/ash | |||
| bin:x:1:1:bin:/bin:/sbin/nologin | |||
| daemon:x:2:2:daemon:/sbin:/sbin/nologin | |||
| adm:x:3:4:adm:/var/adm:/sbin/nologin | |||
| lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin | |||
| sync:x:5:0:sync:/sbin:/bin/sync | |||
| shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown | |||
| halt:x:7:0:halt:/sbin:/sbin/halt | |||
| mail:x:8:12:mail:/var/mail:/sbin/nologin | |||
| news:x:9:13:news:/usr/lib/news:/sbin/nologin | |||
| uucp:x:10:14:uucp:/var/spool/uucppublic:/sbin/nologin | |||
| operator:x:11:0:operator:/root:/sbin/nologin | |||
| man:x:13:15:man:/usr/man:/sbin/nologin | |||
| postmaster:x:14:12:postmaster:/var/mail:/sbin/nologin | |||
| cron:x:16:16:cron:/var/spool/cron:/sbin/nologin | |||
| ftp:x:21:21::/var/lib/ftp:/sbin/nologin | |||
| sshd:x:22:22:sshd:/dev/null:/sbin/nologin | |||
| at:x:25:25:at:/var/spool/cron/atjobs:/sbin/nologin | |||
| squid:x:31:31:Squid:/var/cache/squid:/sbin/nologin | |||
| xfs:x:33:33:X Font Server:/etc/X11/fs:/sbin/nologin | |||
| games:x:35:35:games:/usr/games:/sbin/nologin | |||
| cyrus:x:85:12::/usr/cyrus:/sbin/nologin | |||
| vpopmail:x:89:89::/var/vpopmail:/sbin/nologin | |||
| ntp:x:123:123:NTP:/var/empty:/sbin/nologin | |||
| smmsp:x:209:209:smmsp:/var/spool/mqueue:/sbin/nologin | |||
| guest:x:405:100:guest:/dev/null:/sbin/nologin | |||
| {{ matrix_user_username }}:x:{{ matrix_user_uid }}:{{ matrix_user_gid }}:Matrix:/tmp:/bin/ash | |||
| nobody:x:65534:65534:nobody:/:/sbin/nologin | |||
+ 1
- 0
roles/matrix-backup-borg/templates/sshkey.j2
Просмотреть файл
| @@ -0,0 +1 @@ | |||
| {{ matrix_backup_borg_ssh_key_private }} | |||
+ 58
- 0
roles/matrix-backup-borg/templates/systemd/matrix-backup-borg.service.j2
Просмотреть файл
| @@ -0,0 +1,58 @@ | |||
| #jinja2: lstrip_blocks: "True" | |||
| [Unit] | |||
| Description=Matrix Borg Backup | |||
| {% for service in matrix_backup_borg_systemd_required_services_list %} | |||
| Requires={{ service }} | |||
| After={{ service }} | |||
| {% endfor %} | |||
| {% for service in matrix_backup_borg_systemd_wanted_services_list %} | |||
| Wants={{ service }} | |||
| {% endfor %} | |||
| DefaultDependencies=no | |||
| [Service] | |||
| Type=oneshot | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-backup-borg 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-backup-borg 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_docker }} run --rm --name matrix-backup-borg \ | |||
| --log-driver=none \ | |||
| --cap-drop=ALL \ | |||
| --read-only \ | |||
| --user={{ matrix_user_uid }}:{{ matrix_user_gid }} \ | |||
| --network={{ matrix_docker_network }} \ | |||
| --tmpfs=/tmp:rw,noexec,nosuid,size=100m \ | |||
| --mount type=bind,src={{ matrix_backup_borg_config_path }}/passwd,dst=/etc/passwd,ro \ | |||
| --mount type=bind,src={{ matrix_backup_borg_config_path }},dst=/etc/borgmatic.d,ro \ | |||
| {% for source in matrix_backup_borg_location_source_directories %} | |||
| --mount type=bind,src={{ source }},dst={{ source }},ro \ | |||
| {% endfor %} | |||
| {% for arg in matrix_backup_borg_container_extra_arguments %} | |||
| {{ arg }} \ | |||
| {% endfor %} | |||
| {{ matrix_backup_borg_docker_image }} \ | |||
| sh -c "borgmatic --init --encryption {{ matrix_backup_borg_encryption }}" | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-backup-borg \ | |||
| --log-driver=none \ | |||
| --cap-drop=ALL \ | |||
| --read-only \ | |||
| --user={{ matrix_user_uid }}:{{ matrix_user_gid }} \ | |||
| --network={{ matrix_docker_network }} \ | |||
| --tmpfs=/tmp:rw,noexec,nosuid,size=100m \ | |||
| --mount type=bind,src={{ matrix_backup_borg_config_path }}/passwd,dst=/etc/passwd,ro \ | |||
| --mount type=bind,src={{ matrix_backup_borg_config_path }},dst=/etc/borgmatic.d,ro \ | |||
| {% for source in matrix_backup_borg_location_source_directories %} | |||
| --mount type=bind,src={{ source }},dst={{ source }},ro \ | |||
| {% endfor %} | |||
| {% for arg in matrix_backup_borg_container_extra_arguments %} | |||
| {{ arg }} \ | |||
| {% endfor %} | |||
| {{ matrix_backup_borg_docker_image }} | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-backup-borg 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-backup-borg 2>/dev/null || true' | |||
| SyslogIdentifier=matrix-backup-borg | |||
| [Install] | |||
| WantedBy=multi-user.target | |||
+ 10
- 0
roles/matrix-backup-borg/templates/systemd/matrix-backup-borg.timer.j2
Просмотреть файл
| @@ -0,0 +1,10 @@ | |||
| [Unit] | |||
| Description=Matrix Borg Backup timer | |||
| [Timer] | |||
| Unit=matrix-backup-borg.service | |||
| OnCalendar={{ matrix_backup_borg_schedule }} | |||
| RandomizedDelaySec=2h | |||
| [Install] | |||
| WantedBy=timers.target | |||
+ 7
- 0
roles/matrix-base/defaults/main.yml
Просмотреть файл
| @@ -37,6 +37,9 @@ matrix_server_fqn_hydrogen: "hydrogen.{{ matrix_domain }}" | |||
| # This is where you access the Cinny web client from (if enabled via matrix_client_cinny_enabled; disabled by default). | |||
| matrix_server_fqn_cinny: "cinny.{{ matrix_domain }}" | |||
| # This is where you access the buscarron bot from (if enabled via matrix_bot_buscarron_enabled; disabled by default). | |||
| matrix_server_fqn_buscarron: "buscarron.{{ matrix_domain }}" | |||
| # This is where you access the Dimension. | |||
| matrix_server_fqn_dimension: "dimension.{{ matrix_domain }}" | |||
| @@ -71,6 +74,10 @@ matrix_container_global_registry_prefix: "docker.io/" | |||
| matrix_container_retries_count: 10 | |||
| matrix_container_retries_delay: 10 | |||
| # Each get_url will retry on failed attempt 10 times with delay of 10 seconds between each attempt. | |||
| matrix_geturl_retries_count: 10 | |||
| matrix_geturl_retries_delay: 10 | |||
| matrix_user_username: "matrix" | |||
| matrix_user_groupname: "matrix" | |||
+ 96
- 0
roles/matrix-bot-buscarron/defaults/main.yml
Просмотреть файл
| @@ -0,0 +1,96 @@ | |||
| --- | |||
| # buscarron is a helpdesk bot | |||
| # See: https://gitlab.com/etke.cc/buscarron | |||
| matrix_bot_buscarron_enabled: true | |||
| matrix_bot_buscarron_container_image_self_build: false | |||
| matrix_bot_buscarron_docker_repo: "https://gitlab.com/etke.cc/buscarron.git" | |||
| matrix_bot_buscarron_docker_src_files_path: "{{ matrix_base_data_path }}/buscarron/docker-src" | |||
| matrix_bot_buscarron_version: v1.0.0 | |||
| matrix_bot_buscarron_docker_image: "{{ matrix_bot_buscarron_docker_image_name_prefix }}buscarron:{{ matrix_bot_buscarron_version }}" | |||
| matrix_bot_buscarron_docker_image_name_prefix: "{{ 'localhost/' if matrix_bot_buscarron_container_image_self_build else 'registry.gitlab.com/etke.cc/' }}" | |||
| matrix_bot_buscarron_docker_image_force_pull: "{{ matrix_bot_buscarron_docker_image.endswith(':latest') }}" | |||
| matrix_bot_buscarron_base_path: "{{ matrix_base_data_path }}/buscarron" | |||
| matrix_bot_buscarron_config_path: "{{ matrix_bot_buscarron_base_path }}/config" | |||
| matrix_bot_buscarron_data_path: "{{ matrix_bot_buscarron_base_path }}/data" | |||
| matrix_bot_buscarron_data_store_path: "{{ matrix_bot_buscarron_data_path }}/store" | |||
| # A list of extra arguments to pass to the container | |||
| matrix_bot_buscarron_container_extra_arguments: [] | |||
| # List of systemd services that matrix-bot-buscarron.service depends on | |||
| matrix_bot_buscarron_systemd_required_services_list: ['docker.service'] | |||
| # List of systemd services that matrix-bot-buscarron.service wants | |||
| matrix_bot_buscarron_systemd_wanted_services_list: [] | |||
| # Database-related configuration fields. | |||
| # | |||
| # To use SQLite, stick to these defaults. | |||
| # | |||
| # To use Postgres: | |||
| # - change the engine (`matrix_bot_buscarron_database_engine: 'postgres'`) | |||
| # - adjust your database credentials via the `matrix_bot_buscarron_database_*` variables | |||
| matrix_bot_buscarron_database_engine: 'sqlite' | |||
| matrix_bot_buscarron_sqlite_database_path_local: "{{ matrix_bot_buscarron_data_path }}/bot.db" | |||
| matrix_bot_buscarron_sqlite_database_path_in_container: "/data/bot.db" | |||
| matrix_bot_buscarron_database_username: 'buscarron' | |||
| matrix_bot_buscarron_database_password: 'some-password' | |||
| matrix_bot_buscarron_database_hostname: 'matrix-postgres' | |||
| matrix_bot_buscarron_database_port: 5432 | |||
| matrix_bot_buscarron_database_name: 'buscarron' | |||
| matrix_bot_buscarron_database_connection_string: 'postgres://{{ matrix_bot_buscarron_database_username }}:{{ matrix_bot_buscarron_database_password }}@{{ matrix_bot_buscarron_database_hostname }}:{{ matrix_bot_buscarron_database_port }}/{{ matrix_bot_buscarron_database_name }}?sslmode=disable' | |||
| matrix_bot_buscarron_storage_database: "{{ | |||
| { | |||
| 'sqlite': matrix_bot_buscarron_sqlite_database_path_in_container, | |||
| 'postgres': matrix_bot_buscarron_database_connection_string, | |||
| }[matrix_bot_buscarron_database_engine] | |||
| }}" | |||
| matrix_bot_buscarron_database_dialect: "{{ | |||
| { | |||
| 'sqlite': 'sqlite3', | |||
| 'postgres': 'postgres', | |||
| }[matrix_bot_buscarron_database_engine] | |||
| }}" | |||
| # The bot's username. This user needs to be created manually beforehand. | |||
| # Also see `matrix_bot_buscarron_password`. | |||
| matrix_bot_buscarron_login: "bot.buscarron" | |||
| # The password that the bot uses to authenticate. | |||
| matrix_bot_buscarron_password: '' | |||
| # the homeserver URL, uses internal synapse container address by default | |||
| matrix_bot_buscarron_homeserver: "{{ matrix_homeserver_container_url }}" | |||
| # forms configuration | |||
| matrix_bot_buscarron_forms: [] | |||
| # Sentry DSN | |||
| matrix_bot_buscarron_sentry: | |||
| # Log level | |||
| matrix_bot_buscarron_loglevel: INFO | |||
| # spam hosts/domains | |||
| matrix_bot_buscarron_spam_hosts: [] | |||
| # spam email addresses | |||
| matrix_bot_buscarron_spam_emails: [] | |||
| # Additional environment variables to pass to the buscarron container | |||
| # | |||
| # Example: | |||
| # matrix_bot_buscarron_environment_variables_extension: | | |||
| # BUSCARRON_LOGLEVEL=DEBUG | |||
| matrix_bot_buscarron_environment_variables_extension: '' | |||
+ 5
- 0
roles/matrix-bot-buscarron/tasks/init.yml
Просмотреть файл
| @@ -0,0 +1,5 @@ | |||
| --- | |||
| - set_fact: | |||
| matrix_systemd_services_list: "{{ matrix_systemd_services_list + ['matrix-bot-buscarron.service'] }}" | |||
| when: matrix_bot_buscarron_enabled|bool | |||
+ 23
- 0
roles/matrix-bot-buscarron/tasks/main.yml
Просмотреть файл
| @@ -0,0 +1,23 @@ | |||
| --- | |||
| - import_tasks: "{{ role_path }}/tasks/init.yml" | |||
| tags: | |||
| - always | |||
| - import_tasks: "{{ role_path }}/tasks/validate_config.yml" | |||
| when: "run_setup|bool and matrix_bot_buscarron_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-buscarron | |||
| - import_tasks: "{{ role_path }}/tasks/setup_install.yml" | |||
| when: "run_setup|bool and matrix_bot_buscarron_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-buscarron | |||
| - import_tasks: "{{ role_path }}/tasks/setup_uninstall.yml" | |||
| when: "run_setup|bool and not matrix_bot_buscarron_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-buscarron | |||
+ 100
- 0
roles/matrix-bot-buscarron/tasks/setup_install.yml
Просмотреть файл
| @@ -0,0 +1,100 @@ | |||
| --- | |||
| - set_fact: | |||
| matrix_bot_buscarron_requires_restart: false | |||
| - block: | |||
| - name: Check if an SQLite database already exists | |||
| stat: | |||
| path: "{{ matrix_bot_buscarron_sqlite_database_path_local }}" | |||
| register: matrix_bot_buscarron_sqlite_database_path_local_stat_result | |||
| - block: | |||
| - set_fact: | |||
| matrix_postgres_db_migration_request: | |||
| src: "{{ matrix_bot_buscarron_sqlite_database_path_local }}" | |||
| dst: "{{ matrix_bot_buscarron_database_connection_string }}" | |||
| caller: "{{ role_path|basename }}" | |||
| engine_variable_name: 'matrix_bot_buscarron_database_engine' | |||
| engine_old: 'sqlite' | |||
| systemd_services_to_stop: ['matrix-bot-buscarron.service'] | |||
| - import_tasks: "{{ role_path }}/../matrix-postgres/tasks/util/migrate_db_to_postgres.yml" | |||
| - set_fact: | |||
| matrix_bot_buscarron_requires_restart: true | |||
| when: "matrix_bot_buscarron_sqlite_database_path_local_stat_result.stat.exists|bool" | |||
| when: "matrix_bot_buscarron_database_engine == 'postgres'" | |||
| - name: Ensure buscarron paths exist | |||
| file: | |||
| path: "{{ item.path }}" | |||
| state: directory | |||
| mode: 0750 | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| with_items: | |||
| - {path: "{{ matrix_bot_buscarron_config_path }}", when: true} | |||
| - {path: "{{ matrix_bot_buscarron_data_path }}", when: true} | |||
| - {path: "{{ matrix_bot_buscarron_data_store_path }}", when: true} | |||
| - {path: "{{ matrix_bot_buscarron_docker_src_files_path }}", when: true} | |||
| when: "item.when|bool" | |||
| - name: Ensure buscarron environment variables file created | |||
| template: | |||
| src: "{{ role_path }}/templates/env.j2" | |||
| dest: "{{ matrix_bot_buscarron_config_path }}/env" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0640 | |||
| - name: Ensure buscarron image is pulled | |||
| docker_image: | |||
| name: "{{ matrix_bot_buscarron_docker_image }}" | |||
| source: "{{ 'pull' if ansible_version.major > 2 or ansible_version.minor > 7 else omit }}" | |||
| force_source: "{{ matrix_bot_buscarron_docker_image_force_pull if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_bot_buscarron_docker_image_force_pull }}" | |||
| when: "not matrix_bot_buscarron_container_image_self_build|bool" | |||
| register: result | |||
| retries: "{{ matrix_container_retries_count }}" | |||
| delay: "{{ matrix_container_retries_delay }}" | |||
| until: result is not failed | |||
| - name: Ensure buscarron repository is present on self-build | |||
| git: | |||
| repo: "{{ matrix_bot_buscarron_docker_repo }}" | |||
| dest: "{{ matrix_bot_buscarron_docker_src_files_path }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_bot_buscarron_git_pull_results | |||
| when: "matrix_bot_buscarron_container_image_self_build|bool" | |||
| - name: Ensure buscarron image is built | |||
| docker_image: | |||
| name: "{{ matrix_bot_buscarron_docker_image }}" | |||
| source: build | |||
| force_source: "{{ matrix_bot_buscarron_git_pull_results.changed if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_mailer_git_pull_results.changed }}" | |||
| build: | |||
| dockerfile: Dockerfile | |||
| path: "{{ matrix_bot_buscarron_docker_src_files_path }}" | |||
| pull: true | |||
| when: "matrix_bot_buscarron_container_image_self_build|bool" | |||
| - name: Ensure matrix-bot-buscarron.service installed | |||
| template: | |||
| src: "{{ role_path }}/templates/systemd/matrix-bot-buscarron.service.j2" | |||
| dest: "{{ matrix_systemd_path }}/matrix-bot-buscarron.service" | |||
| mode: 0644 | |||
| register: matrix_bot_buscarron_systemd_service_result | |||
| - name: Ensure systemd reloaded after matrix-bot-buscarron.service installation | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_bot_buscarron_systemd_service_result.changed|bool" | |||
| - name: Ensure matrix-bot-buscarron.service restarted, if necessary | |||
| service: | |||
| name: "matrix-bot-buscarron.service" | |||
| state: restarted | |||
| when: "matrix_bot_buscarron_requires_restart|bool" | |||
+ 36
- 0
roles/matrix-bot-buscarron/tasks/setup_uninstall.yml
Просмотреть файл
| @@ -0,0 +1,36 @@ | |||
| --- | |||
| - name: Check existence of matrix-buscarron service | |||
| stat: | |||
| path: "{{ matrix_systemd_path }}/matrix-bot-buscarron.service" | |||
| register: matrix_bot_buscarron_service_stat | |||
| - name: Ensure matrix-buscarron is stopped | |||
| service: | |||
| name: matrix-bot-buscarron | |||
| state: stopped | |||
| enabled: false | |||
| daemon_reload: true | |||
| register: stopping_result | |||
| when: "matrix_bot_buscarron_service_stat.stat.exists|bool" | |||
| - name: Ensure matrix-bot-buscarron.service doesn't exist | |||
| file: | |||
| path: "{{ matrix_systemd_path }}/matrix-bot-buscarron.service" | |||
| state: absent | |||
| when: "matrix_bot_buscarron_service_stat.stat.exists|bool" | |||
| - name: Ensure systemd reloaded after matrix-bot-buscarron.service removal | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_bot_buscarron_service_stat.stat.exists|bool" | |||
| - name: Ensure Matrix buscarron paths don't exist | |||
| file: | |||
| path: "{{ matrix_bot_buscarron_base_path }}" | |||
| state: absent | |||
| - name: Ensure buscarron Docker image doesn't exist | |||
| docker_image: | |||
| name: "{{ matrix_bot_buscarron_docker_image }}" | |||
| state: absent | |||
+ 9
- 0
roles/matrix-bot-buscarron/tasks/validate_config.yml
Просмотреть файл
| @@ -0,0 +1,9 @@ | |||
| --- | |||
| - name: Fail if required settings not defined | |||
| fail: | |||
| msg: >- | |||
| You need to define a required configuration setting (`{{ item }}`). | |||
| when: "vars[item] == ''" | |||
| with_items: | |||
| - "matrix_bot_buscarron_password" | |||
+ 19
- 0
roles/matrix-bot-buscarron/templates/env.j2
Просмотреть файл
| @@ -0,0 +1,19 @@ | |||
| BUSCARRON_LOGIN={{ matrix_bot_buscarron_login }} | |||
| BUSCARRON_PASSWORD={{ matrix_bot_buscarron_password }} | |||
| BUSCARRON_HOMESERVER={{ matrix_bot_buscarron_homeserver }} | |||
| BUSCARRON_DB_DSN={{ matrix_bot_buscarron_database_connection_string }} | |||
| BUSCARRON_DB_DIALECT={{ matrix_bot_buscarron_database_dialect }} | |||
| BUSCARRON_SPAM_HOSTS={{ matrix_bot_buscarron_spam_hosts|join(" ") }} | |||
| BUSCARRON_SPAM_EMAILS={{ matrix_bot_buscarron_spam_emails|join(" ") }} | |||
| BUSCARRON_SENTRY={{ matrix_bot_buscarron_sentry }} | |||
| BUSCARRON_LOGLEVEL={{ matrix_bot_buscarron_loglevel }} | |||
| {% set forms = [] %} | |||
| {% for form in matrix_bot_buscarron_forms -%}{{- forms.append(form.name) -}} | |||
| BUSCARRON_{{ form.name|upper }}_ROOM={{ form.room|default('') }} | |||
| BUSCARRON_{{ form.name|upper }}_REDIRECT={{ form.redirect|default('') }} | |||
| BUSCARRON_{{ form.name|upper }}_RATELIMIT={{ form.ratelimit|default('') }} | |||
| BUSCARRON_{{ form.name|upper }}_EXTENSIONS={{ form.extensions|default('')|join(' ') }} | |||
| {% endfor %} | |||
| BUSCARRON_LIST={{ forms|join(" ") }} | |||
| {{ matrix_bot_buscarron_environment_variables_extension }} | |||
+ 39
- 0
roles/matrix-bot-buscarron/templates/systemd/matrix-bot-buscarron.service.j2
Просмотреть файл
| @@ -0,0 +1,39 @@ | |||
| #jinja2: lstrip_blocks: "True" | |||
| [Unit] | |||
| Description=Matrix web forms bot | |||
| {% for service in matrix_bot_buscarron_systemd_required_services_list %} | |||
| Requires={{ service }} | |||
| After={{ service }} | |||
| {% endfor %} | |||
| {% for service in matrix_bot_buscarron_systemd_wanted_services_list %} | |||
| Wants={{ service }} | |||
| {% endfor %} | |||
| DefaultDependencies=no | |||
| [Service] | |||
| Type=simple | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-buscarron 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-buscarron 2>/dev/null || true' | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-buscarron \ | |||
| --log-driver=none \ | |||
| --user={{ matrix_user_uid }}:{{ matrix_user_gid }} \ | |||
| --cap-drop=ALL \ | |||
| --read-only \ | |||
| --network={{ matrix_docker_network }} \ | |||
| --env-file={{ matrix_bot_buscarron_config_path }}/env \ | |||
| --mount type=bind,src={{ matrix_bot_buscarron_data_path }},dst=/data \ | |||
| {% for arg in matrix_bot_buscarron_container_extra_arguments %} | |||
| {{ arg }} \ | |||
| {% endfor %} | |||
| {{ matrix_bot_buscarron_docker_image }} | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-buscarron 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-buscarron 2>/dev/null || true' | |||
| Restart=always | |||
| RestartSec=30 | |||
| SyslogIdentifier=matrix-bot-buscarron | |||
| [Install] | |||
| WantedBy=multi-user.target | |||
+ 4
- 4
roles/matrix-bot-go-neb/templates/systemd/matrix-bot-go-neb.service.j2
Просмотреть файл
| @@ -13,8 +13,8 @@ DefaultDependencies=no | |||
| [Service] | |||
| Type=simple | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-go-neb 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-go-neb 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-go-neb 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-go-neb 2>/dev/null || true' | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-go-neb \ | |||
| --log-driver=none \ | |||
| @@ -39,8 +39,8 @@ ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-go-neb \ | |||
| {{ matrix_bot_go_neb_docker_image }} \ | |||
| -c "go-neb /config/config.yaml" | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-go-neb 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-go-neb 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-go-neb 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-go-neb 2>/dev/null || true' | |||
| Restart=always | |||
| RestartSec=30 | |||
| SyslogIdentifier=matrix-bot-go-neb | |||
+ 10
- 1
roles/matrix-bot-honoroit/defaults/main.yml
Просмотреть файл
| @@ -8,7 +8,7 @@ matrix_bot_honoroit_container_image_self_build: false | |||
| matrix_bot_honoroit_docker_repo: "https://gitlab.com/etke.cc/honoroit.git" | |||
| matrix_bot_honoroit_docker_src_files_path: "{{ matrix_base_data_path }}/honoroit/docker-src" | |||
| matrix_bot_honoroit_version: v0.9.5 | |||
| matrix_bot_honoroit_version: v0.9.7 | |||
| matrix_bot_honoroit_docker_image: "{{ matrix_bot_honoroit_docker_image_name_prefix }}honoroit:{{ matrix_bot_honoroit_version }}" | |||
| matrix_bot_honoroit_docker_image_name_prefix: "{{ 'localhost/' if matrix_bot_honoroit_container_image_self_build else 'registry.gitlab.com/etke.cc/' }}" | |||
| matrix_bot_honoroit_docker_image_force_pull: "{{ matrix_bot_honoroit_docker_image.endswith(':latest') }}" | |||
| @@ -96,6 +96,15 @@ matrix_bot_honoroit_text_prefix_done: '' | |||
| # Text: greetings | |||
| matrix_bot_honoroit_text_greetings: '' | |||
| # Text: invite | |||
| matrix_bot_honoroit_text_invite: '' | |||
| # Text: join | |||
| matrix_bot_honoroit_text_join: '' | |||
| # Text: leave | |||
| matrix_bot_honoroit_text_leave: '' | |||
| # Text: error | |||
| matrix_bot_honoroit_text_error: '' | |||
+ 4
- 0
roles/matrix-bot-honoroit/tasks/setup_install.yml
Просмотреть файл
| @@ -43,6 +43,8 @@ | |||
| template: | |||
| src: "{{ role_path }}/templates/env.j2" | |||
| dest: "{{ matrix_bot_honoroit_config_path }}/env" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0640 | |||
| - name: Ensure honoroit image is pulled | |||
| @@ -62,6 +64,8 @@ | |||
| repo: "{{ matrix_bot_honoroit_docker_repo }}" | |||
| dest: "{{ matrix_bot_honoroit_docker_src_files_path }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_bot_honoroit_git_pull_results | |||
| when: "matrix_bot_honoroit_container_image_self_build|bool" | |||
+ 3
- 0
roles/matrix-bot-honoroit/templates/env.j2
Просмотреть файл
| @@ -11,6 +11,9 @@ HONOROIT_CACHESIZE={{ matrix_bot_honoroit_cachesize }} | |||
| HONOROIT_TEXT_PREFIX_OPEN={{ matrix_bot_honoroit_text_prefix_open }} | |||
| HONOROIT_TEXT_PREFIX_DONE={{ matrix_bot_honoroit_text_prefix_done }} | |||
| HONOROIT_TEXT_GREETINGS={{ matrix_bot_honoroit_text_greetings }} | |||
| HONOROIT_TEXT_INVITE={{ matrix_bot_honoroit_text_invite }} | |||
| HONOROIT_TEXT_JOIN={{ matrix_bot_honoroit_text_join }} | |||
| HONOROIT_TEXT_LEAVE={{ matrix_bot_honoroit_text_leave }} | |||
| HONOROIT_TEXT_ERROR={{ matrix_bot_honoroit_text_error }} | |||
| HONOROIT_TEXT_EMPTYROOM={{ matrix_bot_honoroit_text_emptyroom }} | |||
| HONOROIT_TEXT_DONE={{ matrix_bot_honoroit_text_done }} | |||
+ 4
- 4
roles/matrix-bot-honoroit/templates/systemd/matrix-bot-honoroit.service.j2
Просмотреть файл
| @@ -13,8 +13,8 @@ DefaultDependencies=no | |||
| [Service] | |||
| Type=simple | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-honoroit 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-honoroit 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-honoroit 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-honoroit 2>/dev/null || true' | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-honoroit \ | |||
| --log-driver=none \ | |||
| @@ -29,8 +29,8 @@ ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-honoroit \ | |||
| {% endfor %} | |||
| {{ matrix_bot_honoroit_docker_image }} | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-honoroit 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-honoroit 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-honoroit 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-honoroit 2>/dev/null || true' | |||
| Restart=always | |||
| RestartSec=30 | |||
| SyslogIdentifier=matrix-bot-honoroit | |||
+ 49
- 0
roles/matrix-bot-matrix-registration-bot/defaults/main.yml
Просмотреть файл
| @@ -0,0 +1,49 @@ | |||
| --- | |||
| # matrix-registration-bot creates and manages registration tokens for a matrix server | |||
| # See: https://github.com/moan0s/matrix-registration-bot | |||
| matrix_bot_matrix_registration_bot_enabled: true | |||
| matrix_bot_matrix_registration_bot_container_image_self_build: false | |||
| matrix_bot_matrix_registration_bot_docker_repo: "https://github.com/moan0s/matrix-registration-bot.git" | |||
| matrix_bot_matrix_registration_bot_docker_src_files_path: "{{ matrix_bot_matrix_registration_bot_base_path }}/docker-src" | |||
| matrix_bot_matrix_registration_bot_version: latest | |||
| matrix_bot_matrix_registration_bot_docker_image: "{{ matrix_container_global_registry_prefix }}moanos/matrix-registration-bot:{{ matrix_bot_matrix_registration_bot_version }}" | |||
| matrix_bot_matrix_registration_bot_docker_image_force_pull: "{{ matrix_bot_matrix_registration_bot_docker_image.endswith(':latest') }}" | |||
| matrix_bot_matrix_registration_bot_base_path: "{{ matrix_base_data_path }}/matrix-registration-bot" | |||
| matrix_bot_matrix_registration_bot_config_path: "{{ matrix_bot_matrix_registration_bot_base_path }}/config" | |||
| matrix_bot_matrix_registration_bot_data_path: "{{ matrix_bot_matrix_registration_bot_base_path }}/data" | |||
| matrix_bot_matrix_registration_bot_bot_server: "https://{{ matrix_server_fqn_matrix }}" | |||
| matrix_bot_matrix_registration_bot_api_base_url: "https://{{ matrix_server_fqn_matrix }}" | |||
| # The access token that the bot uses to communicate in Matrix chats | |||
| # This does not necessarily need to be a privileged (admin) access token. | |||
| matrix_bot_matrix_registration_bot_bot_access_token: '' | |||
| # The access token that the bot uses to call the Matrix API for creating registration tokens. | |||
| # This needs to be a privileged (admin) access token. | |||
| # By default, we assume `matrix_bot_matrix_registration_bot_bot_access_token` is such a privileged token and we use it as is. | |||
| # If necessary, you can define your own other access token here, which might even be for a different Matrix user. | |||
| matrix_bot_matrix_registration_bot_api_token: "{{ matrix_bot_matrix_registration_bot_bot_access_token }}" | |||
| matrix_bot_matrix_registration_bot_logging_level: info | |||
| matrix_bot_matrix_registration_environment_variables_extension: '' | |||
| # A list of extra arguments to pass to the container | |||
| matrix_bot_matrix_registration_bot_container_extra_arguments: [] | |||
| # List of systemd services that matrix-bot-matrix-registration-bot.service depends on | |||
| matrix_bot_matrix_registration_bot_systemd_required_services_list: ['docker.service'] | |||
| # List of systemd services that matrix-bot-matrix-registration-bot.service wants | |||
| matrix_bot_matrix_registration_bot_systemd_wanted_services_list: [] | |||
| # The bot's username. This user needs to be created manually beforehand. | |||
| # Also see `matrix_bot_matrix_registration_bot_user_password`. | |||
| matrix_bot_matrix_registration_bot_matrix_user_id_localpart: "bot.matrix-registration-bot" | |||
| matrix_bot_matrix_registration_bot_matrix_user_id: '@{{ matrix_bot_matrix_registration_bot_matrix_user_id_localpart }}:{{ matrix_domain }}' | |||
| matrix_bot_matrix_registration_bot_matrix_homeserver_url: "{{ matrix_homeserver_container_url }}" | |||
+ 5
- 0
roles/matrix-bot-matrix-registration-bot/tasks/init.yml
Просмотреть файл
| @@ -0,0 +1,5 @@ | |||
| --- | |||
| - set_fact: | |||
| matrix_systemd_services_list: "{{ matrix_systemd_services_list + ['matrix-bot-matrix-registration-bot.service'] }}" | |||
| when: matrix_bot_matrix_registration_bot_enabled|bool | |||
+ 23
- 0
roles/matrix-bot-matrix-registration-bot/tasks/main.yml
Просмотреть файл
| @@ -0,0 +1,23 @@ | |||
| --- | |||
| - import_tasks: "{{ role_path }}/tasks/init.yml" | |||
| tags: | |||
| - always | |||
| - import_tasks: "{{ role_path }}/tasks/validate_config.yml" | |||
| when: "run_setup|bool and matrix_bot_matrix_registration_bot_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-matrix-registration-bot | |||
| - import_tasks: "{{ role_path }}/tasks/setup_install.yml" | |||
| when: "run_setup|bool and matrix_bot_matrix_registration_bot_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-matrix-registration-bot | |||
| - import_tasks: "{{ role_path }}/tasks/setup_uninstall.yml" | |||
| when: "run_setup|bool and not matrix_bot_matrix_registration_bot_enabled|bool" | |||
| tags: | |||
| - setup-all | |||
| - setup-bot-matrix-registration-bot | |||
+ 73
- 0
roles/matrix-bot-matrix-registration-bot/tasks/setup_install.yml
Просмотреть файл
| @@ -0,0 +1,73 @@ | |||
| --- | |||
| - name: Ensure matrix-registration-bot paths exist | |||
| file: | |||
| path: "{{ item.path }}" | |||
| state: directory | |||
| mode: 0750 | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| with_items: | |||
| - {path: "{{ matrix_bot_matrix_registration_bot_config_path }}", when: true} | |||
| - - {path: "{{ matrix_bot_matrix_registration_bot_data_path }}", when: true} | |||
| - {path: "{{ matrix_bot_matrix_registration_bot_docker_src_files_path }}", when: true} | |||
| when: "item.when|bool" | |||
| - name: Ensure matrix-registration-bot configuration file created | |||
| template: | |||
| src: "{{ role_path }}/templates/config/config.yml.j2" | |||
| dest: "{{ matrix_bot_matrix_registration_bot_config_path }}/config.yml" | |||
| owner: "{{ matrix_user_username }}" | |||
| group: "{{ matrix_user_groupname }}" | |||
| mode: 0640 | |||
| - name: Ensure matrix-registration-bot image is pulled | |||
| docker_image: | |||
| name: "{{ matrix_bot_matrix_registration_bot_docker_image }}" | |||
| source: "{{ 'pull' if ansible_version.major > 2 or ansible_version.minor > 7 else omit }}" | |||
| force_source: "{{ matrix_bot_matrix_registration_bot_docker_image_force_pull if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_bot_matrix_registration_bot_docker_image_force_pull }}" | |||
| when: "not matrix_bot_matrix_registration_bot_container_image_self_build|bool" | |||
| register: result | |||
| retries: "{{ matrix_container_retries_count }}" | |||
| delay: "{{ matrix_container_retries_delay }}" | |||
| until: result is not failed | |||
| - name: Ensure matrix-registration-bot repository is present on self-build | |||
| git: | |||
| repo: "{{ matrix_bot_matrix_registration_bot_docker_repo }}" | |||
| dest: "{{ matrix_bot_matrix_registration_bot_docker_src_files_path }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_bot_matrix_registration_bot_git_pull_results | |||
| when: "matrix_bot_matrix_registration_bot_container_image_self_build|bool" | |||
| - name: Ensure matrix-registration-bot image is built | |||
| docker_image: | |||
| name: "{{ matrix_bot_matrix_registration_bot_docker_image }}" | |||
| source: build | |||
| force_source: "{{ matrix_bot_matrix_registration_bot_git_pull_results.changed if ansible_version.major > 2 or ansible_version.minor >= 8 else omit }}" | |||
| force: "{{ omit if ansible_version.major > 2 or ansible_version.minor >= 8 else matrix_mailer_git_pull_results.changed }}" | |||
| build: | |||
| dockerfile: Dockerfile | |||
| path: "{{ matrix_bot_matrix_registration_bot_docker_src_files_path }}" | |||
| pull: true | |||
| when: "matrix_bot_matrix_registration_bot_container_image_self_build|bool" | |||
| - name: Ensure matrix-bot-matrix-registration-bot.service installed | |||
| template: | |||
| src: "{{ role_path }}/templates/systemd/matrix-bot-matrix-registration-bot.service.j2" | |||
| dest: "{{ matrix_systemd_path }}/matrix-bot-matrix-registration-bot.service" | |||
| mode: 0644 | |||
| register: matrix_bot_matrix_registration_bot_systemd_service_result | |||
| - name: Ensure systemd reloaded after matrix-bot-matrix-registration-bot.service installation | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_bot_matrix_registration_bot_systemd_service_result.changed|bool" | |||
| - name: Ensure matrix-bot-matrix-registration-bot.service restarted, if necessary | |||
| service: | |||
| name: "matrix-bot-matrix-registration-bot.service" | |||
| state: restarted | |||
+ 36
- 0
roles/matrix-bot-matrix-registration-bot/tasks/setup_uninstall.yml
Просмотреть файл
| @@ -0,0 +1,36 @@ | |||
| --- | |||
| - name: Check existence of matrix-matrix-registration-bot service | |||
| stat: | |||
| path: "{{ matrix_systemd_path }}/matrix-bot-matrix-registration-bot.service" | |||
| register: matrix_bot_matrix_registration_bot_service_stat | |||
| - name: Ensure matrix-matrix-registration-bot is stopped | |||
| service: | |||
| name: matrix-bot-matrix-registration-bot | |||
| state: stopped | |||
| enabled: false | |||
| daemon_reload: true | |||
| register: stopping_result | |||
| when: "matrix_bot_matrix_registration_bot_service_stat.stat.exists|bool" | |||
| - name: Ensure matrix-bot-matrix-registration-bot.service doesn't exist | |||
| file: | |||
| path: "{{ matrix_systemd_path }}/matrix-bot-matrix-registration-bot.service" | |||
| state: absent | |||
| when: "matrix_bot_matrix_registration_bot_service_stat.stat.exists|bool" | |||
| - name: Ensure systemd reloaded after matrix-bot-matrix-registration-bot.service removal | |||
| service: | |||
| daemon_reload: true | |||
| when: "matrix_bot_matrix_registration_bot_service_stat.stat.exists|bool" | |||
| - name: Ensure Matrix matrix-registration-bot paths don't exist | |||
| file: | |||
| path: "{{ matrix_bot_matrix_registration_bot_base_path }}" | |||
| state: absent | |||
| - name: Ensure matrix-registration-bot Docker image doesn't exist | |||
| docker_image: | |||
| name: "{{ matrix_bot_matrix_registration_bot_docker_image }}" | |||
| state: absent | |||
+ 10
- 0
roles/matrix-bot-matrix-registration-bot/tasks/validate_config.yml
Просмотреть файл
| @@ -0,0 +1,10 @@ | |||
| --- | |||
| - name: Fail if required settings not defined | |||
| fail: | |||
| msg: >- | |||
| You need to define a required configuration setting (`{{ item }}`). | |||
| when: "vars[item] == ''" | |||
| with_items: | |||
| - "matrix_bot_matrix_registration_bot_bot_access_token" | |||
| - "matrix_bot_matrix_registration_bot_api_token" | |||
+ 12
- 0
roles/matrix-bot-matrix-registration-bot/templates/config/config.yml.j2
Просмотреть файл
| @@ -0,0 +1,12 @@ | |||
| bot: | |||
| server: {{ matrix_bot_matrix_registration_bot_bot_server|to_json }} | |||
| username: {{ matrix_bot_matrix_registration_bot_matrix_user_id_localpart|to_json }} | |||
| access_token: {{ matrix_bot_matrix_registration_bot_bot_access_token|to_json }} | |||
| api: | |||
| # API endpoint of the registration tokens | |||
| base_url: {{ matrix_bot_matrix_registration_bot_api_base_url|to_json }} | |||
| # Access token of an administrator on the server | |||
| token: {{ matrix_bot_matrix_registration_bot_api_token|to_json }} | |||
| logging: | |||
| level: {{ matrix_bot_matrix_registration_bot_logging_level|to_json }} | |||
+ 37
- 0
roles/matrix-bot-matrix-registration-bot/templates/systemd/matrix-bot-matrix-registration-bot.service.j2
Просмотреть файл
| @@ -0,0 +1,37 @@ | |||
| #jinja2: lstrip_blocks: "True" | |||
| [Unit] | |||
| Description=Matrix registration bot | |||
| {% for service in matrix_bot_matrix_registration_bot_systemd_required_services_list %} | |||
| Requires={{ service }} | |||
| After={{ service }} | |||
| {% endfor %} | |||
| {% for service in matrix_bot_matrix_registration_bot_systemd_wanted_services_list %} | |||
| Wants={{ service }} | |||
| {% endfor %} | |||
| DefaultDependencies=no | |||
| [Service] | |||
| Type=simple | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-registration-bot 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-registration-bot 2>/dev/null || true' | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-matrix-registration-bot \ | |||
| --log-driver=none \ | |||
| --cap-drop=ALL \ | |||
| -e "CONFIG_PATH=/config/config.yml" \ | |||
| --user={{ matrix_user_uid }}:{{ matrix_user_gid }} \ | |||
| --read-only \ | |||
| --mount type=bind,src={{ matrix_bot_matrix_registration_bot_config_path }},dst=/config,ro \ | |||
| --mount type=bind,src={{ matrix_bot_matrix_registration_bot_data_path }},dst=/data \ | |||
| --network={{ matrix_docker_network }} \ | |||
| {{ matrix_bot_matrix_registration_bot_docker_image }} | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-registration-bot 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-registration-bot 2>/dev/null || true' | |||
| Restart=always | |||
| RestartSec=30 | |||
| SyslogIdentifier=matrix-bot-matrix-registration-bot | |||
| [Install] | |||
| WantedBy=multi-user.target | |||
+ 2
- 0
roles/matrix-bot-matrix-reminder-bot/tasks/setup_install.yml
Просмотреть файл
| @@ -57,6 +57,8 @@ | |||
| repo: "{{ matrix_bot_matrix_reminder_bot_docker_repo }}" | |||
| dest: "{{ matrix_bot_matrix_reminder_bot_docker_src_files_path }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_bot_matrix_reminder_bot_git_pull_results | |||
| when: "matrix_bot_matrix_reminder_bot_container_image_self_build|bool" | |||
+ 4
- 4
roles/matrix-bot-matrix-reminder-bot/templates/systemd/matrix-bot-matrix-reminder-bot.service.j2
Просмотреть файл
| @@ -13,8 +13,8 @@ DefaultDependencies=no | |||
| [Service] | |||
| Type=simple | |||
| Environment="HOME={{ matrix_systemd_unit_home_path }}" | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-reminder-bot 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-reminder-bot 2>/dev/null' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-reminder-bot 2>/dev/null || true' | |||
| ExecStartPre=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-reminder-bot 2>/dev/null || true' | |||
| ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-matrix-reminder-bot \ | |||
| --log-driver=none \ | |||
| @@ -32,8 +32,8 @@ ExecStart={{ matrix_host_command_docker }} run --rm --name matrix-bot-matrix-rem | |||
| {{ matrix_bot_matrix_reminder_bot_docker_image }} \ | |||
| -c "matrix-reminder-bot /config/config.yaml" | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-reminder-bot 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-reminder-bot 2>/dev/null' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} kill matrix-bot-matrix-reminder-bot 2>/dev/null || true' | |||
| ExecStop=-{{ matrix_host_command_sh }} -c '{{ matrix_host_command_docker }} rm matrix-bot-matrix-reminder-bot 2>/dev/null || true' | |||
| Restart=always | |||
| RestartSec=30 | |||
| SyslogIdentifier=matrix-bot-matrix-reminder-bot | |||
+ 2
- 0
roles/matrix-bot-mjolnir/tasks/setup_install.yml
Просмотреть файл
| @@ -35,6 +35,8 @@ | |||
| dest: "{{ matrix_bot_mjolnir_docker_src_files_path }}" | |||
| version: "{{ matrix_bot_mjolnir_docker_image.split(':')[1] }}" | |||
| force: "yes" | |||
| become: true | |||
| become_user: "{{ matrix_user_username }}" | |||
| register: matrix_bot_mjolnir_git_pull_results | |||
| when: "matrix_bot_mjolnir_container_image_self_build|bool" | |||